Tracking Cyber Threats: What We Learned from 1,000,000 Leaked Credentials
 Alina
Alina
Credentials are among the most frequently targeted and easily monetized assets. Cybercriminals have found scalable, low-effort ways to harvest usernames, passwords, and session data through commodity infostealers that often go undetected until it’s too late. As organizations shift to hybrid work and expand their attack surfaces, the risk of credential exposure has never been more critical.
At Sentry Leak, we’ve spent the last few months analyzing a dataset of over 1,000,000 leaked credentials. These credentials were collected from sandbox detonations, Telegram leak channels, and dark web marketplaces. This early-stage threat intelligence exercise helped us better understand how data is stolen, where it goes, and how it’s reused by threat actors.
Here are some of the most striking takeaways from our research:
Password Reuse is Still Rampant
We found that over 20% of users reused the same or slightly modified passwords across multiple accounts. Even more alarming, around 8% of those reused passwords were tied to both personal and professional services—highlighting a dangerous practice where compromise of one account could lead to compromise of many others. Credential reuse across domains significantly expands the attack surface.
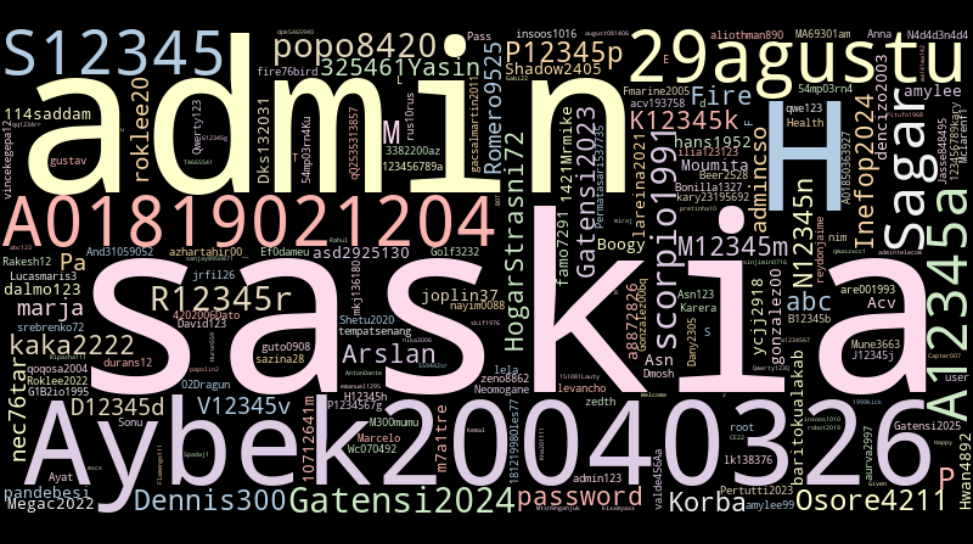
Figure 1: Word Clouds showing common Password.
Attackers leverage credential stuffing techniques by automatically testing leaked passwords against high-value platforms. Many infostealer logs include credentials from email services, SaaS platforms, VPN clients, and cloud services, giving attackers a variety of entry points.
Credential reuse also makes it easier for attackers to correlate identities. If a user uses the same email-password combo on ten different services, an attacker gains visibility into the victim’s digital footprint and can carry out targeted phishing or fraud schemes. This technique has been linked to account takeovers.
We also observed password patterns that followed predictable formats: simple dictionary words, appending numbers, or reusing base words with minor variations. This further enables brute-force and dictionary-based attacks, especially when combined with OSINT to identify target preferences.
Industries Most Targeted by Infostealers
By correlating domain names and service types tied to the stolen credentials, we were able to group them by industry. The top three most affected sectors were Technology (13.38%), Government (9.94%), and Social Media (7.04%). These sectors not only represent a wide attack surface but also often rely on externally accessible services, making them prime targets for infostealer campaigns.
