Malicious Apps On Google Play Store Bypassing Android 13 Restrictions
 FPT Metrodata Indonesia
FPT Metrodata Indonesia
Summary
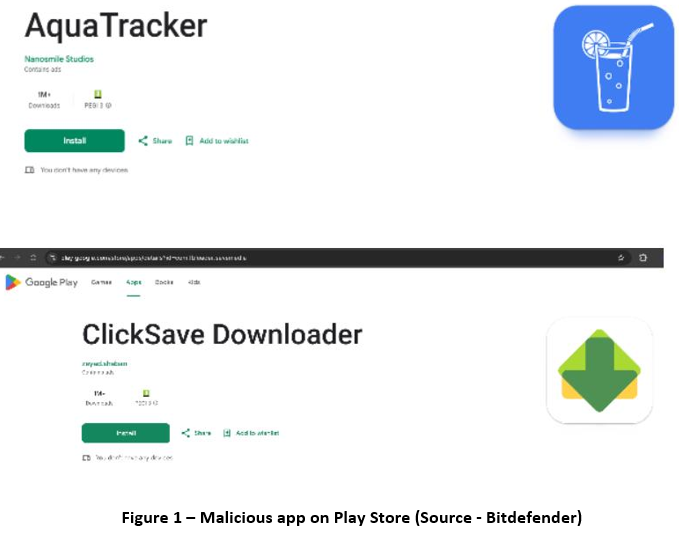
Bitdefender researchers have uncovered a large-scale ad fraud campaign involving at least 331 malicious apps on the Google Play Store, which have amassed over 60 million downloads. These apps primarily serve out-of-context ads but also engage in phishing attacks, attempting to steal user credentials and credit card details.
Some of the apps hide their icons to evade detection and can start automatically, even on Android 13, bypassing security restrictions. While some maintain basic functionality, they exploit loopholes to overlay ads without special permissions, making them difficult to detect.
The campaign appears to be the work of a single threat actor or multiple groups using the same packaging tool from black markets. Many apps masquerade as harmless utilities, such as QR scanners, health apps, and expense trackers.
Technical Details
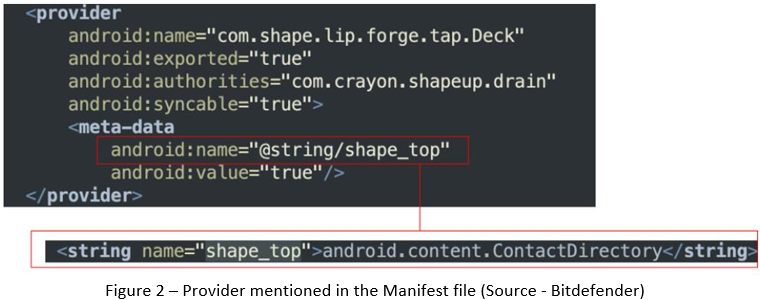
Attackers in this ad fraud campaign use a contact content provider that is automatically queried by the system upon installation, allowing the app's entry point to load stealthily. Initially, this provider was directly referenced in the manifest, but newer samples now store it as a string in resources to evade detection. This evolution in tactics has likely contributed to the large number of fraudulent apps identified, demonstrating how cybercriminals continuously adapt their methods to bypass security measures and remain on the Google Play Store.
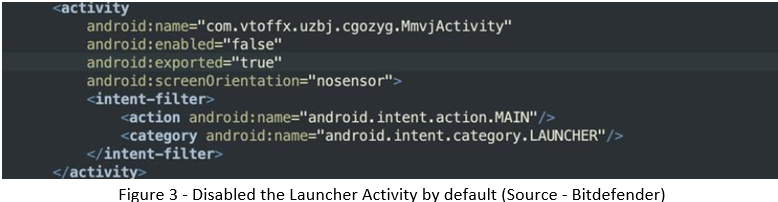
Attackers have devised multiple techniques to hide malicious app icons, bypassing Android's restrictions. One common method involves disabling the Launcher Activity by default and later enabling it using native code via the content provider startup mechanism. After completing the setup, the app disables its launcher again, making the icon disappear. This suggests attackers may have found an Android bug or are abusing the API.
