SMS Phishing and SMS 2FA Interception through 5G Downgrade and SS7 Protocol
 FPT Metrodata Indonesia
FPT Metrodata Indonesia
Summary
FMI Intelligence Teams came across multiple news outlets from multiple countries, such as Vietnam, Thailand, Indonesia, and Malaysia. The news outlets outline a trend in which threat actors utilize international mobile subscriber identity-catcher (IMSI-catcher) to conduct SMS Phishing (Smishing), as late as January 2025. This news also highlights an attack surface in the form of SMS 2FA interception through these tools, and vulnerability through downgrading of cellular protocol to a vulnerable 2G and SS7 protocol.
Technical Details
Cell-site simulators
Cell-site simulators, also known as Stingrays or IMSI catchers, are devices that masquerade as legitimate cell-phone towers, tricking phones within a certain radius into connecting to the device rather than a tower. Mobile phones are designed to connect to the cell site nearby with the strongest signal. To exploit this, cell-site simulators broadcast signals that are either stronger than the legitimate cell sites around them, or are made to appear stronger. This causes devices within range to disconnect from their service providers’ legitimate cell sites and to instead establish a new connection with the cell-site simulator.
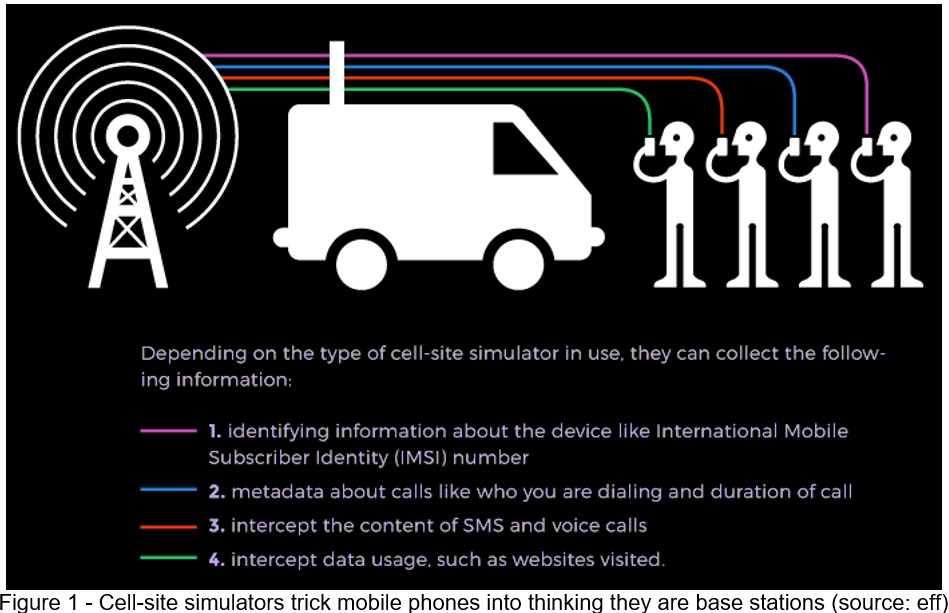
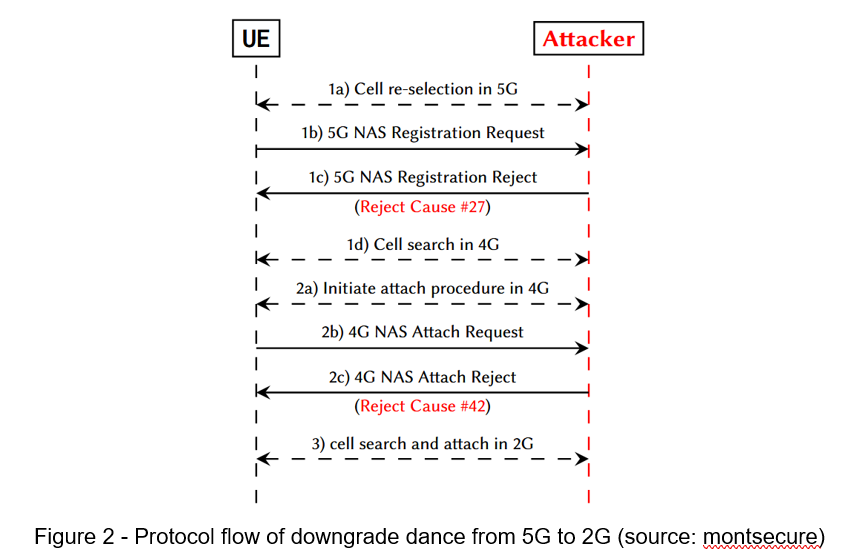
Once the mobile phones are connected, there are multiple methods to force the connection to a less secure standard. That can be weaker encryption algorithms or even connections using an older mobile generation. Such bidding-down attacks can be very diverse and use many different characteristics of a mobile connection, which makes it very difficult to simply protect against all of them. Once downgraded to 2G, the attacker can manipulate and eavesdrop on the entire connection as 2G offers no effective security mechanisms.
