Deep Diving into Privacy Stack: A Roundup of everything Private from DeFi.
 Shivank Kapur
Shivank Kapur
Introduction
Privacy has become a fundamental concern in the evolving landscape of blockchain space. As public blockchains inherently expose transaction data, a robust privacy stack is essential to ensure financial confidentiality, data security, and communication protection.
All of us agree that when it comes to on-chain privacy, Ethereum Foundation is stepping up. However, let's face it, though, most individuals are unaware of the true meaning of on-chain privacy.
Reference: Click here to know about the recent changes in EF.
What information ought to be safeguarded? Which tools or programs assist you maintain your privacy? How to be protected from hacks? Which DApps one should not interact with? Privacy encompasses a whole stack and goes beyond infrastructure.
This article explores the key components of the privacy stack, from the DeFi and application layer to infrastructure and communication layers, and how they contribute to a more private and secure decentralized ecosystem.
Different Layers of Privacy
I'll describe the five layers of on-chain privacy, their significance, and user protection measures. Let's get started.
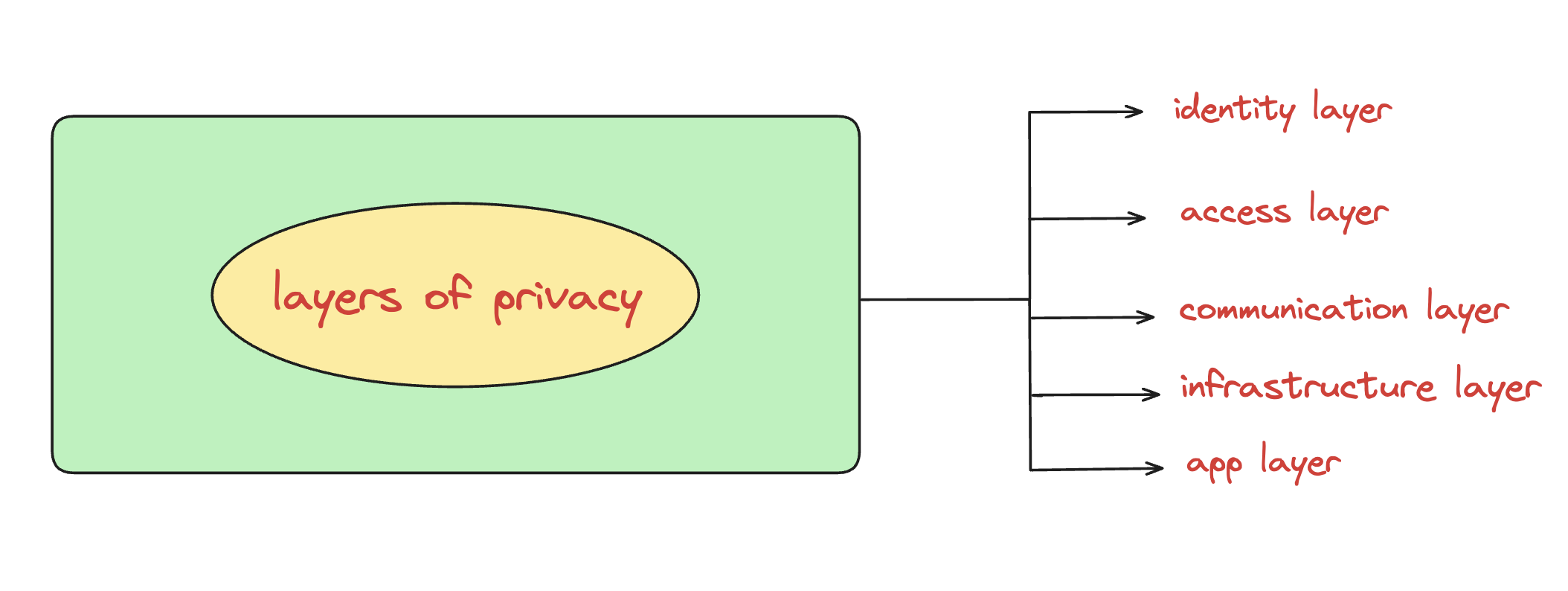
1. Identity Layer: Maintaining anonymity while transacting on-chain is crucial for protecting user identity. The Identify Layer focuses on how individuals can send and receive money while concealing their real-world identity and leveraging it for on-chain authentication. It includes key solutions such as - Stealth Addresses, Zero-Knowledge Proofs, Decentralized Identity (DID) Systems, etc.
