Cybersecurity in Cloud Finance: Strategies for Protecting Sensitive Financial Data
 Avinash Pamisetty
Avinash Pamisetty
The world of finance has become increasingly reliant on cloud technology, with financial institutions, fintech companies, and businesses shifting operations to the cloud for its scalability, flexibility, and cost-efficiency. However, this shift also introduces a set of cybersecurity risks, particularly concerning the protection of sensitive financial data. Financial data is one of the most valuable targets for cybercriminals, making the need for robust security protocols in the cloud more critical than ever. This article will explore strategies for securing sensitive financial data in the cloud, providing financial organizations with best practices to mitigate potential threats and safeguard customer trust.
The Importance of Cybersecurity in Cloud Finance
Cloud computing allows financial institutions to store and process vast amounts of data, including customer information, transaction records, and financial statements. This access to cloud resources improves operational efficiency and reduces costs, but it also creates a larger attack surface for cybercriminals. Data breaches, ransomware attacks, and other cyber incidents can have devastating consequences for financial institutions. Not only can these breaches result in significant financial losses, but they can also erode customer trust, damage a company’s reputation, and lead to regulatory penalties.
Given the increasing frequency of cyber threats, especially in the finance sector, it is essential for organizations to implement strong cybersecurity measures in the cloud. The following strategies are critical in ensuring that sensitive financial data is adequately protected.
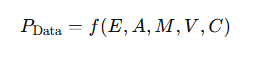
EQ 1. Data Protection Equation
1. Data Encryption
Encryption is one of the most effective ways to protect sensitive financial data both in transit and at rest. Data encryption ensures that even if unauthorized individuals gain access to financial data, they will not be able to read or use it without the appropriate decryption keys.
Encryption at Rest: Data stored in cloud servers should be encrypted, so even if an attacker gains access to the storage systems, they cannot access the raw data without the decryption key.
Encryption in Transit: Sensitive data being transferred between cloud environments or between users and cloud-based applications should also be encrypted using secure communication protocols like TLS/SSL. This prevents attackers from intercepting data during transmission.
Implementing end-to-end encryption ensures that data remains confidential throughout its lifecycle in the cloud, making it much harder for cybercriminals to exploit.
2. Multi-Factor Authentication (MFA)
Multi-factor authentication (MFA) is a critical security feature that adds an extra layer of protection when accessing cloud-based financial applications. Instead of relying on just a password, MFA requires users to provide additional verification, such as a one-time code sent to their phone, or biometric data (like a fingerprint or facial recognition).
For financial institutions, MFA can prevent unauthorized access to sensitive accounts, reducing the risk of data breaches caused by compromised credentials. For instance, even if an attacker manages to steal a user's login credentials, they would still need the second authentication factor to gain access.
MFA should be enforced for all users, especially for individuals with high-level privileges, such as financial officers, who can access the most sensitive data in the organization.

3. Data Masking and Tokenization
Data masking and tokenization are techniques that protect sensitive financial data by replacing actual values with non-sensitive equivalents.
Data Masking: This involves altering or obfuscating sensitive data so that it cannot be read by unauthorized parties. For example, part of a customer’s credit card number may be masked, with only the last four digits visible to authorized users.
Tokenization: This process involves replacing sensitive data with a unique token that has no usable value outside of the specific system. For example, real account numbers may be replaced by a string of numbers or characters that cannot be reversed without the appropriate keys.
These methods reduce the exposure of sensitive data and minimize the risk of it being misused if it is intercepted or exposed during a cyber attack.
4. Regular Security Audits and Vulnerability Scanning
Regular security audits and vulnerability assessments are essential for identifying and addressing potential security weaknesses in the cloud environment. These audits allow financial institutions to stay ahead of emerging threats and ensure that their cloud security protocols are up to date.
Cloud environments are dynamic and constantly evolving, so it is important to continually monitor for vulnerabilities. This includes checking for misconfigured cloud resources, outdated software versions, or potential gaps in access control mechanisms. Vulnerability scanning tools can identify weaknesses in the system and recommend appropriate fixes.
Additionally, regular audits ensure compliance with industry regulations such as the General Data Protection Regulation (GDPR), the Payment Card Industry Data Security Standard (PCI DSS), and other standards that govern financial data protection.

5. Strong Access Control and Role-Based Permissions
One of the key elements of securing financial data in the cloud is implementing strong access control measures. Not all employees need access to all sensitive data, and restricting access based on roles is a fundamental principle of cybersecurity.
Role-Based Access Control (RBAC): With RBAC, access to financial data is granted based on the user's job role. For example, a financial analyst may only need access to transaction data, while an executive may require access to broader financial reports.
Least Privilege: The principle of least privilege ensures that users are only granted the minimum level of access required to perform their job duties. By limiting access to sensitive data, the damage caused by a compromised account is minimized.
These access controls, combined with regular audits, help ensure that only authorized individuals can access sensitive financial data, reducing the risk of internal threats or accidental data exposure.
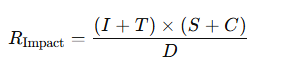
EQ 2. Incident Response and Recovery Equation
6. Cloud Service Provider (CSP) Security Standards
When selecting a cloud service provider (CSP) for financial data storage and processing, it is important to consider the security standards and certifications the provider adheres to. Reputable CSPs will offer robust security measures, including encryption, compliance with industry regulations, and strong access control policies.
Before entering into a contract with a CSP, financial organizations should verify the provider's compliance with standards like:
ISO/IEC 27001 for information security management
SOC 2 Type II for security, availability, and confidentiality controls
PCI DSS for payment card data protection
Choosing a trusted CSP that prioritizes security can help ensure that sensitive financial data is protected from potential risks.
7. Incident Response Planning
Despite best efforts, no system is completely immune to cyber threats. Therefore, financial institutions should develop and maintain an effective incident response plan (IRP) to address potential security breaches.
An IRP provides a clear framework for identifying, responding to, and recovering from security incidents. The plan should include procedures for:
Detecting breaches as quickly as possible
Notifying affected parties (customers, regulators, etc.)
Containing and mitigating damage
Restoring systems and data from backups
By having an IRP in place, financial organizations can minimize the impact of a breach and ensure a faster recovery.

Conclusion
As financial institutions continue to migrate to the cloud, safeguarding sensitive financial data becomes an increasingly critical priority. Implementing strong cybersecurity measures, such as data encryption, MFA, role-based access control, and regular security audits, can help mitigate risks and protect against cyber threats. In addition, working with a trusted cloud service provider and maintaining a well-defined incident response plan will ensure that financial data remains secure in the face of evolving cyber risks.
By adopting these strategies, financial organizations can enjoy the benefits of cloud technology while minimizing the risks associated with storing and processing sensitive financial data in the cloud.
Subscribe to my newsletter
Read articles from Avinash Pamisetty directly inside your inbox. Subscribe to the newsletter, and don't miss out.
Written by
