Satoshi Scoop Weekly, 21 Mar 2025
 Cryptape
CryptapeTable of contents
- Crypto Insights
- Dust UTXOs as Miner Transaction Fee
- Bitcoin Node P2P Traffic Analysis
- How Should Quantum-Recovered Bitcoin Be Handled
- Evaluation of Common Pathfinding Strategies in Lightning Network Clients
- A Solo Miner Finds a New Block with Minimal Hashrate
- Don’t Fear the Quantum Reaper
- A Noise-Free Roadmap of Secure and Efficient zkVMs
- Top Reads on Blockchain and Beyond
- Not Your Keys, Not Your Content: Rethinking Ownership in the Digital Age
- How to Avoid LinkedIn Recruitment Phishing Attacks
- Timeline for Bitcoin and the Rise of Cypherpunks
- Withdrawable Signatures in Fiat-Shamir with Aborts Constructions
- Diverse Paths of Practicing Web5 from a Socio-Technical Perspective
Crypto Insights
Dust UTXOs as Miner Transaction Fee
As Bitcoin's value and transaction fees rise, more UTXOs become unspendable because the cost of moving them exceeds their value. This leads to an increasing accumulation of dust UTXOs—small amounts of Bitcoin that can never circulate—causing continuous growth in the UTXO set.
To address this, the author has proposed a solution: using a special OP_RETURN output format to allow miners to claim dust UTXOs. Users can voluntarily designate their dust UTXOs as transaction fees through cryptographic authorization, allowing miners to claim them directly without requiring a traditional spend transaction. He believes this benefits users, miners, and the network: users regain value that would otherwise be stranded, miners earn additional fees, and the UTXO set's growth is alleviated.
Bitcoin Node P2P Traffic Analysis
By leveraging net:inbound_message and net:outbound_message tracepoints, the author analyzed TCP/IP traffic. In this article he details the methodology and shares the data collected.
Initially, this study aimed to determine what kind of bandwidth Erlay could save, but it was later discovered that the method and data could also benefit other P2P optimizations.
How Should Quantum-Recovered Bitcoin Be Handled
The Bitcoin community is divided on the ethical and technical considerations of recovering lost Bitcoin through quantum computing—an issue known as the "Quantum Recovery Debate." Some argue that allowing quantum-enabled recovery undermines Bitcoin's fundamental principles, while others believe it is inevitable.
Jameson Lopp is a vocal opponent of quantum recovery. He argues that permitting quantum-based Bitcoin recovery amounts to wealth redistribution, violating Bitcoin’s core principles of censorship resistance, transaction immutability, and conservatism. This form of redistribution would benefit only those with access to quantum computing. He warns that it could compromise Bitcoin’s security and trust without providing any real benefit. His proposed strategy is burning the vulnerable coins to prevent entities with quantum supremacy from claiming it.
Evaluation of Common Pathfinding Strategies in Lightning Network Clients
Sindura Saraswathi has published a study on various LN client pathfinding strategies, systematically analyzing single-path routing algorithms used in LND (Lightning Network Daemon), CLN (Core Lightning), LDK (Lightning Development Kit), and Eclair. The research compares their underlying channel weight functions, constraints, and properties of deployed algorithms, ultimately evaluating their performance and highlighting the strengths and weaknesses of each client variant. (Full paper)
A Solo Miner Finds a New Block with Minimal Hashrate
It is reported that another block has been mined solo. Block 887,212 was mined by solo ASIC miner Bitaxe through Solo CKPool, using the low-power open-source miner developed by D-Central Technologies. This is accomplished at a low hashrate of 552.49 EH/s. The probability of such a miner finding a block daily is less than one in a million—statistically, it would take around 3,500 years to mine a single block on average.
Don’t Fear the Quantum Reaper
Eli Ben-Sasson argues that zero-knowledge cryptographic solutions must be central to Bitcoin L2's quantum security, particularly zkSTARKs. Additionally, integrating quantum-resistant hash functions, such as stateless hash-based signatures (SPHINCS+), can defend against quantum computing threats. These functions resist Shor’s quantum attacks and use STARKs for scalable security. STARKs rely on strong hash functions rather than number-theoretic assumptions vulnerable to quantum attacks. This allows them to scale Bitcoin without redesigning its security model, making it inherently quantum-resistant.
To illustrate STARK’s uniqueness, he provides a clever analogy:
Your passwords today are akin to needles hidden in a gigantic haystack. Somebody could theoretically find your password by trying huge combinations of numbers, but it’s akin to finding that needle in the haystack. A quantum computer is like a huge magnet that can instantly find that needle. STARK cryptography is fundamentally different. Your password is no longer a magnetic needle in the haystack but a specific piece of hay in the massive haystack. No magnet will help you, and no quantum computer will find it. Even the modest powerful magnet in the world won’t find that hay and even the most powerful quantum computer won’t crack zkSTARK Proofs.
A Noise-Free Roadmap of Secure and Efficient zkVMs
The author argues that zkVMs, as highly complex software projects, are still in their infancy and face significant challenges in both security and performance. Besides a considerable number of bugs, zkVMs currently lack performance advantages—proving correct execution is significantly slower than local execution. Most zkVM applications are not practically viable today, and excessive hype and marketing spin make it difficult to assess real progress.
The author believes it will take years to achieve a secure and high-performance zkVM. To cut through the noise, he proposes a staged roadmap with clear security and performance milestones.