2. Access Layer: Avoiding widespread monitoring while interacting with blockchain applications is essential for financial and data privacy. The Access Layer provides ways to interact with dApps while minimizing exposure. For example - Using Privacy-Preserving Wallets, Decentralized VPNs and Proxies, Private Bridges and Swaps, etc.
3. Communication Layer: The Communication Layer protects the confidentiality of transactions and user interactions, ensuring that messages and metadata remain private. For example - end-to-end encrypted messaging, RPC providers, etc.
4. Infrastructure Layer: The Infrastructure Layer covers the base protocols that ensure privacy across decentralized networks, from data storage to on-chain computation. For example - Decentralized Private Storage, Private Execution Environments, etc.
5. App Layer: The App Layer consists of privacy-enhancing applications that users can leverage today, as well as emerging projects that prioritize data confidentiality. For example - Privacy gaming, etc.
Identity Layer
This layer helps safeguard your identity even before you engage with dapps by allowing you to create accounts or identities for using on-chain applications. This can be further separated into two sections: anonymous fund transfers and on-chain private identity transmission.
A) On-chain Private DID (Decentralized Identity)
Solutions such as on-chain voting, on-chain event ticketing platforms, on-chain KYCs, and many more depend on the ability to verify users based on their real-world identities while maintaining the privacy of the data.
There are two additional components to this on-chain identity.
As an illustration, consider inference-able private DIDs, which can use shared private information to secretly respond to various queries depending on the necessary response. For example -
Is it a male?
Is the person from the US?
The alternative is a more strict approach that employs ZK to demonstrate ownership of a real-world identity or predetermined conditions while keeping all information private.
B) Stealth Accounts