SMS man-in-the-middle
When a subscriber sends a SMS in a 2G network, communication between different equipment occurs thanks to the SS7 MAP (Mobile Application Part) protocol. The Mobile phone sends text to the Mobile Switching Centre (MSC, routing calls and SMS) in which it is currently located, with the recipient MSISDN (telephone number) and SMS Center (SMSC) address. The MSC sends the message and MSISDN to the SMSC that stores the message for delivery when possible. The SMSC contacts the HLR associated with the MSISDN to learn how to reach the recipient thanks to the MAP operation SendRoutingInfo_forShortMessage (SRI_SM). The HLR is the Home Location Register, a database which stores subscriber information about its current location and the subscription details. The HLR replies to the SMSC with the IMSI (International Mobile Subscriber Identifier) of the recipient and the MSC address where the recipient is located. The IMSI is a unique identifier used in SS7. When possible, the SMSC sends the message to the serving MSC which will forward it to the recipient.
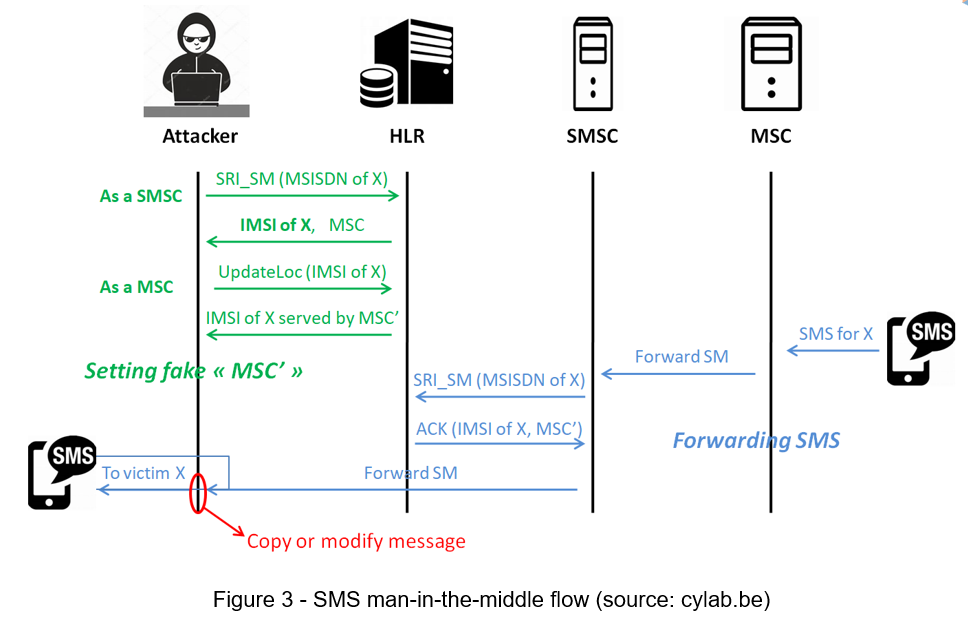
An attacker can have an access to the SS7 network, using some network equipment badly configured, buying a connection from a less scrupulous provider or from the black market, to name a few options. The attacker can impersonate as a SMSC and send a MAP SRI_SM message to the HLR of a targeted MSISDN to collect its IMSI and the address of its serving MSC. The HLR will reply since there is no equipment authentication in SS7. Then the attacker can pose as a MSC, providing for this an address that the attacker controls, and can send a MAP UpdateLocation operation. This will update the serving MSC associated with the victim MSISDN stored in the HLR. When a SMS is sent to the victim, it is forwarded to the MSC controlled by the attacker who can copy, modify and forward it to the actual recipient, realising a Man-In-The-Middle attack.
