Day 35: Mastering ConfigMaps and Secrets in Kubernetes🔒🔑🛡️
 Vaishnavi Shivde
Vaishnavi Shivde
In the world of Kubernetes (k8s), managing configuration and sensitive data efficiently is crucial. This is where ConfigMaps and Secrets come into play. Let's dive into what they are, how they differ, and why they're essential for your Kubernetes clusters.
What is a ConfigMap? 📜
A ConfigMap is a Kubernetes object used to store non-confidential data in key-value pairs. Here are some key points about ConfigMaps:
Purpose:
Designed to manage configuration data separately from the application code.
Facilitates the separation of configuration and runtime information.
Use Cases:
- Storing configuration files, environment variables, command-line arguments, and more.
Integration:
- Can be mounted as files or volumes, or exposed as environment variables to your pods.
Flexibility:
- Makes it easy to update the configuration without needing to rebuild your image or redeploy your application.
Example:
apiVersion: v1 kind: ConfigMap metadata: name: example-config data: config-key: config-value
What is a Secret? 🕵️♀️
A Secret is another Kubernetes object, but it is used to store sensitive information, such as passwords, OAuth tokens, and SSH keys. Here’s what you need to know about Secrets:
Purpose:
- Designed to store and manage sensitive information securely.
Encryption:
- Data stored in Secrets is base64-encoded and can be encrypted at rest using encryption providers.
Use Cases:
- Storing credentials, TLS certificates, API keys, and other confidential data.
Integration:
- Like ConfigMaps, Secrets can be mounted as volumes or exposed as environment variables.
Security:
- Access to Secrets is controlled via Kubernetes RBAC (Role-Based Access Control), ensuring only authorized entities can access sensitive data.
Example:
apiVersion: v1 kind: Secret metadata: name: example-secret type: Opaque data: username: dXNlcm5hbWU= # base64 encoded 'username' password: cGFzc3dvcmQ= # base64 encoded 'password'
Key Differences 🆚
Confidentiality:
ConfigMap: For non-sensitive data.
Secret: For sensitive data.
Data Encoding:
ConfigMap: Plain text.
Secret: Base64-encoded, can be encrypted at rest.
Use Cases:
ConfigMap: Application configuration, command-line arguments, etc.
Secret: Passwords, tokens, keys, etc.
Best Practices 🏅
Separation of Concerns: Use ConfigMaps for configuration data and Secrets for sensitive information.
Access Control: Leverage Kubernetes RBAC to limit access to Secrets.
Environment Variables: Be cautious when exposing Secrets via environment variables as they can be exposed through logs.
Encryption: Always enable encryption for Secrets at rest.
Regular Audits: Regularly audit access to both ConfigMaps and Secrets to ensure compliance and security.
Task 01: Create a ConfigMap for your Deployment
Create a ConfigMap for your Deployment.