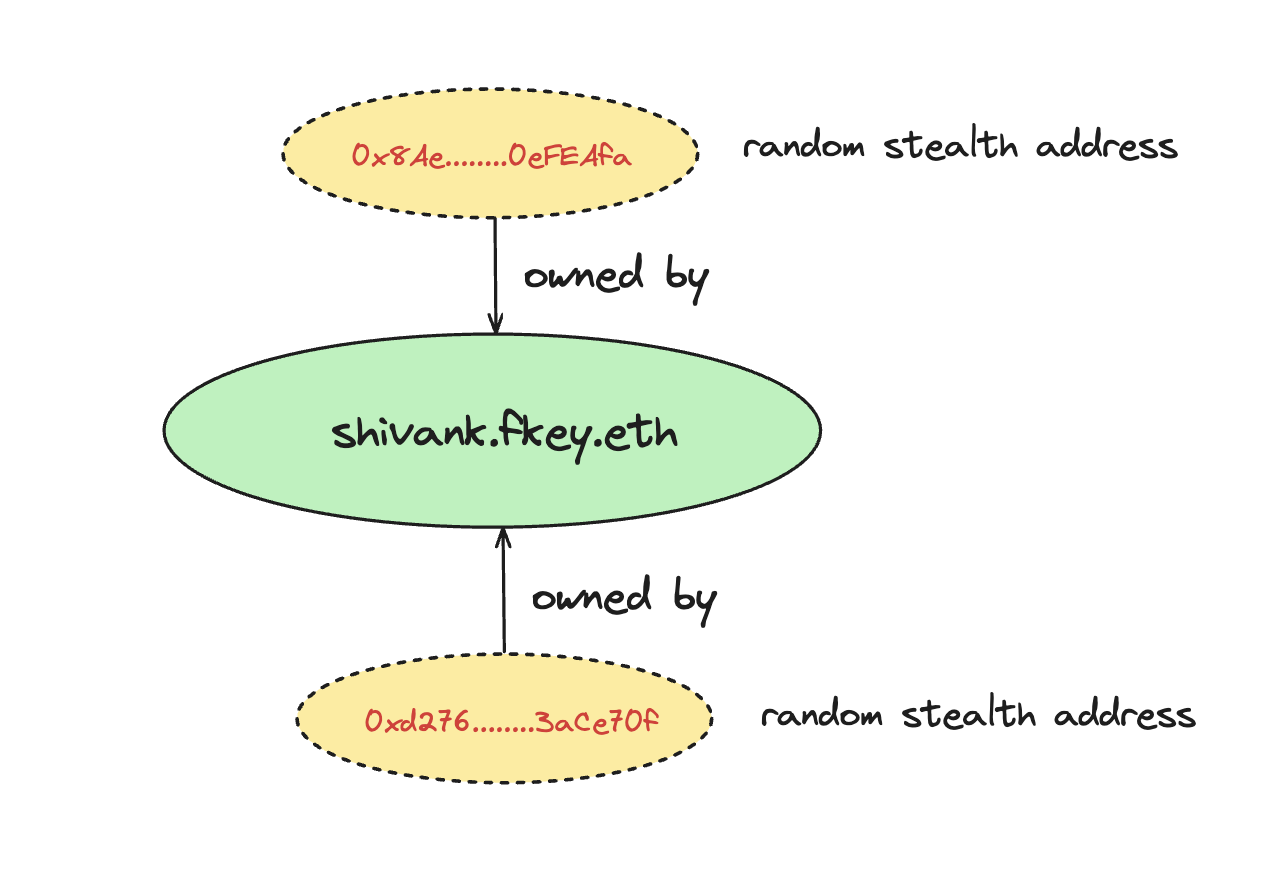
Historically, this has likely been the most popular on-chain private option.
Stealth addresses are addresses that are generated at random by the owner. Although the user owns these addresses, there is no connection between them and their on-chain accounts. Without publicly connecting these addresses to their own on-chain profile, they can use them to receive and manage funds on-chain.
However, there are a couple of UX-related issues in stealth addresses right now because it entails managing a large number of EOAs, managing stealth addresses as smart contract accounts, each controlled by random EOAs, is difficult. It gets more difficult to monitor these EOAs as stealth addresses increase. The majority of DeFi applications are made to only connect to one wallet at a time. For individuals who have money spread over several secret accounts, this presents an issue.
When someone wishes to trade money on a DeFi app, for instance, and has $500 USDC distributed among two distinct stealth addresses, the app might not be able to combine these balances for the transaction.
People have also been using Umbra Cash and fluidkey, which offer traceable but unlinkable stealth addresses to your primary wallets. A privacy solution that is both compliant and friendly.
Access Layer
Regarding what you disclose on-chain even before interacting with the blockchain, this layer is crucial, despite being one of the most misinterpreted and disregarded by on-chain users.
This includes wallets, VPNs, and browsers.
A) Browsers
Selecting a browser is crucial since it contains all of the information about the apps you are using as well as a lot more. In my opinion, Tor project and brave are good options.
B) VPNs
VPN users who think are having control over their privacy are in a big dilemma, because they are literally routing your data through a centralized server.
Below is a straightforward diagram that shows how your data is transmitted with a decentralised VPN, a centralised VPN, and no VPN. There are three types of VPNs - decentralised, centralised, and without.
