Cyber Security (Day-2)
 Balaji Patil
Balaji PatilCyber Threats
Attackers use a variety of tech and attack types to achieve their objective.
Malware and Ransomware
malware is a file or code that typically takes control of, collects info from, or damage an infected endpoint. Malware is an inclusive term for all types of malicious software.
Malware usually has one or more of the following objectives:
Provide remote control for an attacker to use an infected machine
To send spam from the infected machine to unsuspecting targets
To investigate the infected user’s local network
To steal sensitive data
Malware Types
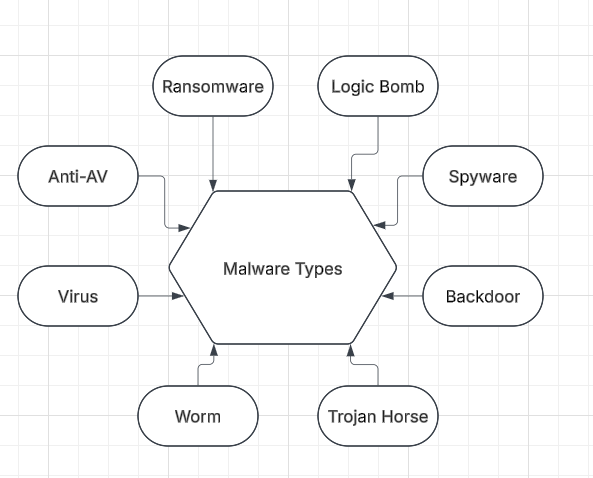
Logic Bomb: It is a malware that is triggered by a specified condition, such as a given date or a particular user account being disabled
Spyware: spyware is a malware that collect info, such as internet surfing behavior, login credentials and financial account information, on an infected endpoint
Rootkits: A rootkits is malware that provides access to a computer. Rootkits are installed in the BIOS of machine, which means operating system-level security tools cannot detect them.
Bootkit : It is malware that is a kernel-mode variant of a rootkit, commonly used to attack computers that are protected by full-disk encryption.
Backdoor: It is malware that allows an attacker to bypass authentication to gain access to a compromised system.
Anti-AV: It is malware that disables legitimately installed antivirus software on the compromised endpoint, thereby preventing automatic detection and removal of other malware.
Ransomware: It is malware that locks a computer or device (Locker ransomware) or encrypts data (Crypto ransomware) on an infected endpoint with an encryption key that only the attacker knows, thereby making the data unusable until the victim pays a ransom (usually with cryptocurrency, such as Bitcoin). Reveton and LockeR are two examples of Locker ransomware. Locky, TeslaCrypt/EccKrypt, Cryptolocker, and Cryptowall are examples of Crypto ransomware.
Trojan horse: It is malware that is disguised as a harmless program but actually gives an attacker full control and elevated privileges of an endpoint when installed. Unlike other types of malware, Trojan horses are typically not self-replicating.
Virus: It is malware that is self-replicating but must first infect a host program and be executed by a user or process.
Worm: It is malware that typically targets a computer network by replicating itself to spread rapidly. Unlike viruses, worms do not need to infect other programs and do not need to be executed by a user or process.
Subscribe to my newsletter
Read articles from Balaji Patil directly inside your inbox. Subscribe to the newsletter, and don't miss out.
Written by