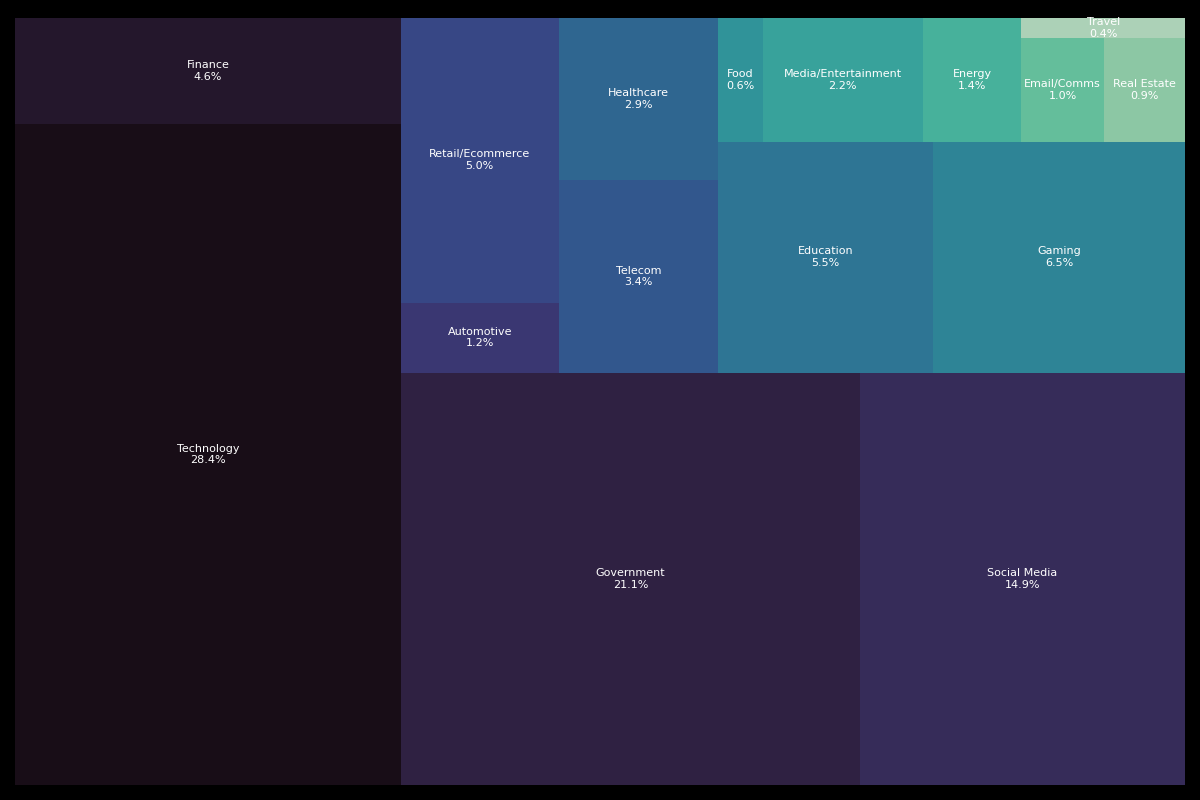
Figure 2: Sector heatmap
The Technology sector includes cloud platforms, developer tools, and digital services, all of which are integral to business infrastructure. Credential compromise in this space could lead to source code theft, unauthorized infrastructure access, or abuse of CI/CD pipelines. Government-related domains, the second most impacted, include ministries, municipal platforms, and other public services—often under-protected despite being high-value targets for espionage and ransomware. The Social Media sector, which ranked third, continues to be exploited for identity theft, account takeover, and influence operations.
Telegram is the New Dark Web
While traditional dark web marketplaces and forums are still operational, a notable shift is happening in how cybercriminals distribute and monetize stolen credentials. Telegram's built-in encryption, group structure, and bot functionality make it an ideal platform for cybercriminals. We observed dozens of channels using bots to automatically distribute logs, allowing buyers to filter by domain, keyword, or service type. These bots make stolen credentials accessible at scale, democratizing access to compromised data.
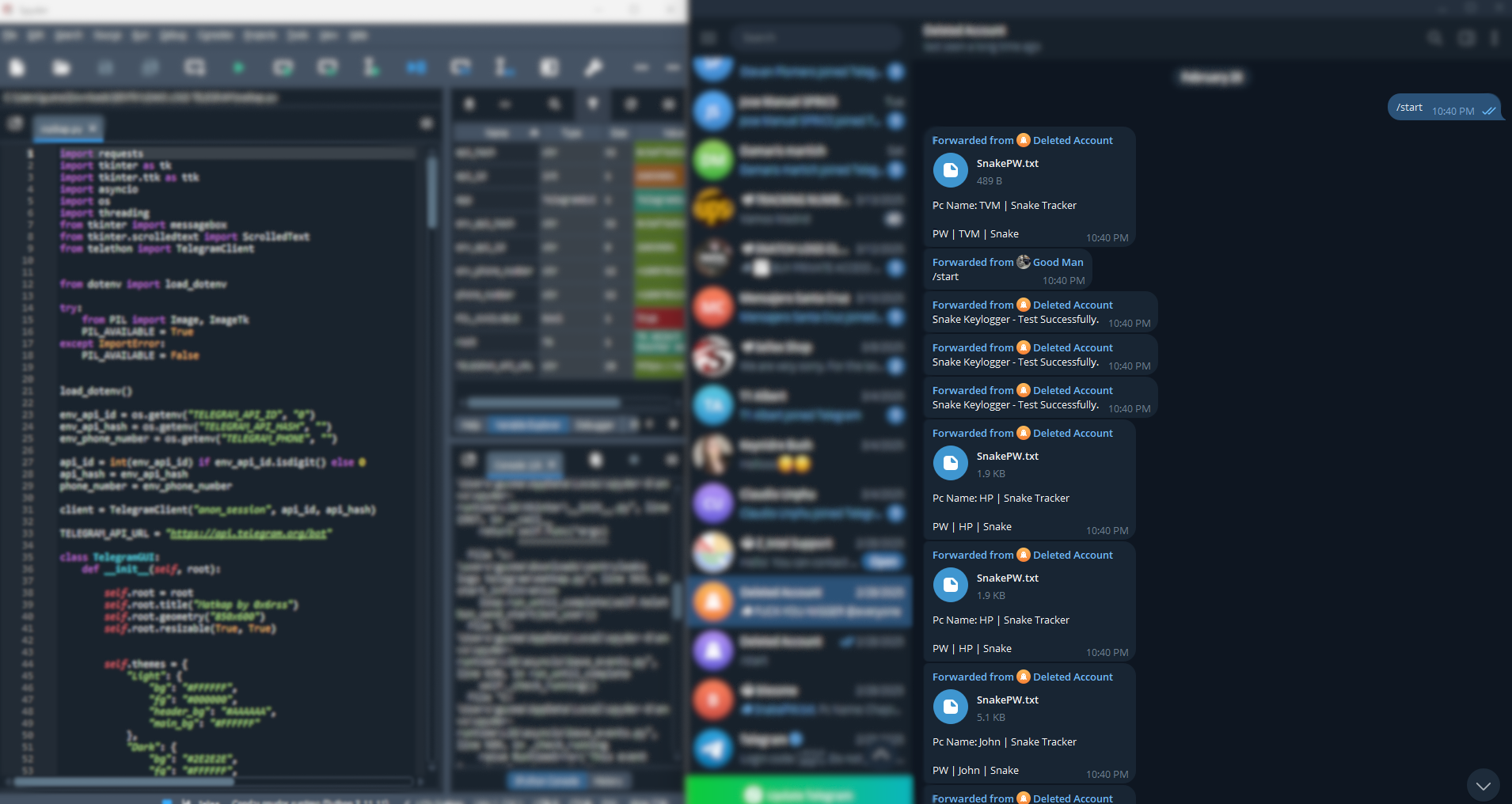
Figure 3. Telegram Bot Monitor usingMatkap