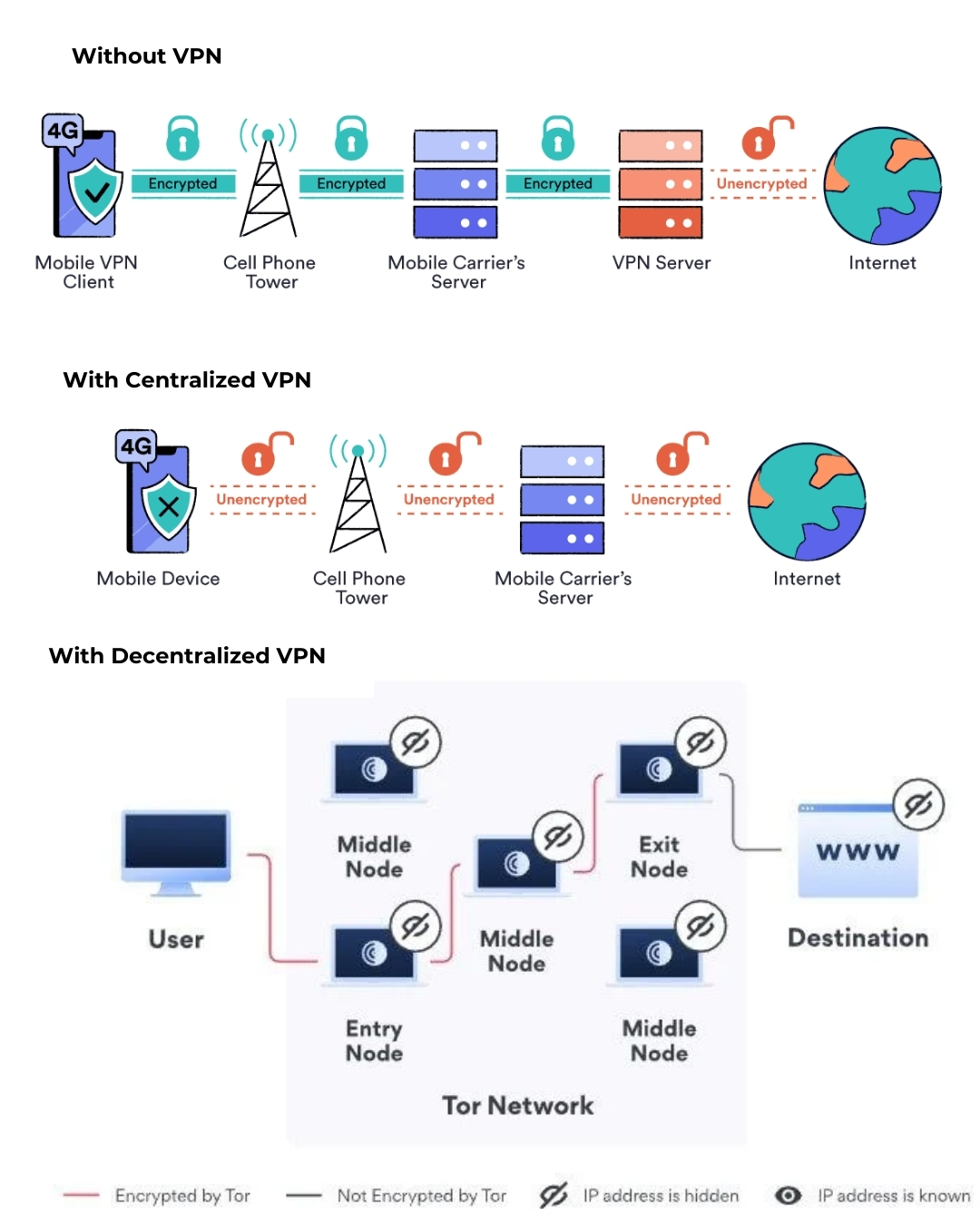
Orchid Protocol is one decentralised VPN provider. You don't need to utilise it if you're using any of the browser apps I listed because they come with built-in VPNs. However, if you use Chrome or another browser for any reason, you can use these VPNs to safeguard your privacy.
C) Wallets
Since most CEX wallets on your phone function similarly to standard Web2 apps, where your data is managed by centralised servers and databases, they jeopardise your data. You must have faith that they won't misuse or leak your information.
Private transactions are not automatically supported by other self-custodial wallets. One such example is the Wasabi Wallet which is designed for conducting confidential Bitcoin transactions. It relays transactions via TOR, which aggregates transactions from several users into a single transaction to help you keep your transfer amounts confidential.
Communication Layer
Till now in the above two layers we have covered the basics, but this is where on-chain privacy truly begins. Communication layer consists of a lot of parts but here we’re talking about only Messaging, RPC, etc.
A) P2P communication and messaging
Texting
The majority of conventional messaging apps make false claims about their privacy. Your data is used even if they provide end-to-end encryption. Have you ever mentioned your desire to buy anything to a friend on any social media app, only to be immediately followed by shoe advertisements on Instagram? While social networking and messaging share many similarities in terms of data protection, certain apps are designed with true privacy in mind.
