Data Breach Reality Check
 Valere
Valere
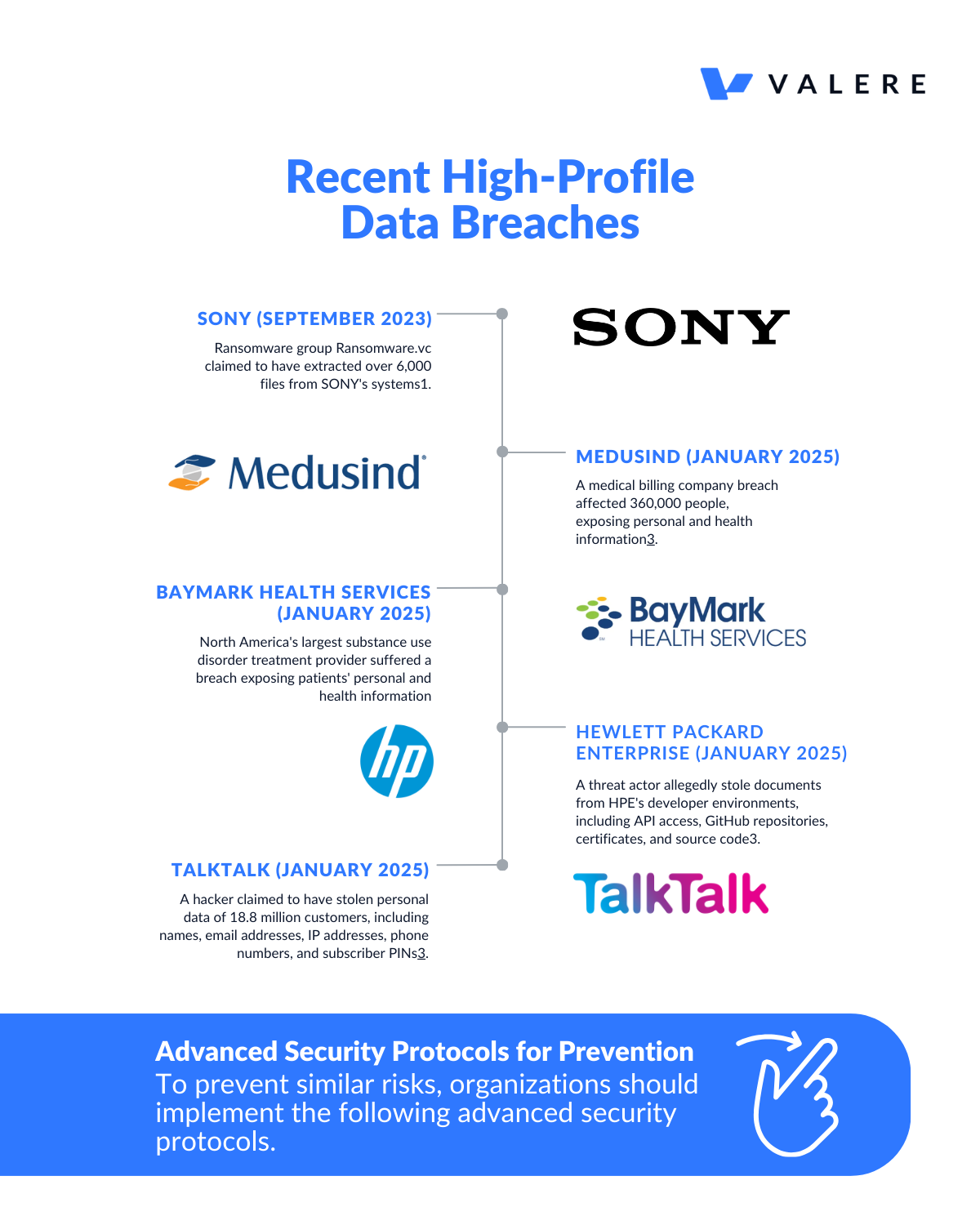
Recent high-profile data breaches have highlighted the ongoing challenges in cybersecurity. Here's an analysis of some notable breaches and how advanced security protocols can mitigate similar risks:
Recent High-Profile Data Breaches
Advanced Security Protocols for Prevention
To prevent similar risks, organizations should implement the following advanced security protocols:
1. Multi-Factor Authentication (MFA) and Passwordless Authentication
Implement strong MFA, preferably including biometric authentication, to prevent unauthorized access even if credentials are compromised. Passwordless authentication, using methods like fingerprints or hardware tokens, can further enhance security.
2. Advanced Encryption Technologies
Employ strong encryption for data at rest and in transit. Use algorithms like AES with 256-bit keys for stored data and protocols like TLS for data in transit. This ensures that even if data is intercepted, it remains incomprehensible to unauthorized individuals.
3. Zero Trust Model and Access Controls
Adopt a Zero Trust model, verifying all access attempts regardless of their origin. Implement role-based access controls (RBAC) and the principle of least privilege to limit exposure of sensitive data.
4. Regular Security Assessments and Penetration Testing
Conduct continuous threat modeling and penetration testing to identify and address vulnerabilities before they can be exploited.
5. Advanced Threat Detection Systems
Utilize AI-powered threat detection systems, like IBM's QRadar, to identify and respond to potential breaches in real-time, significantly reducing the time to discover security issues.
6. Data Loss Prevention (DLP) Tools
Employ DLP solutions to identify, classify, and monitor sensitive data in real-time, enforcing security policies and providing actionable insights.
7. Robust Patch Management
Implement an automated and comprehensive patch management process to minimize risks from outdated software, as many breaches exploit known vulnerabilities.
8. Employee Training and Awareness
Regularly educate employees on cybersecurity best practices, including recognizing phishing attempts and proper handling of sensitive data.
By implementing these advanced security protocols, organizations can significantly reduce their risk of suffering data breaches similar to the recent high-profile incidents. However, it's crucial to remember that cybersecurity is an ongoing process that requires constant vigilance and adaptation to new threats.
Is your organization ready? Dive deeper into the advanced security protocols discussed and implement a stronger security strategy. valere.io/ai
Subscribe to my newsletter
Read articles from Valere directly inside your inbox. Subscribe to the newsletter, and don't miss out.
Written by

Valere
Valere
Valere is an award-winning technology innovation & software development company, utilizing emerging technology in Machine Learning (ML) and Generative Artificial Intelligence (GenAI) to enable medium to large enterprises to execute, launch, and scale their vision into something meaningful.