Why SS7 is vulnerable
Mobile networks started to evolve from the 1980’s around the SS7 stack of protocols designed in the 70’s, when national operators had little reason not to trust each other. In the mid 90’s, the number of network actors increased and hence the risks, due to the telecom deregulation (multiplication of providers) and the development of IP to offload the GSM traffic. About 10 years later, research groups started to report SS7 vulnerabilities and to demonstrate exploits such as location tracking, call or SMS interception and Denial of Service.
SS7 was designed with little concern about security. In 2G networks, the mobile phone is authenticated by a network thanks to its SIM card but the network is not. This leads for instance to the possibility to place fake antennas that can capture the radio traffic for mobile phones relatively close to the antenna.
Unfortunately, aside from the access network and its antennas, the core network is also prone to attacks. The mobility requirement in GSM led to the creation of a big network based on operator agreement to offer world-wide roaming. Here the biggest vulnerability is due to the lack of authentication of the network equipment. If an attacker has an entry point to the SS7 network, that attacker can impersonate some equipment to send requests to other network equipment world-wide. And nearly all requests are valid and not suspicious.
Recommendation
We have listed some essential cybersecurity best practices that create the first line of control against attackers. We recommend that our readers follow the best practices given below:
• The attack abused downgrading to 2G to utilize ss7; hence, it is advised to disable 2G on your mobile phone. Android 12 introduced a user option to disable 2G, first implemented by pixel phone, while iOS provides lockdown mode.
• Alternative methods to disable 2G on Android include utilizing dialing engineering mode secret code “*#*#4636#*#*”, and set preferred network type to “LTE/WCDMA” or “LTE Only” to disable 2G.
• Implement app-based 2FA solutions such as Google Authenticator, Authy, or Microsoft Authenticator. These apps generate time-based one-time passcodes (TOTP) that are not sent over the network, thus removing the risk of interception.
• For sensitive communication, consider using encrypted messaging apps like WhatsApp, Signal, or Telegram.
• Be cautious of suspicious emails, texts, or calls asking for personal information. Never click on links or download attachments from unknown sources.
Conclusion
IMSI-catcher leverages powerful broadcast signals to hijack cellular connection of mobile phones. Multiple methods are then available to downgrade connection protocol to 2G. Downgrading connection to 2G allows eavesdropping and tampering of communications, allowing broadcast of malicious SMS and interception of SMS 2FA. This capability highlights the risk of downgrading attacks, emphasizing the need to enforce secure communication channels.
Subscribe to my newsletter
Read articles from FPT Metrodata Indonesia directly inside your inbox. Subscribe to the newsletter, and don't miss out.
Written by

FPT Metrodata Indonesia
FPT Metrodata Indonesia
PT FPT Metrodata Indonesia (FMI) is a joint venture between FPT IS and Metrodata Electronics, focusing on providing Cybersecurity-as-a-Service—including SOC, managed security, professional services, consulting, and threat intelligence—to support Indonesia’s rapidly growing digital economy. FMI is expanding into AI and cloud GPU services to deliver innovative protection and solutions for enterprises. Learn more at https://fmisec.com.