Cyberstorm 2025 Writeup: The Hidden Secrets [by Windows 9/11]
 Nayanesh
NayaneshCategory: OSINT
Team Name : Windows 9/11
Author: Nayanesh
CTF Writeup: The Hidden Secrets OSINT Challenge
Challenge Description
Every member of the Redfox Security team seems to be hiding something from you. Their professional networking profiles look normal, but there's more than meets the eye.
Initial Clues & Analysis
The challenge hinted at employees, so my first stop was their official website: RedfoxSec. Navigating to the "About Us" section, I found details about their employees, but there were no links or any obvious hints. Since that was a dead end, my next move was to check their LinkedIn profile.
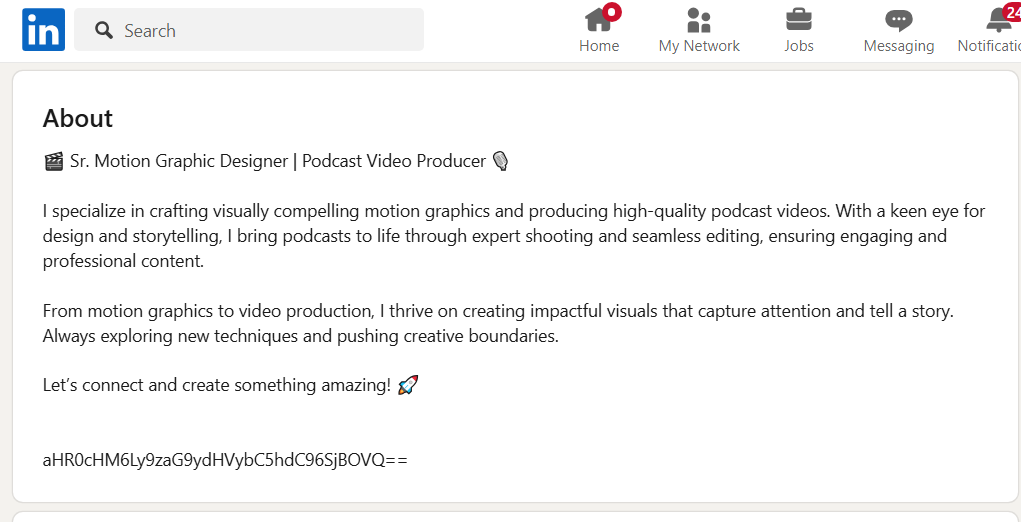
Clicking on the "People" section, I started scanning employee descriptions and posts, searching for any irregularities or encoded text. After reviewing a few profiles, I discovered one employee's bio contained a suspiciously encoded string. Upon decoding it using a Base64 decoder, it revealed a short URL.
Following the link, I found an image of Luffy and his crew from One Piece, which aligned with the theme of the CTF. This confirmed that I was on the right track.
Investigation Path
Step 1: Checking Other Employee Profiles
Recognizing a pattern, I proceeded to inspect more employee profiles. Multiple employees had cryptic text within their descriptions, encoded using various formats:
Base64
Base45
Base58
Other ciphers, which were identified using dcode.fr
Each decoded text led to a different URL, each hosting an image. Upon analyzing the images, I identified a subset that contained fragmented portions of a QR code.
