TryHackMe's SOC Simulation Guide
 Joseph Chisom Ofonagoro
Joseph Chisom Ofonagoro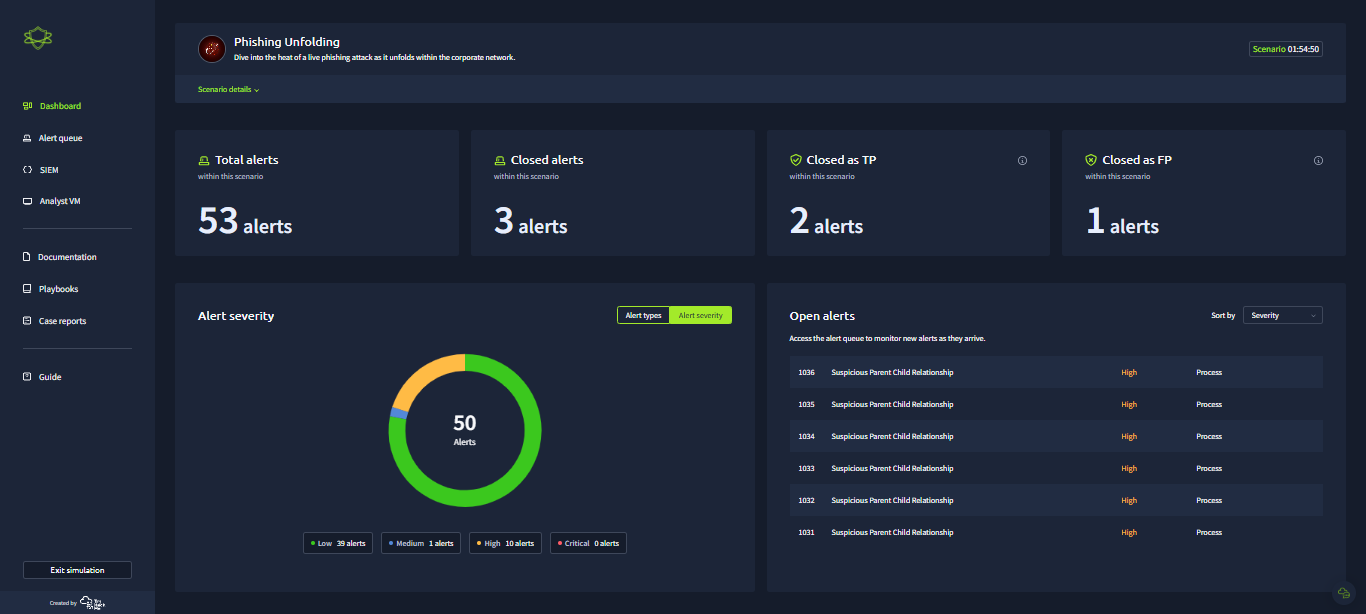
Introduction
If you are into cybersecurity, there are certain platforms that you should ideally be familiar with. One of such platforms is TryHackMe.
They offer lots of guides and practical labs sessions on different cybersecurity paths, and even a flow to get you started in the field.
In January this year, when I logged into my TryHackMe’s account, since I was on the SOC analysis path, I saw that they had added a new feature, which I believed was to be a game changer for SOC analysts using the platform. They now have a Simulated SOC Experience.
This was mind blowing for me that I quickly dived straight into it, and dived out no sooner than I had entered, because though it was tagged medium, prior to then, I had no experience nor coordinated knowledge of how a typical SOC works.
So, I went for more knowledge, watched a 3 hour live stream and came back, this time armed with the necessary know-how. I now knew what to do exactly, how the VM and SIEM tool worked, and I began my process which I am going to share with you.
The Actual SOC Experience.
When you click on the ‘Launch Simulator’ button, you will find different labs, they keep adding new ones with time, but the most popular, and I will say as the most useful for SOC analysts is the lab on Phishing Unfolding. It is the one we would be looking at in this article.
The Dashboard
Once you spin up your lab, you will be taken to your dashboard where you can get an overview of the threats that are being detected.
The dashboard is simply a super aggregator of data. It collects data from the SIEM, EDR, Firewalls and other security tools the organization uses, so you don’t need to jump from one end to the other. All you have to do is enter your dashboard and view them all. Don’t worry about configuring the dashboard as that is the job of the SOC engineer, but yeah, this is a lab, right? So no worries at all.
Here is how my SOC dashboard looked like:
By the left pane is the alert queue, where you can view all alerts in detail.
You can also find your SIEM, which takes you to Splunk enterprise, then your personalized Virtual Machine for running sample tests and investigating logs using Wireshark and any other tool that may have been made available to you.
If you are quite lost, you should consider reading the documentation and play books.
One fact about this lab that I love is that it is timed, which gives me that adrenaline. But, remember that you won’t be penalized for not hitting a certain number of triage after the timing is over, so you’ve got to focus more on accuracy. This is because the security of the network depends on how accurate your results are.
Remember that as a SOC analyst, you are the first level of defence any organization has.
The Alert Queue
Here is where you get very detailed information about each incident. This is also where you assign incidents to yourself.
Click the human avatar to assign an incident to yourself. When you do that, the incident will automatically be placed at the top of the page.
Note: You should assign incidents to yourself in descending order of severity. So, when there are five low severity incidents, two medium and one critical, assign the critical incident to yourself first and when you are done, you can proceed to the medium, or if any more critical incident pops up again, assign that one to yourself.
Once you have assigned an incident to yourself, click on the downwards arrow to view more information about it.
The information obtained will tell you if you are to head to the SIEM or VM first.
In this other image, you can see that we are supposed to head to our SIEM tool first because it has email as its datasource and it has no attachment.
Once you are done with your investigation, click the ‘Write Case report’ button and give as much information as you can. Remember that AI is going to score you at the end.
Here is a tip to help you write better case reports. I initially failed at it: Use the 5Ws of cybersecurity when writing your case report as it gives more detail to the person reading it.
SIEM
TryHackMe uses Splunk Enterprise to aggregate all incidents recorded within the network.
When you click the SIEM button, it takes you directly to Splunk. You can use Splunk search keywords to filter for particular events you are looking for.
Analyst VM
Your Virtual Machine allows you to analyse samples in a safe environment. It comes with all the required tools you will need to examine further.
The image below is that of a tool used to check for malware. These potential malware are stored in the VM from their original sources.
After you have done your diggings, write a case report on it and select if it requires escalation or not.
Here is my case report, but like I wrote earlier when I recommended that you use the 5Ws of cybersecurity, you can make it more detailed.
When your time is up, you’d automatically be scored.
I will share my score here:
These are just some of the scores I had. A brief explanation of this is that I was more accurate in flagging down true incidents than I was in flagging down false incidents. So, I most likely categorized some false alerts to be true, but my accuracy at catching true incidents as true was very high, which is great!
Summary
If I were to rate this SOC lab, on the aspect of its practicality, as with every other lab I have laid my hands on from TryHackMe, I would rate it a 100/100. Though I saw some technical issues, I believe that they are working on those bugs. I mean, it's pretty new, it requires some user feedback to become better and as soon as I publish this, I am sending them a message about an error I encountered with the VM.
To find the comprehensive report from TryHackMe to me on my First Ever Simulation, check here
You too can go check it out and add it to your resume! Viola!
Subscribe to my newsletter
Read articles from Joseph Chisom Ofonagoro directly inside your inbox. Subscribe to the newsletter, and don't miss out.
Written by

Joseph Chisom Ofonagoro
Joseph Chisom Ofonagoro
Hi there! I am a curious techie. My spare time is spent with books.