Cyberstorm 2025 Writeup: Jimbei’s Secret [by Windows 9/11]
 Nayanesh
NayaneshCategory: Forensics
Team Name : Windows 9/11
Author: Nayanesh
CTF Writeup: Jimbe Forensics Forensics Challenge
Challenge Description
Description : Jimbei often disappears and no Straw Hat can find him. Where does he go!? Can you find his secret and assure Luffy that he is not sneaking around to Albasta ?

Initial Clues & Analysis
The challenge provided an image along with a description mentioning that Jimbe is always cut off in photos because he is shy. Initially, I overlooked this hint and began analyzing the image using standard forensic techniques.
Initial Checks Performed:
ExifTool Analysis (Read More Below): Ran
exiftool IMAGE.jpgto check metadata but found nothing useful.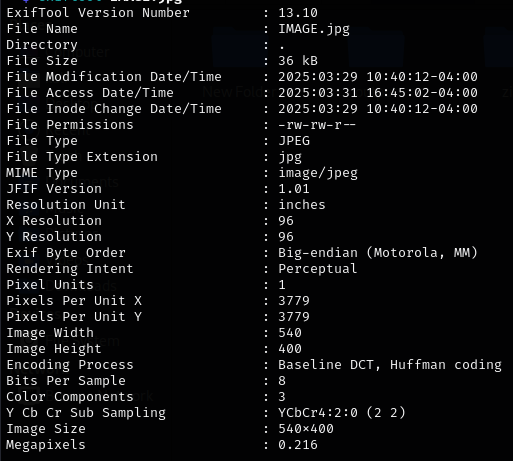
Strings Extraction: Used
strings IMAGE.jpgbut found no relevant hidden text.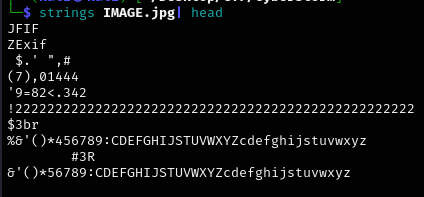
Steganography Analysis (Read More Below):
Ran