Step 2: Finding Commonalities in the Images
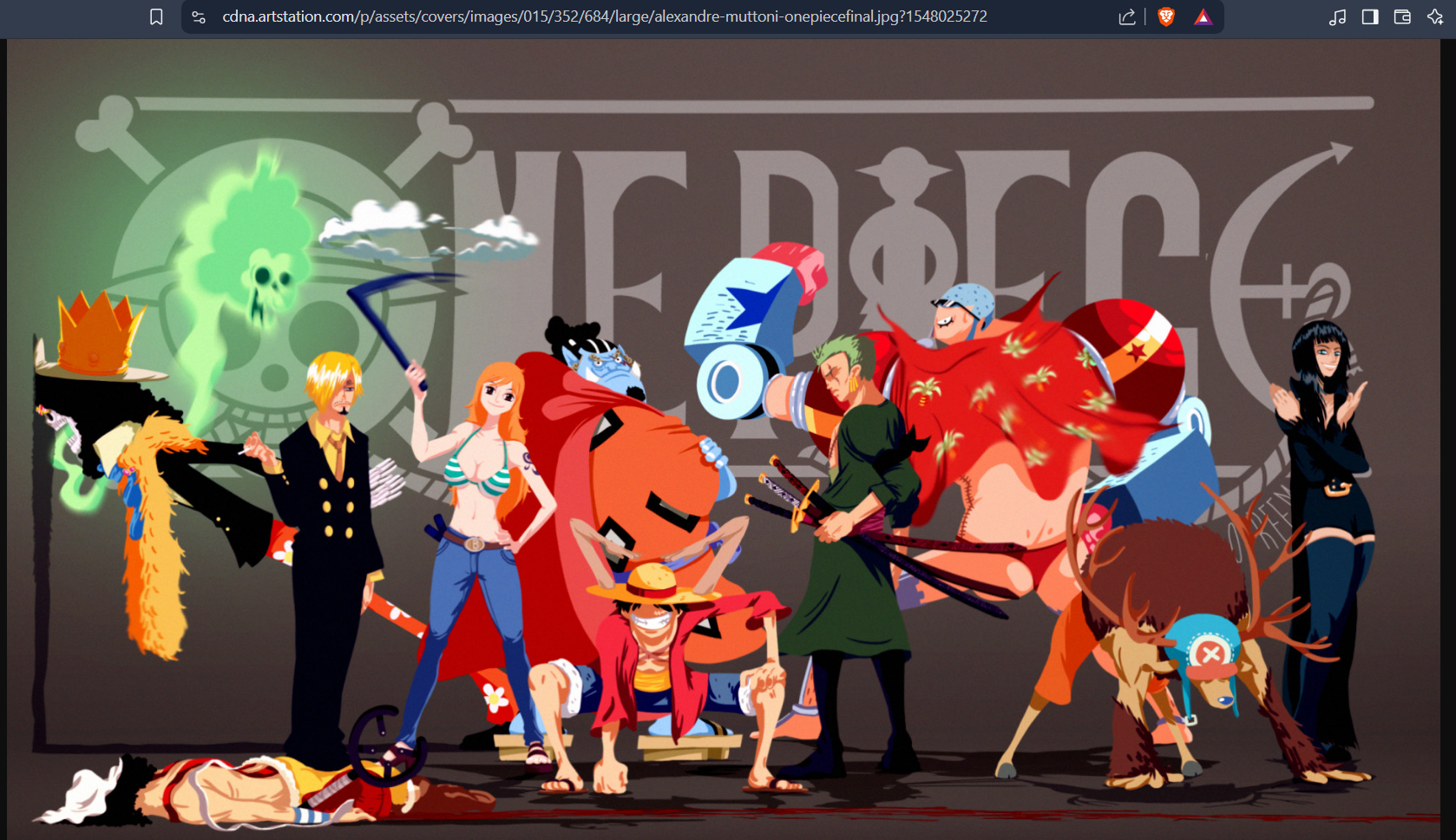

Most images were just random One Piece art, but four of them were different. They each contained a fragment of what looked like a QR code. Aha! This was a puzzle waiting to be assembled.

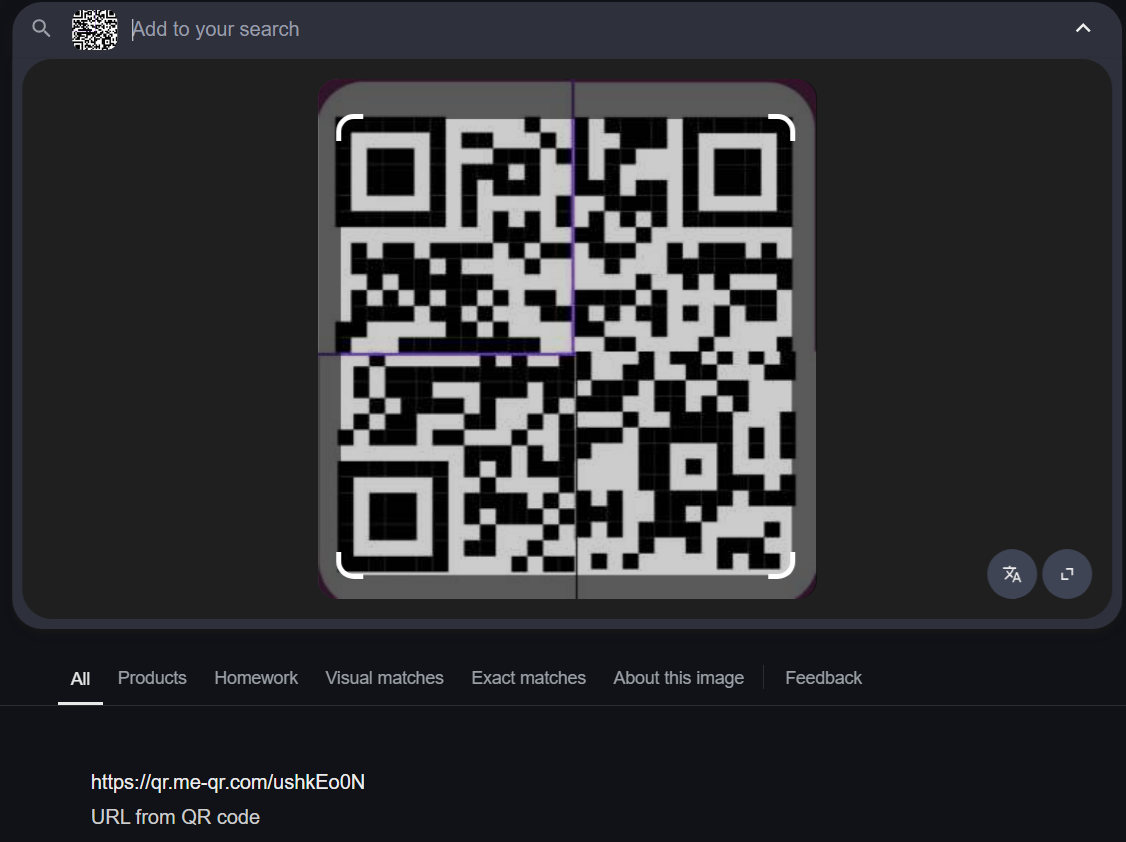
Four of the images appeared to be segments of a QR code. By assembling these pieces, I generated a complete QR code. Scanning it, however, resulted in this:
This was misleading, suggesting a decoy or another layer to the challenge.
Step 3: Digging Deeper into the URLs
Revisiting the URLs that hosted the QR code fragments, I noticed a recurring pattern in their structures. One particular URL stood out:
https://drive.google.com/file/d/14mKsrZkbIkpirsIpyckmYhbSG157XziB/view?=Thr0ugh
The term "Thr0ugh" appeared intentionally formatted. Checking the other URLs associated with the QR code fragments, I found similar terms:
S3cretL1nksSh4redThr0ugh
Putting it together: S3cretL1nksSh4redThr0ugh
Step 4: Constructing the Flag
The structured pattern in these terms suggested they formed the flag. Initially, I attempted:
flag{S3cret_L1nks_Sh4red_Thr0ugh}
This was incorrect. Removing the underscores:
flag{S3cretL1nksSh4redThr0ugh}
Resulted in a successful submission.
Tools & Resources Used
RedfoxSec Website – Initial background research.
LinkedIn – Primary source of investigation.
Base64/Base45/Base58 Decoders – Deciphering encoded text.
Dcode.fr – Identifying encryption methods.
Online QR Code Scanner – Assembling and analyzing QR fragments.
Google Drive Inspection – Identifying patterns in URL structures.
Lessons Learned / Takeaways
Examine employee profiles for irregularities. Subtle details in descriptions can reveal crucial leads.
Be proficient in various encoding schemes. Base64, Base45, Base58, and other ciphers are commonly used in OSINT challenges.
Analyze URLs for hidden clues. Sometimes, key elements of the flag are embedded within URL parameters.
Decoys are common. The QR code initially led to misleading information, requiring further investigation.
Rabbit Holes / Dead Ends
Checking the official website first. Contained general company details but no hidden clues.
Brute-forcing flag variations. Unsuccessful attempts before discovering the correct format.
Over-relying on the QR code. It served as a diversion rather than the direct solution.
Examining too many employee profiles. Only a select few contained relevant encoded information.
Final Verdict: This OSINT challenge demonstrated the importance of thorough digital investigation, cryptographic analysis, and pattern recognition. It required careful attention to details across multiple platforms, reinforcing the core principles of open-source intelligence gathering.
Subscribe to my newsletter
Read articles from Nayanesh directly inside your inbox. Subscribe to the newsletter, and don't miss out.
Written by