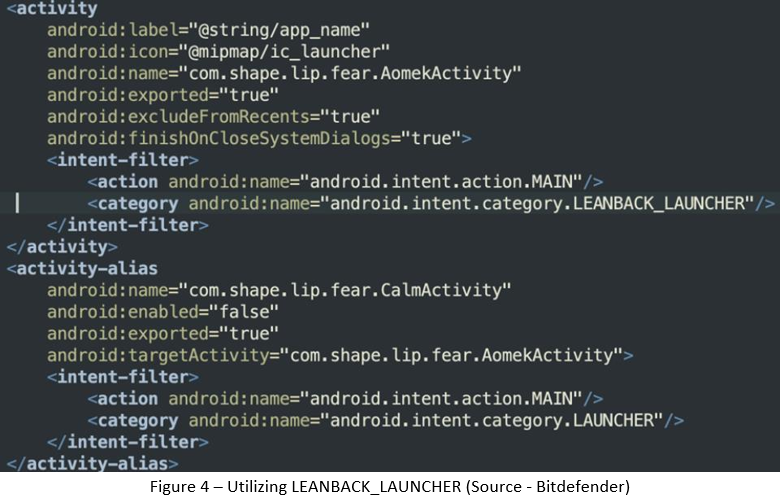
Another technique leverages the LEANBACK_LAUNCHER, designed for Android TV, to evade detection. By using an alias activity that points to a hidden launcher, attackers can dynamically enable or disable the app icon at will. Some apps also contain leftover metadata hinting at such behavior. These methods allow malware developers to control when the app is visible, making detection and removal more challenging.
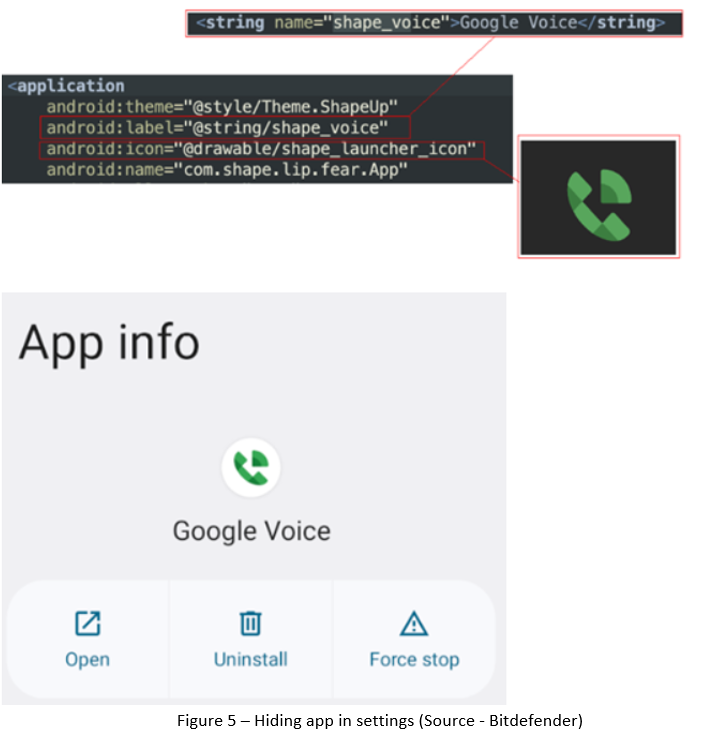
Some apps attempt to hide from the Settings menu to prevent user removal. In one example, an app even renames itself to Google Voice to appear legitimate and avoid suspicion.
Across multiple samples, attackers employ a native library to stealthily launch activities without required permissions by abusing Android’s DisplayManager API. They create a virtual display, detect it using a display listener, and then use the Presentation API to render content before triggering a fullscreen activity via startActivity. This technique allows attackers to launch phishing attacks, tricking users into entering credentials for platforms like Facebook or YouTube or providing credit card details under false pretenses.