An excellent instance of genuine end-to-end encrypted messaging is given by session app. In the meanwhile, wallet-to-wallet messaging infrastructure is provided by XMTP, which facilitates private communication between users through on-chain applications.
P2P Interaction
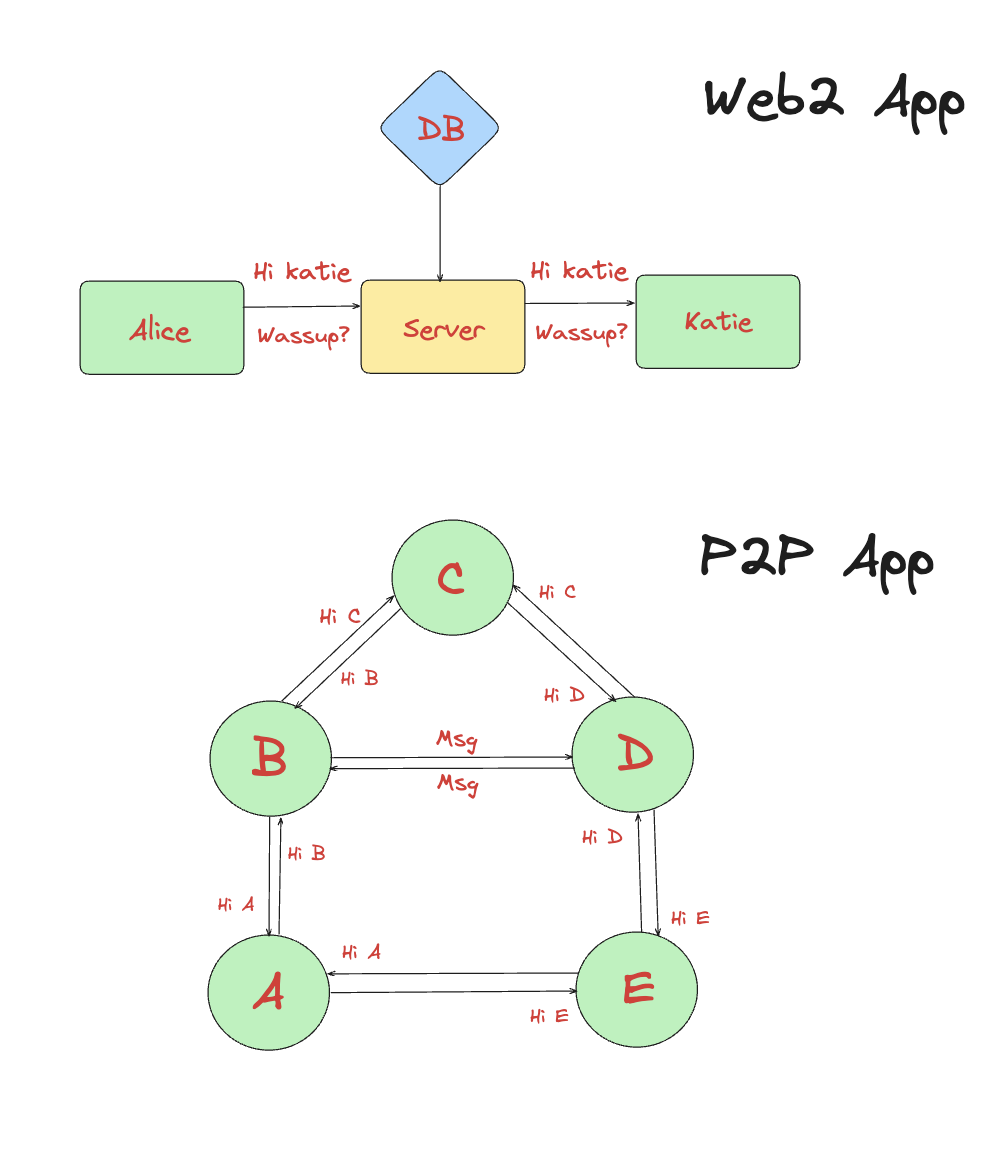
P2P apps are completely decentralised, allowing anyone to operate their own server for private communication, whereas the majority of social media apps use client-server architectures.
