Hackers Exploit ClickFix Technique to Deploy Havoc C2 Framework
 Dheelep
Dheelep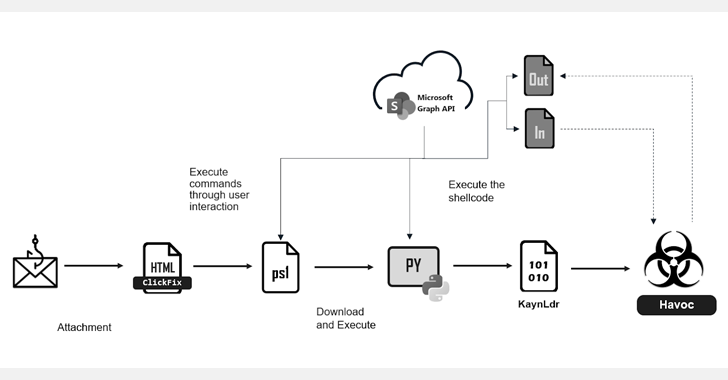
Cybersecurity researchers have uncovered a new phishing campaign that leverages the ClickFix trick to deploy the open-source command-and-control (C2) framework known as Havoc. This latest attack highlights the continued evolution of phishing tactics used by threat actors to infiltrate systems and maintain stealthy access.
Attack Chain Overview
The attack begins with a phishing email containing an HTML attachment named Documents.html. When the recipient opens this file, they are presented with a deceptive error message instructing them to copy and execute a PowerShell command in their terminal. If the user follows these instructions, the malicious payload is executed, setting off the infection chain.
Execution and Payload Deployment
Once the command is run, it downloads and executes a PowerShell script hosted on a compromised SharePoint server. The script performs an environment check to determine if it is running inside a sandbox or virtual machine, a common tactic used to evade detection. If the check is passed, the attack proceeds with the following steps:
Downloading and Installing Python: If Python is not installed on the victim’s system, the script downloads and runs pythonw.exe to ensure the required runtime is available.
Fetching and Executing a Python Script: The script then retrieves a secondary Python-based shellcode loader from the same SharePoint server.
Injecting Havoc C2: The loader deploys KaynLdr, a reflective loader written in C and Assembly, which injects the Havoc Demon agent into memory.
Stealthy C2 Communications
To evade detection, the attackers utilize Microsoft Graph API for C2 communications, allowing them to blend their malicious activity within legitimate network traffic. Havoc provides extensive post-exploitation capabilities, including:
System reconnaissance
File operations and data exfiltration
Command execution
Token manipulation
Kerberos attacks for lateral movement
Implications and Mitigation
This attack underscores the growing use of open-source offensive security tools by cybercriminals. The abuse of trusted cloud services like SharePoint and Microsoft Graph API makes detection more challenging for traditional security tools.
Mitigation Strategies:
User Awareness: Educate employees on phishing techniques and the dangers of executing unknown scripts.
Restrict PowerShell Usage: Implement application control policies to limit unauthorized execution of PowerShell scripts.
Monitor Network Traffic: Analyze outbound connections to detect anomalies related to cloud-based C2 communications.
Harden Email Security: Deploy email filtering solutions to block malicious attachments and links.
Final Thoughts
The ClickFix technique is another example of how attackers continually refine their methods to bypass security defenses. Organizations must adopt a multi-layered security approach to detect and prevent such threats effectively. By staying vigilant and implementing robust security practices, businesses can reduce the risk of falling victim to these increasingly sophisticated phishing attacks.
Stay updated on the latest cybersecurity threats and tactics at Blackout Protocol – We Trace the Untraceable. We Hunt the Undetected.
Subscribe to my newsletter
Read articles from Dheelep directly inside your inbox. Subscribe to the newsletter, and don't miss out.
Written by