stegseek IMAGE.jpgto check for hidden data.The output indicated that the file was corrupted before a specific offset.
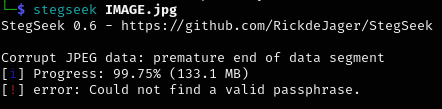
At this point, I suspected that the image might have structural issues, possibly affecting the resolution or format.
Investigation Path
Step 1: Attempting to Repair the Image
Used an online JPEG repair tool to see if the corruption could be fixed.
https://online.officerecovery.com/pixrecovery
(Tried on the above sites)
The repaired file did not reveal any hidden content.
Step 2: Revisiting the Challenge Description
Re-reading the challenge description made me reconsider the phrase about Jimbe always being "cut off" in images.
This suggested that the image dimensions might be incorrect or manipulated.
Step 3: Checking and Modifying the Image Resolution
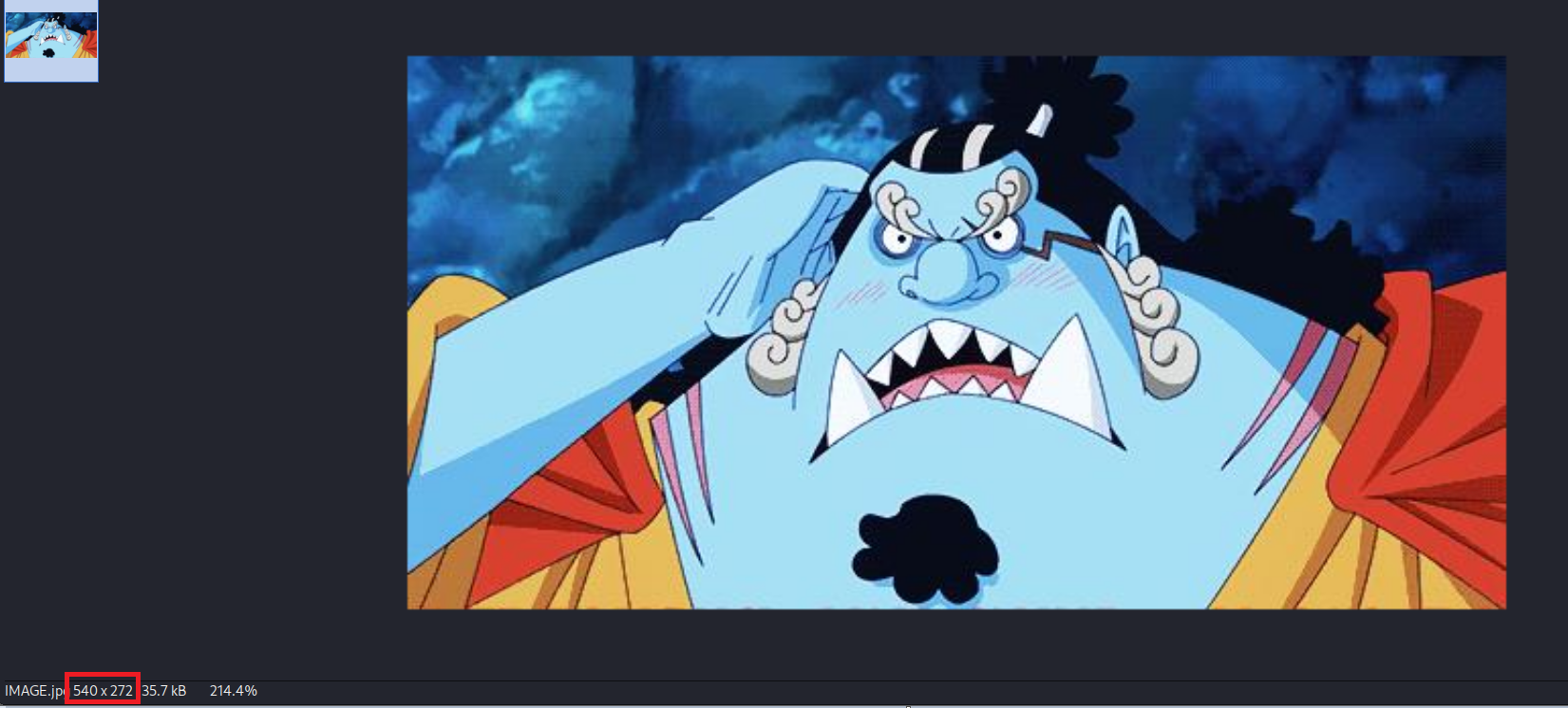
Checked the resolution of the image: 540x272 (272 height seemed unusual).
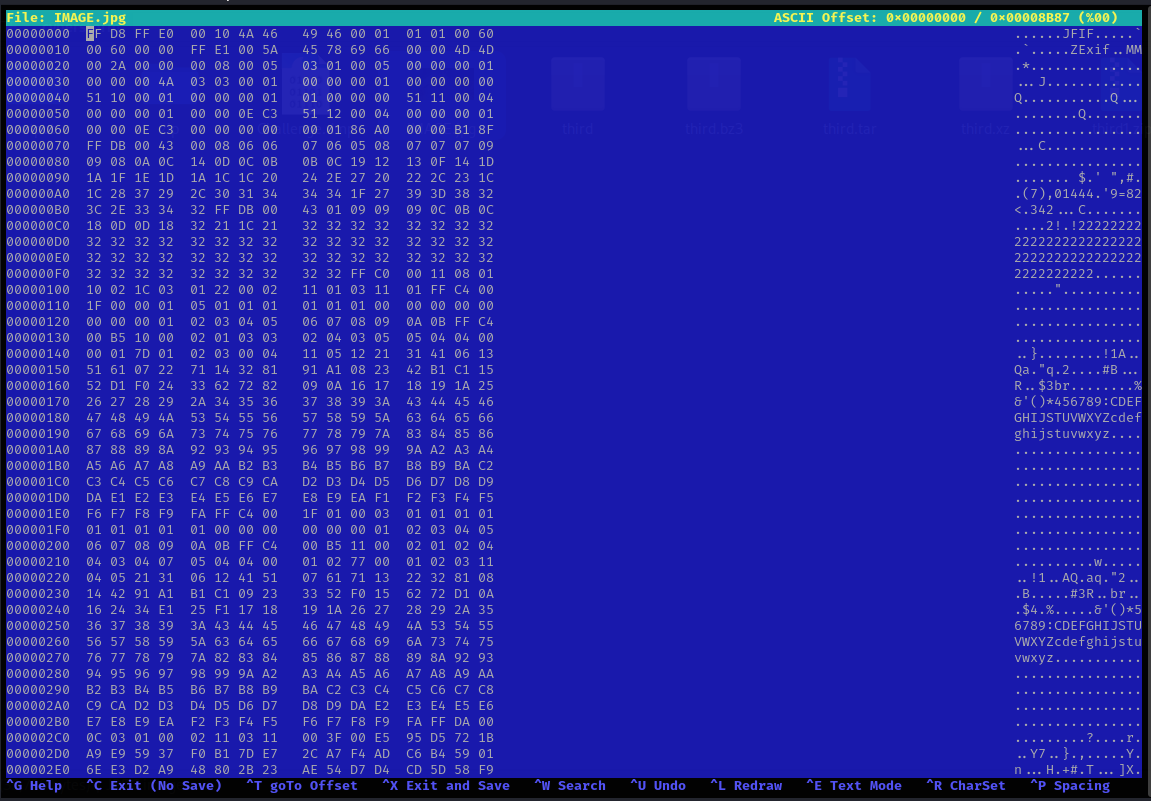
Opened the image in a hex editor (
hexeditor IMAGE.jpg).