Decentralisation plus privacy equals real freedom.
B) Providers of RPC
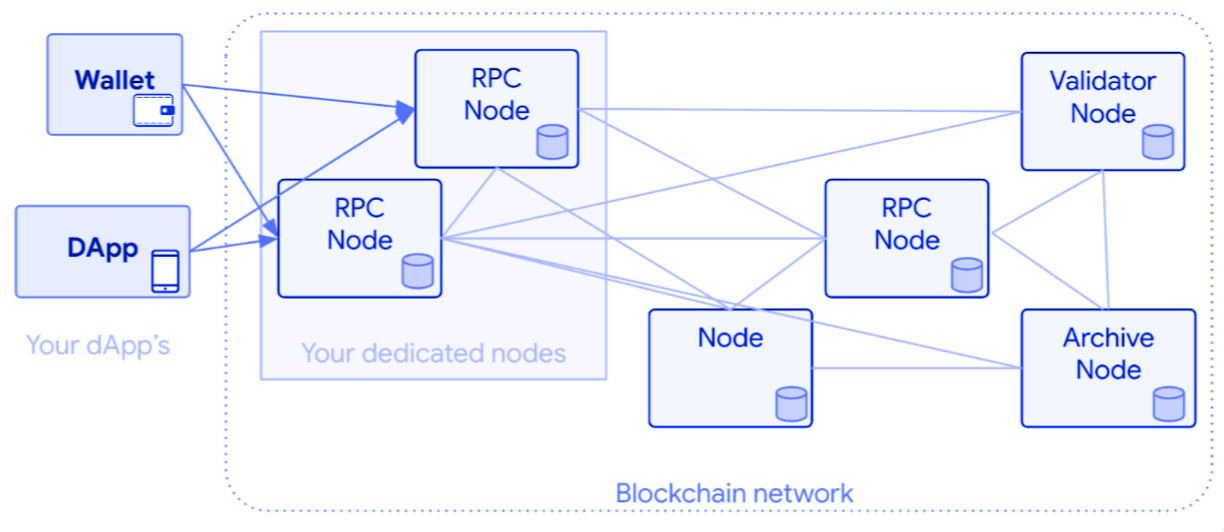
What is RPC?
A transaction is not sent straight to Ethereum after it is signed. Unless you are operating a whole node, that is not feasible. Rather, the majority of wallets relay your transactions on your behalf by using RPC providers.
The downside is that you could be vulnerable to MEV attacks when you transmit a transaction.
Additionally, each transaction you send includes metadata that includes details about your transaction. exposing every detail of consumers' on-chain interactions. An excellent illustration of what metadata looks like and what RPC providers actually view when they relay transactions for you.
Infrastructure Layer
This layer talks about the protocols or chains dealing with privacy as core infrastructure.
A) In light of what they offer
Privacy Blockchains
Native L1s and L2s with privacy by default are known as privacy blockchains. Aleph Zero, Polygon Miden, StarkEx, Taceo_io, Mind Network, Oasis, Partitia, Aztec, Ten, Fhenix, and Secret Network
Privacy-as-a-Service Providers for public blockchains
These services enhance the privacy of major L1s and L2s, Ethereum, Solana, and other public blockchain ecosystems, including INCO, Encipher, Nillion, Arcium, Lit Protocol, Fair Block, IKA, Fleek, Phala, and Automata.
Open-Source Privacy Tools, Storage, Support, and Solution Providers
Skiff & Fileverse - Storage options that prioritise privacy. Research-based companies, such as Zama & Sunscreen, are developing privacy infrastructure for various protocols, such as cryptographic techniques.
The eigen layer project for economic security is one that was developed for purposes other than privacy and is frequently utilised by infrastructure protocols. Users should be aware that an attack is only feasible if it is inexpensive enough to breach the security safeguarding the protocol, which is why I left it off of the ecosystem page.
B) Functioning based
These fall into three groups if we group them according to the technology and what it makes possible:
Composable Privacy
For untraceable anonymous apps (Rigid Privacy), ZK is the best option; for confidentiality with traceability, FHE, TEE, and MPC solutions are the best options.
zK-based solutions
ZK's effective verification, which enables users to demonstrate something is accurate without disclosing any underlying data, is another significant benefit.
