Phishing Campaign Masquerades as Booking[.]com to Deploy Credential-Stealing Malware Suite
 FPT Metrodata Indonesia
FPT Metrodata Indonesia
Summary
Microsoft recently published a blog detailing an ongoing phishing campaign that impersonates Booking[.]com to target hospitality organizations worldwide. First observed in December 2024, this campaign escalated during peak travel periods and remains active as of February 2025. The phishing attack specifically targets organizations in North America, Oceania, South and Southeast Asia, and Europe, sending fake emails that appear to come from Booking[.]com. The goal is to steal credentials and conduct financial fraud.
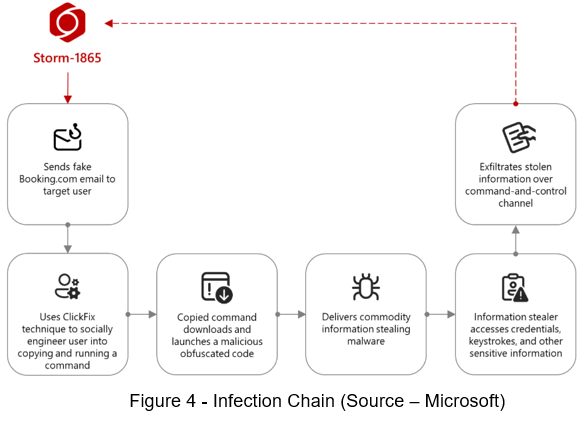
Threat actors use a social engineering method called ClickFix, where victims are tricked into copying and executing malicious commands. The phishing page prompts users to open the Windows Run window and paste a command from their clipboard, leading to malware installation. Microsoft tracks this activity under Storm-1865, a cluster linked to credential theft and fraudulent financial transactions. This technique bypasses automated security defenses by relying on human interaction.
Technical Details
Storm-1865 specifically targets hospitality organizations and individuals within those organizations who are likely to interact with Booking[.]com. The attackers send phishing emails impersonating the travel agency, using diverse lures such as negative guest reviews, booking requests, promotional opportunities, and account verification notices. These tactics are designed to deceive recipients into engaging with malicious content, ultimately leading to credential theft and financial fraud.

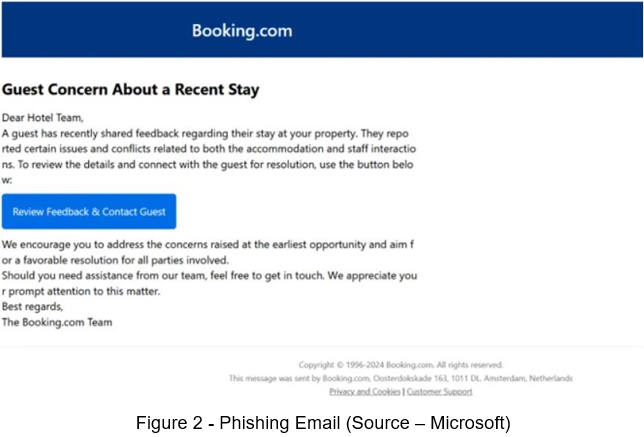
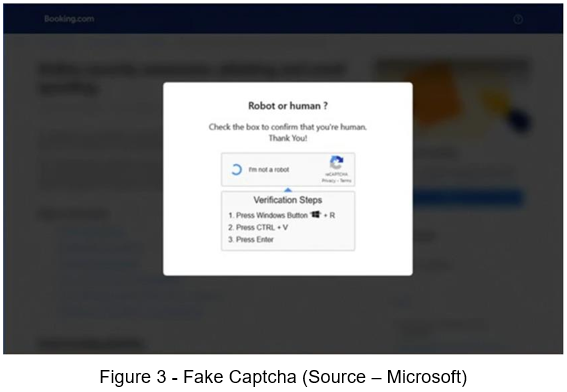
The phishing email contains a malicious link or a PDF attachment that falsely claims to direct recipients to Booking[.]com. When clicked, the link leads to a fraudulent webpage displaying a fake CAPTCHA over a background that mimics a legitimate Booking[.]com page. This deceptive CAPTCHA is a key part of the ClickFix social engineering technique. It tricks users into opening the Windows Run window, pasting a preloaded command from their clipboard, and executing it. This action downloads and installs the malicious payload, enabling credential theft and potential financial fraud. The added illusion of legitimacy through CAPTCHA increases the likelihood of victims following the instructions.
The phishing campaign distributes various commodity malware families, including XWorm, Lumma Stealer, VenomRAT, AsyncRAT, Danabot, and NetSupport RAT. These payloads enable credential and financial data theft, aligning with Storm-1865’s known activities. The attack uses mshta.exe to execute malicious code, downloading PowerShell, JavaScript, or portable executable (PE) content, depending on the payload. Storm-1865 has previously conducted similar campaigns, including targeting hotel guests via Booking[.]com in 2023 and e-commerce buyers with fraudulent payment pages in 2024. The addition of the ClickFix technique to its tactics demonstrates an adaptation to evade conventional security defenses, further enhancing its ability to compromise targets.
Recommendations
Check if the email is from a trusted source. Hover over the email address to spot inconsistencies.
Be cautious of emails pressuring you to click links, download files, or provide credentials.
Hover over links to inspect the full URL. Navigate to official websites directly instead of clicking email links.
Look for spelling errors or slight alterations in domain names (e.g., "micros0ft[.]com" instead of "microsoft[.]com").
If unsure, reach out to the service provider using official contact details from their website.
Conclusion
This phishing campaign demonstrates Storm-1865’s evolving tactics, leveraging ClickFix to bypass traditional security defenses and trick users into executing malicious commands. By impersonating Booking[.]com and using urgent, contextually relevant lures, the attackers increase their chances of success, ultimately delivering credential-stealing malware to facilitate financial fraud. The use of multiple malware families and social engineering techniques underscores the sophistication and adaptability of this threat actor. As Storm-1865 continues to refine its attack methods, organizations in the hospitality sector remain prime targets, highlighting the need for continued vigilance against phishing threats.
Subscribe to my newsletter
Read articles from FPT Metrodata Indonesia directly inside your inbox. Subscribe to the newsletter, and don't miss out.
Written by

FPT Metrodata Indonesia
FPT Metrodata Indonesia
PT FPT Metrodata Indonesia (FMI) is a joint venture between FPT IS and Metrodata Electronics, focusing on providing Cybersecurity-as-a-Service—including SOC, managed security, professional services, consulting, and threat intelligence—to support Indonesia’s rapidly growing digital economy. FMI is expanding into AI and cloud GPU services to deliver innovative protection and solutions for enterprises. Learn more at https://fmisec.com.