(Use shortcut
W>Search for Hex Byte> Enter0110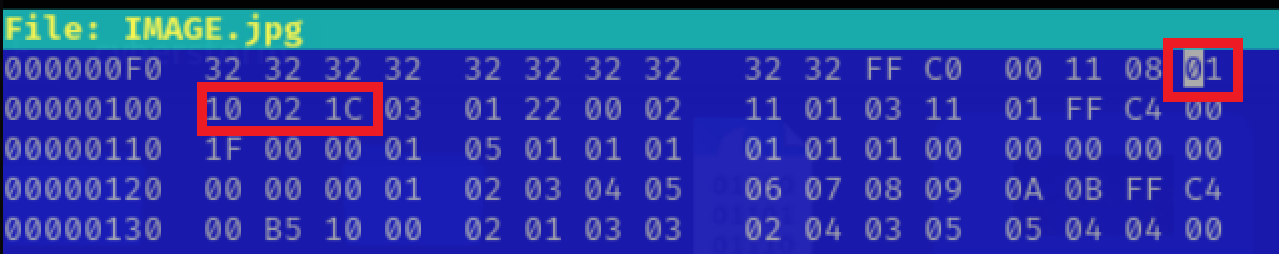
Located the resolution values in hex:
21C x 110(540 x 272 in decimal).(We can also verify that after
0110there is021cwhich is the width)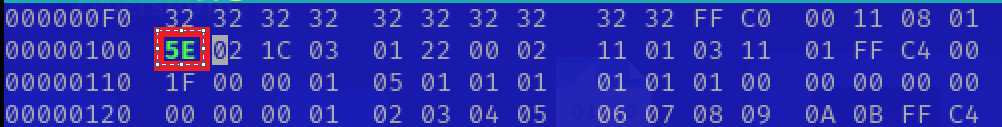
Changed the height value from
110(272 in decimal) to15E(350 in decimal).Saved the modified image.
Step 4: Revealing the Hidden Content
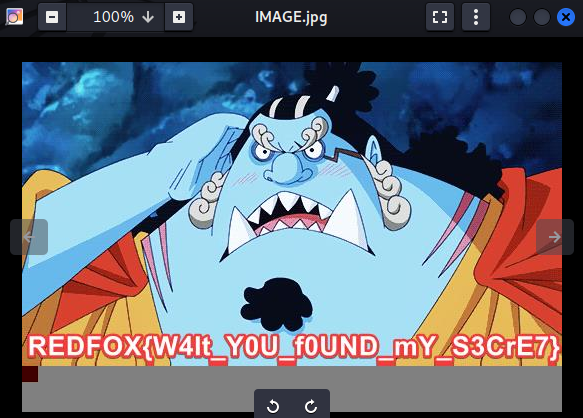
- Opened the modified image and successfully revealed the hidden part of the image containing the flag.
Finding the Flag
By adjusting the image height, the missing portion became visible.
The revealed section contained the flag.
Flag: REDFOX{W4It_Y0U_f0UND_mY_S3CrE7}
Tools & Resources Used
exiftool(Metadata analysis) -exiftoolis a command-line tool used to read, write, and edit metadata in various file types, including images, videos, and documents. It extracts data like camera details (make, model, exposure settings), timestamps, GPS coordinates, image dimensions, and more. It supports formats like JPG, PNG, TIFF, RAW, and MP4, among othersstrings(Extracting hidden text)stegseek(Checking for steganography) - Stegseek is a lightning fast steghide cracker that can be used to extract hidden data from files. It is built as a fork of the original steghide project and, as a result, it can run through the entirety ofrockyou.txtin under 2 seconds.Online JPEG repair tools
hexeditor(Editing image file structure)
Lessons Learned / Takeaways
Always read the challenge description carefully – subtle hints can provide crucial direction.
Image forensics isn't just about metadata or steganography – structural modifications (e.g., resolution changes) can be key.
Hex editing can help uncover hidden image content by modifying dimensions or file structure.
Avoid tunnel vision – I initially wasted time on conventional forensic techniques instead of considering file manipulation.
Rabbit Holes / Dead Ends
ExifTool & Strings Analysis: Did not yield useful data.
Steganography Check:
stegseekflagged corruption but was not the primary solution.JPEG Repair Attempt: Did not reveal any hidden information, though it confirmed corruption. This was showing due to the change in the height bit of the image.
This challenge reinforced the importance of thinking beyond traditional methods and considering how file structure modifications can be used to hide data in plain sight!
Subscribe to my newsletter
Read articles from Nayanesh directly inside your inbox. Subscribe to the newsletter, and don't miss out.
Written by