Additionally, the majority of MPC, FHE, and TEE protocols still employ Zk.
Privacy focussed solutions
Storage with a privacy focus Users can safely store and exchange private data using encryption using fileverse, a decentralised storage service. NotionHQ purchased Skiff, a privacy-focused platform that provides storage to protect your data and end-to-end encrypted email.
App Layer
This is the last layer that uses privacy infrastructure to give end users privacy options.
A) Private DeFi
This includes dApps that enable DeFi applications to be confidential. Making private transactions on DEXs possible using ZKPanther & Railgun. Users can transfer public blockchain funds anonymously with Tornado Cash.
B) Management of Private Assets
The goal of private asset management is to protect privacy by facilitating private transactions and on-chain asset ownership. The CERC20 standard was introduced by circle and Inco, enabling users to encrypt ERC20 assets with private balances and transfers.
Through the integration of Stablecoin with fluidkey, which provides stealth addresses, confidential payments are made possible.
Usetoku declared that CERC20 would be supported for private payrolls. A secret RWA standard has been suggested by Inco under the ERC3643 organisation.
C) Private Governance
There are three ways that private governance allows users to vote on proposals in confidence -
Commit-and-reveal scheme: @UMAprotocol uses this.
The Aragon Project team developed two ZK-based private voting features that were deployed for nounsdao in order to provide on-chain private voting.
FHE-based private voting: Developed by tallyxyz with FHEVM, this feature enables users to conceal their voting preferences while still working with current governance systems.
Summary
Privacy is a critical concern in blockchain, as public networks inherently expose transaction data. A comprehensive privacy stack is essential to ensure financial confidentiality, data security, and communication protection. This article explores the five key layers of on-chain privacy:
Identity Layer – Focuses on maintaining anonymity while transacting. Solutions include Stealth Addresses, Zero-Knowledge Proofs (ZKPs), and Decentralized Identity (DID) Systems. It enables anonymous fund transfers and on-chain identity verification while preserving privacy.
Access Layer – Helps users interact with blockchain applications without exposing personal data. Tools such as privacy-preserving wallets, decentralized VPNs (dVPNs), and private bridges and swaps minimize surveillance and tracking risks.
Communication Layer – Ensures private messaging and metadata protection. End-to-end encrypted messaging, P2P interaction protocols, and RPC privacy enhancements prevent data leaks and protect sensitive information.
Infrastructure Layer – Comprises privacy-centric blockchain networks and cryptographic solutions. Privacy blockchains like Aleph Zero, Aztec, and Oasis and privacy-as-a-service providers such as Nillion and Lit Protocol help enhance security in public chains like Ethereum and Solana.
Application Layer – Includes privacy-enhancing dApps such as ZKPanther and Railgun for confidential DeFi transactions, Tornado Cash for anonymous transfers, and CERC20 for private asset management.
By leveraging these privacy layers, users can protect their identity, secure transactions, and interact with dApps without compromising personal information. The article highlights the need for stronger privacy tools as blockchain adoption grows.
Subscribe to my newsletter
Read articles from Shivank Kapur directly inside your inbox. Subscribe to the newsletter, and don't miss out.
Written by

Shivank Kapur
Shivank Kapur
I'm a FullStack Developer currently working with Technologies like MERN Stack, BlockChain, GraphQL, Next.js, LLMs, and a plethora of other cutting-edge tools. I'm working as a Developer Relations Engineering intern at Router Protocol and also as a Contributor at SuperteamDAO. My journey also encompasses past experiences at Push Protocol, where I orchestrated seamless community management strategies. I help Communities by Bridging the Gap between Developers and Clients. Crafting, launching, and meticulously documenting products fuel my passion, infusing every endeavor with purpose and precision. Beyond the binary, I find solace in the pages of self-help and spirituality, honing both mind and spirit with each turn of the page. phewww... I love a cup of coffee ☕ while writing code. So let's connect and have a meet over something you wanna discuss. I'll be more than happy to have it. Drop me a line at shivankkapur2004@gmail.com