apiVersion: v1 kind: ConfigMap metadata: name: mysql-cm namespace: mysql labels: app: mysql data: MYSQL_DATABASE: "cool-db"Update the deployment.yml file to include the ConfigMap
To use the ConfigMap in your deployment, you need to update the deployment.yml file to include the
envFromfield under thespec.containerssection. TheenvFromfield allows you to inject all the key-value pairs from the ConfigMap as environment variables into your containers.apiversion: apps/v1 kind: Deployment metadata: name: mysql-d namespace: mysql labels: app: mysql spec: replicas: 2 selector: matchLabels: app: mysql template: metadata: namespace: mysql labels: app: mysql spec: containers: - name: mysql image: mysql ports: - containerPort: 30006 env: - name: MYSQL_DATABASE valueFrom: configMapKeyRef: name: mysql-cm key: MYSQL_DATABASEApply deployment.yml file to k8s cluster
kubectl apply -f deployment.ymlVerify that the ConfigMap has been create
kubectl get configmapsYou should see something like this:
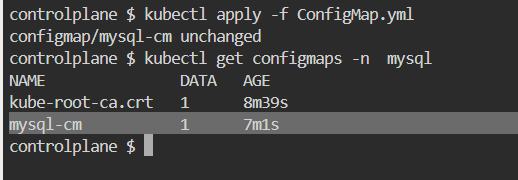
To inspect the details of a specific ConfigMap, you can use the
kubectl describe configmapcommand with the name of the ConfigMap. For example, you can run the following command:kubectl describe configmap mysql-cm -n mysqlYou should see something like this:
Task 02: Create a Secret for your Deployment
Create a Secret for your Deployment
apiVersion: v1 kind: Secret metadata: name: mysql-s namespace: mysql labels: app: mysql type: Opaque data: MYSQL_PASSWORD: "YXNraHNhcw=="Update the deployment.yml file to include the Secret
To use the Secret in your deployment, you need to update the deployment.yml file to include the env field under the
spec.containerssection. The env field allows you to inject specific key-value pairs from the Secret as environment variables into your containers.apiVersion: apps/v1 kind: Deployment metadata: name: mysql-d namespace: mysql labels: app: mysql spec: replicas: 2 selector: matchLabels: app: mysql template: metadata: namespace: mysql labels: app: mysql spec: containers: - name: mysql image: mysql ports: - containerPort: 30006 env: - name: MYSQL_DATABASE valueFrom: configMapKeyRef: name: mysql-cm key: MYSQL_DATABASE - name: MYSQL_PASSWORD valueFrom: secretKeyRef: name: mysql-s key: MYSQL_PASSWORDApply the updated deployment using the command:
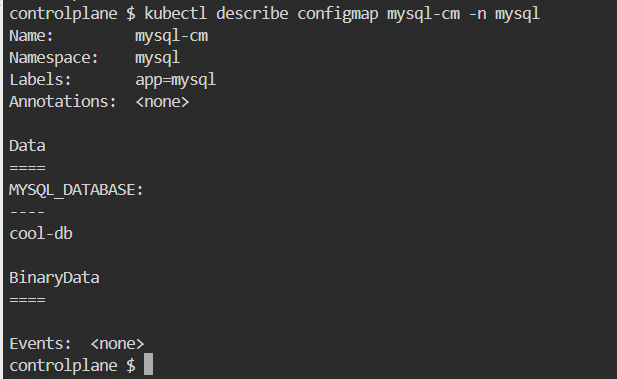
kubectl apply -f deployment.ymlVerify that the Secrets has been created.
kubectl get secrets -n mysqlYou should see something like this:
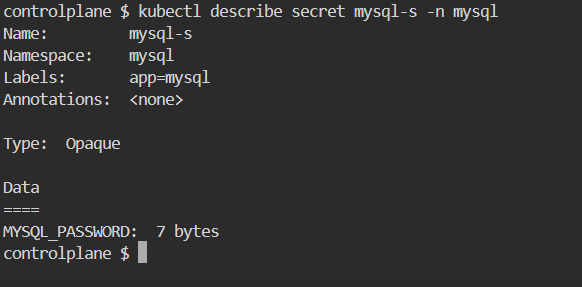
To inspect the details of a specific Secret, you can use the
kubectl describe secretcommand with the name of the Secret. For example, you can run the following command:kubectl describe secret mysql-s -n mysqlYou should see something like this:
Conclusion 🎯
ConfigMaps and Secrets are powerful tools in Kubernetes for managing configuration and sensitive data. By leveraging them appropriately, you can ensure that your applications are not only flexible and easy to manage but also secure. Happy k8s-ing! 🚀
Feel free to share your thoughts or any additional tips in the comments below! 😊
Subscribe to my newsletter
Read articles from Vaishnavi Shivde directly inside your inbox. Subscribe to the newsletter, and don't miss out.
Written by
Vaishnavi Shivde
Vaishnavi Shivde
Aspiring DevOps Engineer | Linux | Git & Github | Shell Scripting | Docker | CI/CD Jenkins | Kubernetes | AWS | Terraform | JIRA | Python |