DPRK-Linked Malware Campaign Targets Developers Through Fake Coding Challenges
 FPT Metrodata Indonesia
FPT Metrodata Indonesia
Summary
On September 3, 2024, the FBI issued a public service announcement to alert the crypto industry about a new threat: North Korea - officially known as the Democratic People’s Republic of Korea (DPRK) - is using sophisticated social engineering techniques to deliver malware. The agency noted that this state actor, with a well-documented history of generating illicit funds through cyberattacks, is now targeting specific individuals within cryptocurrency companies.
In line with these warnings, Jamf Threat Labs has been closely monitoring similar attack patterns. Their research indicates that most of these incidents begin when an attacker makes initial contact via social media, eventually leading to the deployment of malware. To further assist organizations in understanding and mitigating these risks, Jamf published a detailed blog outlining key insights and recommended defenses.
Techinal Details
The human element has long been regarded as the most vulnerable aspect of cybersecurity, and attackers continue to take advantage of this weakness through increasingly advanced social engineering tactics. These schemes frequently target individuals via professional networking platforms, making users both the first line of defense and the primary target.
According to the FBI’s announcement, threat actors conduct extensive reconnaissance before initiating contact. They carefully analyze a target’s social media presence, particularly on employment-related or professional networking sites.
Jamf Threat Labs recently observed an attack attempt in which a user was approached on LinkedIn by an individual posing as a recruiter from a decentralized finance technology company. A key red flag in this instance was that the profile had zero followers, suggesting it was recently created—an indicator often associated with fraudulent accounts.
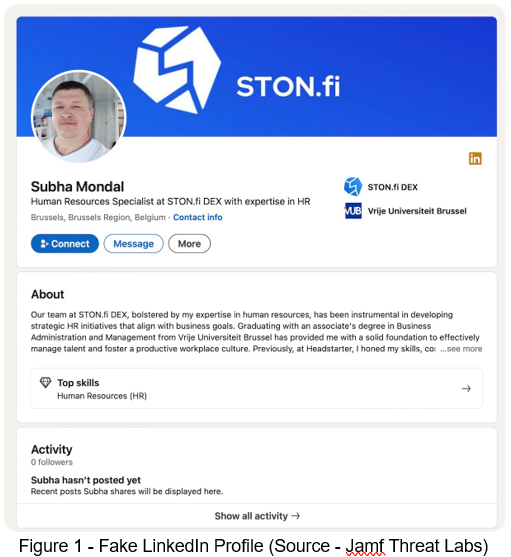
This aligns with the FBI’s findings, which highlight that these actors frequently masquerade as recruiters or representatives of tech companies, even going far enough to create professionallooking websites to bolster their credibility. While Jamf Threat Labs cannot verify the legitimacy of the website ston.fi, the recruiter's messaging appears to be strategically designed to engage the target’s interest.
The FBI’s announcement outlines several methods fraudsters use to trick victims into installing malware. One tactic observed by Jamf Threat Labs closely aligns with a documented attack scenario in the advisory.
In this case, a fake recruiter asked the target to complete a "pre-employment test," requiring them to execute non-standard Node.js or PyPI packages, scripts, or GitHub repositories. The attacker provided a zipped coding challenge (51a88646f9770e09b3505bd5cbadc587abb952ba), a common step in technical hiring processes.
The test was a Visual Studio project designed to convert Slack messages to CSV using C#. However, hidden within two separate .csproj files were malicious Bash commands. These commands, when executed, downloaded a second-stage payload, demonstrating how attackers weaponize seemingly legitimate hiring practices to distribute malware.
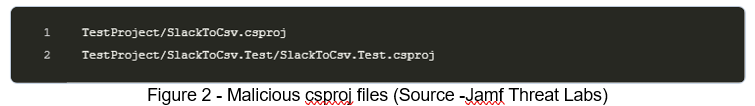
The Bash commands executed during the project build process include scripts that modify their
root directory before retrieving a second-stage payload using curl from taurihostmetrics[.]com.
Once downloaded, each payload is made executable, concealed, and then executed. These second-stage malware samples operate under different names—VisualStudioHelper, which communicates with wiresapplication[.]com, and zsh_env, which connects to juchesoviet48[.]com. Jamf Threat Labs has identified the second-stage malware deployed through this coding challenge as Thiefbucket, though it is also known in some circles as Rustdoor.
Based on the initial infection techniques and delivery methods observed, Jamf Threat Labs continues to attribute this malware to DPRK-affiliated threat actors, aligning with previously documented attack patterns.