Compared to the dark web, Telegram requires less technical knowledge to navigate. The low barrier to entry has attracted a new generation of cybercriminals who use it to coordinate attacks, advertise malware-as-a-service, and sell access credentials in real time. Many Telegram channels have thousands of subscribers and remain active for months or even years without takedown.
Common TTPs Linked to Leaked Credentials
The analysis of infostealer logs reveals consistent attacker behaviors, mapped to known MITRE ATT&CK techniques:
T1056.001 – Input Capture (Keylogging): Records user keystrokes to capture credentials and activity context.
T1555 – Credential Dumping: Extracts saved passwords, cookies, and autofill data from browsers.
T1078 – Valid Accounts: Reuses stolen credentials to gain access to VPNs, cloud services, and internal apps.
T1566 – Phishing: Delivers stealers via fake updates, cracked software, or malicious email attachments.
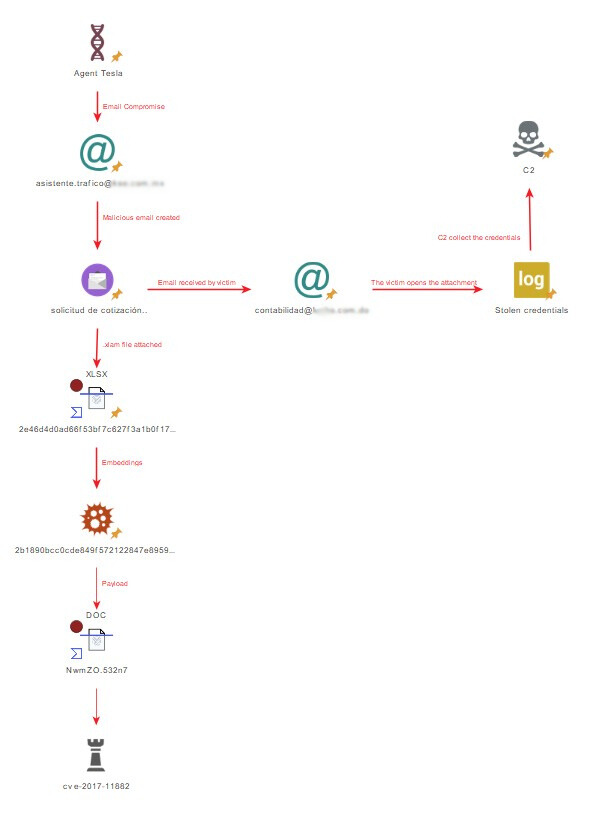
Figure 4: Agent Tesla Phishing Distribution Sample
We're just getting started. And if you're part of a security team, researcher network, or even just someone who cares about your digital safety, we invite you to follow our journey, ask questions, and share your thoughts. Because this isn't just about credentials—it's about building resilience against the next phase of cyber threats.
Stay safe.
-- The Sentry Leak Team
Subscribe to my newsletter
Read articles from Alina directly inside your inbox. Subscribe to the newsletter, and don't miss out.
Written by