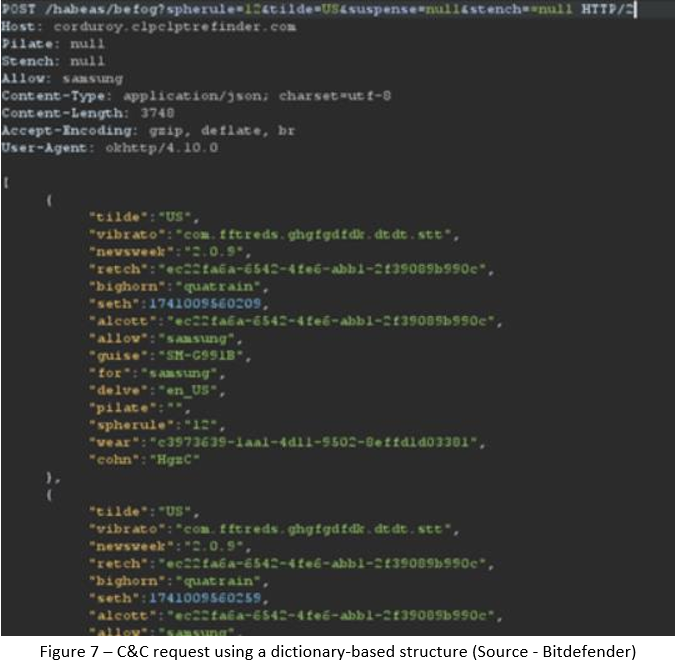
Malicious apps use dedicated C&C domains with unique links for each package and employ encrypted communication methods, combining AES, Base64, and custom encryption. They exfiltrate device information in a dictionary-based structure, but the keys are polymorphic and unique per app, making detection challenging.
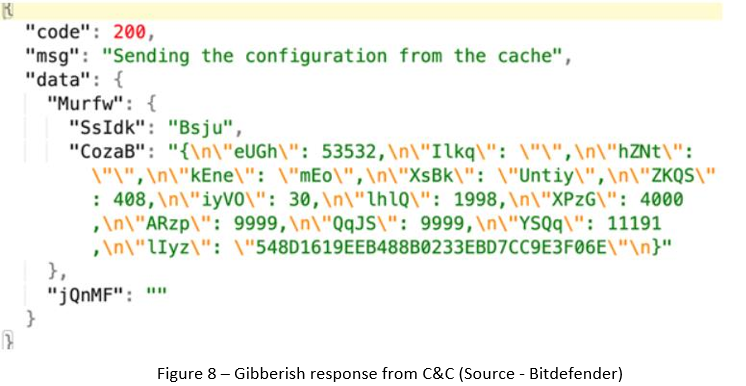
On the server side, decrypted responses are intentionally obfuscated, appearing as gibberish to hinder block analysis. This manipulated response is then used to configure ad SDKs, ensuring the malware can continue serving fraudulent ads while evading security measures.
Recommendations
Download and install software only from official app stores like the Play Store or the iOS App Store.
Use a reputed anti-virus and internet security software package on your connected devices, such as PCs, laptops, and mobile devices.
Use strong passwords and enforce multi-factor authentication wherever possible.
Enable biometric security features such as fingerprint or facial recognition for unlocking the mobile device where possible.
Be wary of opening any links received via SMS or emails delivered to your phone.
Ensure that Google Play Protect is enabled on Android devices.
Be careful while enabling any permissions.
Keep your devices, operating systems, and applications updated.
Conclusion
This large-scale ad fraud campaign demonstrates the evolving tactics cybercriminals use to bypass Android security measures, evade detection, and maximize their reach. By leveraging hidden launchers, encrypted communications, and obfuscated C&C responses, attackers effectively deploy phishing attacks and fraudulent ads while making analysis and removal more challenging. The findings highlight the need for continuous security monitoring, advanced behavioral detection, and proactive threat mitigation beyond default Android protections.
Subscribe to my newsletter
Read articles from FPT Metrodata Indonesia directly inside your inbox. Subscribe to the newsletter, and don't miss out.
Written by

FPT Metrodata Indonesia
FPT Metrodata Indonesia
PT FPT Metrodata Indonesia (FMI) is a joint venture between FPT IS and Metrodata Electronics, focusing on providing Cybersecurity-as-a-Service—including SOC, managed security, professional services, consulting, and threat intelligence—to support Indonesia’s rapidly growing digital economy. FMI is expanding into AI and cloud GPU services to deliver innovative protection and solutions for enterprises. Learn more at https://fmisec.com.