Top Reads on Blockchain and Beyond
Not Your Keys, Not Your Content: Rethinking Ownership in the Digital Age
The author highlights that much of the content accessible online isn’t truly owned by users—they are merely "subscribers." For example, Amazon recently disabled the "Download & Transfer via USB" feature for Kindle, meaning users can no longer manually transfer local eBooks, making access entirely dependent on Amazon’s cloud infrastructure. This raises questions about the meaning of ownership: simply possessing something isn’t enough. True ownership requires the ability to independently exercise your control and exclusivity over it.
How to Avoid LinkedIn Recruitment Phishing Attacks
@swader shared a personal case of experiencing a LinkedIn recruitment phishing attack. SlowMist analyzed this case in-depth and provided countermeasures for both individuals and companies.
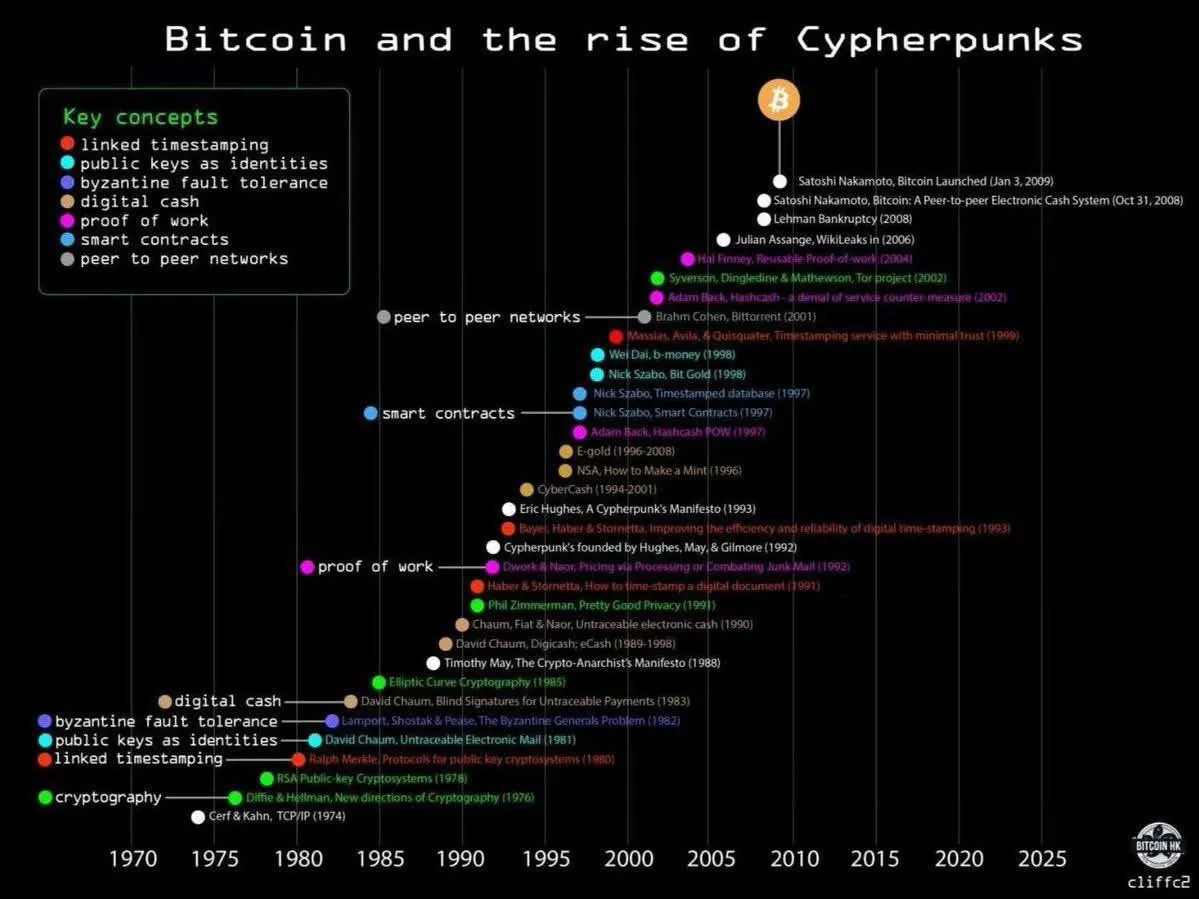
Timeline for Bitcoin and the Rise of Cypherpunks
Bitcoin’s evolution and the principles of the cypherpunk movement represent a fascinating intersection of cryptography, decentralized technology, and digital-age privacy and freedom. This timeline traces key milestones from the 1970s to the present, showcasing the gradual fusion of encryption, decentralized networks, and philosophical motivations for privacy and autonomy—culminating in Bitcoin’s launch on January 3, 2009.
Withdrawable Signatures in Fiat-Shamir with Aborts Constructions
The author proposes a new extension for revocable signatures under the Fiat-Shamir with aborts paradigm. By integrating Fiat-Shamir with aborts structures such as Dilithium or HAETAE, this work introduces a practical and secure approach within a post-quantum framework, opening up new possibilities for blockchain applications and beyond. The paper presents the abstract structure, security proofs, and a concrete construction for a withdrawable signature scheme based on Dilithium. (Full paper)
Diverse Paths of Practicing Web5 from a Socio-Technical Perspective
In this article, the author explores Web5—a new socio-technical paradigm integrating the strengths of Web2 and Web3—and how it redefines the relationship between technology and society. Adopting an socio-technical perspective, the article delves into the theoretical foundations of Web5 and uses a Village in Anhui, China, as a starting point for rural practice. It illustrates how Web5, as a form of edge innovation, can unfold across diverse domains, reconnecting technology with real societal needs and fostering an open, inclusive, and genuinely valuable technological ecosystem.
Subscribe to my newsletter
Read articles from Cryptape directly inside your inbox. Subscribe to the newsletter, and don't miss out.
Written by