Arcane Stealer: Unveiling Its Data Exfiltration Capabilities
 FPT Metrodata Indonesia
FPT Metrodata Indonesia
Summary
Kaspersky recently published a blog detailing the discovery of a new stealer, Arcane, which surfaced in late 2024. This malware was distributed via YouTube videos promoting game cheats and is particularly notable for the extensive range of data it collects. It targets account credentials from VPN services, gaming platforms, and various networking tools, including ngrok, Playit, Cyberduck, FileZilla, and DynDNS. Despite sharing a name, this stealer is unrelated to the well known Arcane Stealer V. Additionally, the threat actor behind Arcane later introduced a similarly named loader, which pretends to offer cheats and cracks but instead delivers malware to victims' devices.
Technical Details
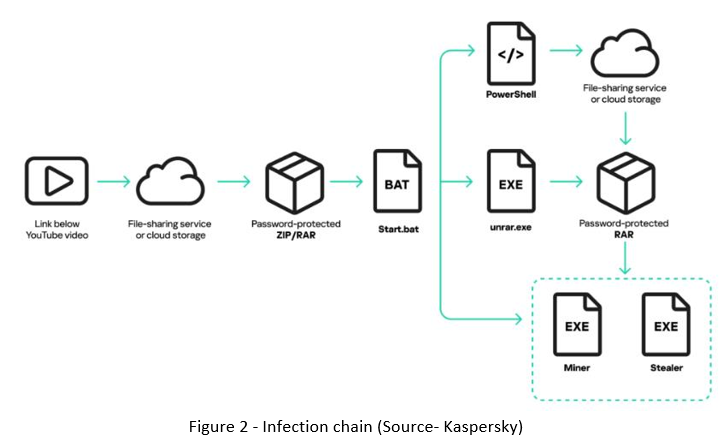
Kaspersky's analysis revealed that the campaign distributing the Arcane Stealer had been active even before the malware itself was identified. The initial distribution relied on YouTube videos advertising game cheats, often linking to a downloadable archive protected by a password. Once extracted, the archive always contained a start.bat batch file in the main directory and an UnRAR.exe utility within a subfolder. The batch file was obfuscated and functioned solely to retrieve another password-protected archive using PowerShell. This second archive was then extracted with UnRAR.exe, using a password embedded within the batch file as an argument.
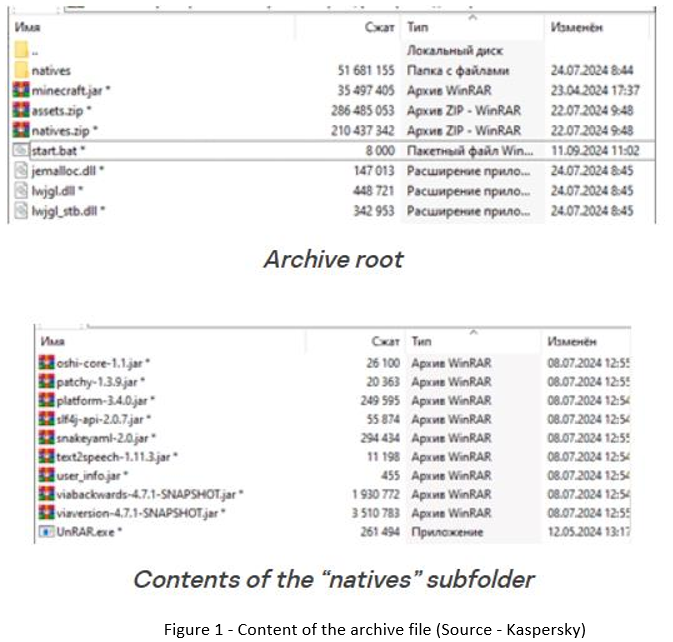
After extraction, start.bat executed the payload via PowerShell while also modifying system settings to evade detection. It disabled Windows SmartScreen by altering registry keys and adding all root directories to the SmartScreen exception list. Each archive contained two executables—a cryptocurrency miner and a stealer. The stealer was identified as a variant of the Phemedrone Trojan, but the attackers had rebranded it as “VGS”. This branding was evident in the stealer’s activity reports, where "VGS" appeared in the header alongside the report’s date and timestamp.
Arcane Stealer
Kaspersky uncovered a new Arcane Stealer at the end of 2024, replacing the previous VGS variant in an ongoing malware campaign. While a different Arcane Stealer V surfaced in 2019, the newly identified stealer is unrelated and derives its name from ASCII art in its code. Despite borrowing elements from existing stealers, Arcane could not be linked to any known malware families.
The stealer undergoes frequent updates, modifying its capabilities across versions. It extracts credentials, configuration files, and settings from VPN clients, network utilities, messaging apps, email clients, gaming services, and cryptocurrency wallets. Additionally, it collects system details, including OS information, installed software, and saved Wi-Fi passwords.
Arcane employs advanced browser data theft techniques, using the Data Protection API (DPAPI) and an embedded Xaitax utility to decrypt login credentials and cookies. It also exploits a Chromium debug port, launching browsers in debugging mode to steal cookies from platforms like Gmail, Steam, YouTube, and Twitter.
ArcanaLoader
A few months after detecting the Arcane Stealer, researchers observed a shift in its distribution method. Instead of promoting game cheats, cybercriminals began using YouTube to advertise ArcanaLoader, a loader with a graphical interface designed to download and execute popular cracks, cheats, and similar software. Most cases, the links in these videos directed users to an executable file, which then retrieved an archive containing ArcanaLoader. The loader also provided access to a Discord server, where users could find news, support, and download links for updated versions. Additionally, one of the Discord channels featured an advertisement seeking bloggers to help promote ArcanaLoader.

Discussions on the Discord server, as well as the language used in YouTube videos and news updates, were exclusively in Russian, indicating a Russian-speaking target audience. Telemetry data confirmed that most affected users were located in Russia, Belarus, and Kazakhstan.
Conclusion
The emergence of Arcane Stealer and its evolving distribution tactics underscore the adaptability of cybercriminals in targeting unsuspecting users. Initially spread through YouTube videos promoting game cheats, the malware later transitioned to a more sophisticated delivery method via ArcanaLoader, a seemingly legitimate tool used to execute malicious payloads. The integration of Discord for distribution, support, and recruitment further highlights the attackers’ strategic efforts to expand their reach.
This campaign focuses heavily on Russian-speaking users, as evidenced by telemetry data and language indicators. It demonstrates how threat actors leverage social engineering and trusted platforms to spread malware effectively. The frequent updates to Arcane Stealer’s capabilities suggest that it will continue evolving, posing a persistent threat to users seeking game-related tools. This case serves as a critical reminder of the dangers of downloading unverified software and the importance of cybersecurity awareness to avoid falling victim to such attacks.
Subscribe to my newsletter
Read articles from FPT Metrodata Indonesia directly inside your inbox. Subscribe to the newsletter, and don't miss out.
Written by