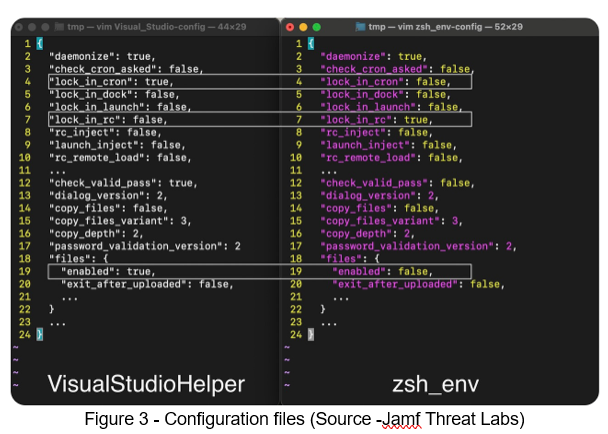
As previously discussed, the fake coding challenge delivers two executables that are nearly identical in functionality, differing primarily in their embedded configurations. The configuration files within these malware samples reveal distinct persistence mechanisms: VisualStudioHelper establishes persistence using a cron job, while zsh_env achieves persistence by modifying the zshrc file.
Additionally, within the configuration on line 19, VisualStudioHelper includes a setting labeled "files", which is enabled (true). This setting enables the malware to function as an infostealer, allowing it to collect various files specified within the configuration. To access high-value data, infostealers often require additional permissions. In this case, the malware circumvents restrictions by displaying a pop-up prompt, tricking users into granting the necessary privileges—this behavior is also preconfigured within the embedded settings.
The VisualStudioHelper payload is designed to deceive users by displaying a fake password prompt within Visual Studio, making it appear as a legitimate request during project builds. This increases the likelihood that the victim will unknowingly provide their credentials.
The second-stage malware, zsh_env, establishes persistence by modifying the .zshrc configuration. This ensures that whenever the user opens a zsh shell, the malware is executed in the background, leveraging the assumption that developers frequently use the Terminal. Both payloads function similarly but have distinct purposes. VisualStudioHelper acts as an infostealer and backdoor, capable of automated data theft and communication with wiresapplication[.]com. Meanwhile, zsh_env serves solely as a persistent backdoor, lacking automated data theft features, and connects to juchesoviet48[.]com for command and control.
Since its initial discovery, Thiefbucket has maintained several advanced capabilities, including automated data theft, file manipulation, process termination, and command execution. It can also prompt users with deceptive dialog boxes and establish persistence through multiple methods, such as LaunchAgents, cron jobs, and .zshrc modifications.
A notable change is that the malware, originally developed in Rust, has been rewritten in ObjectiveC. While Jamf Threat Labs continues to analyze feature differences, early findings suggest only minor modifications. The malware’s help page now includes additional arguments, primarily for testing and executing embedded configurations.
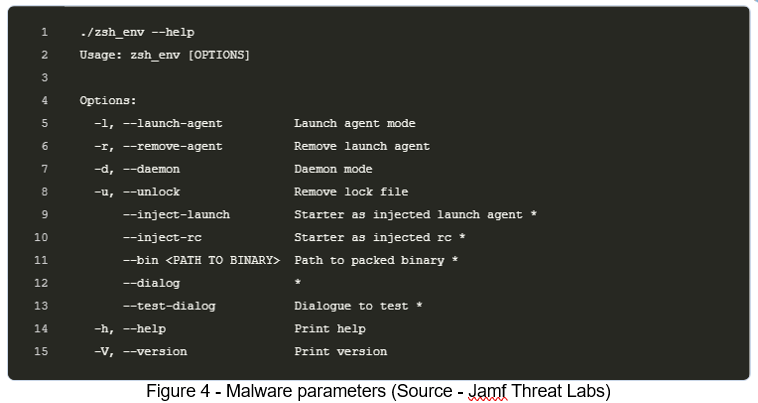
One key observation is that the VisualStudioHelper payload leverages the --dialog argument to prompt users for their passwords. Additionally, testing the --bin argument revealed that Thiefbucket adds a specified binary path to .zshrc before self-deleting, ensuring persistence while evading detection.
Conclusion
Threat actors persist in evolving their tactics to target individuals in the crypto industry. Jamf Threat Labs has observed attacks aligning with the FBI’s recent warning, highlighting the importance of cybersecurity awareness. Employees, particularly developers, should be cautious when engaging with unknown contacts on social media—especially those requesting them to execute software. The DPRK’s social engineering campaigns are highly sophisticated, often carried out by individuals fluent in English who conduct thorough research on their targets before initiating contact.
Organizations should prioritize security training to help employees recognize and resist these tactics. For a comprehensive list of recommended mitigations and best practices, reviewing the FBI’s public service announcement is highly advised.
Subscribe to my newsletter
Read articles from FPT Metrodata Indonesia directly inside your inbox. Subscribe to the newsletter, and don't miss out.
Written by

FPT Metrodata Indonesia
FPT Metrodata Indonesia
PT FPT Metrodata Indonesia (FMI) is a joint venture between FPT IS and Metrodata Electronics, focusing on providing Cybersecurity-as-a-Service—including SOC, managed security, professional services, consulting, and threat intelligence—to support Indonesia’s rapidly growing digital economy. FMI is expanding into AI and cloud GPU services to deliver innovative protection and solutions for enterprises. Learn more at https://fmisec.com.