Cyberstorm 2025 Writeup: Secure Coms [by Windows 9/11]
 Nayanesh
NayaneshCategory: Forensics
Team Name : Windows 9/11
Author: Nayanesh
CTF Writeup: Secure Coms Forensics Challenge
Challenge Description
Robin was able to get into Cipher Pol's secure network and has been trying to send back some intel. But Rob Lucci is on top of preventing any exfiltration by manually checking all the network packets for suspicious contents. Other members are not as paranoid it seems. Rob Lucci has some vested interest in protecting this piece of intel. Find out what Rob Lucci is protecting and ensure Robin's efforts don’t go in vain.
Attached: signal.pcapng
Initial Clues & Analysis
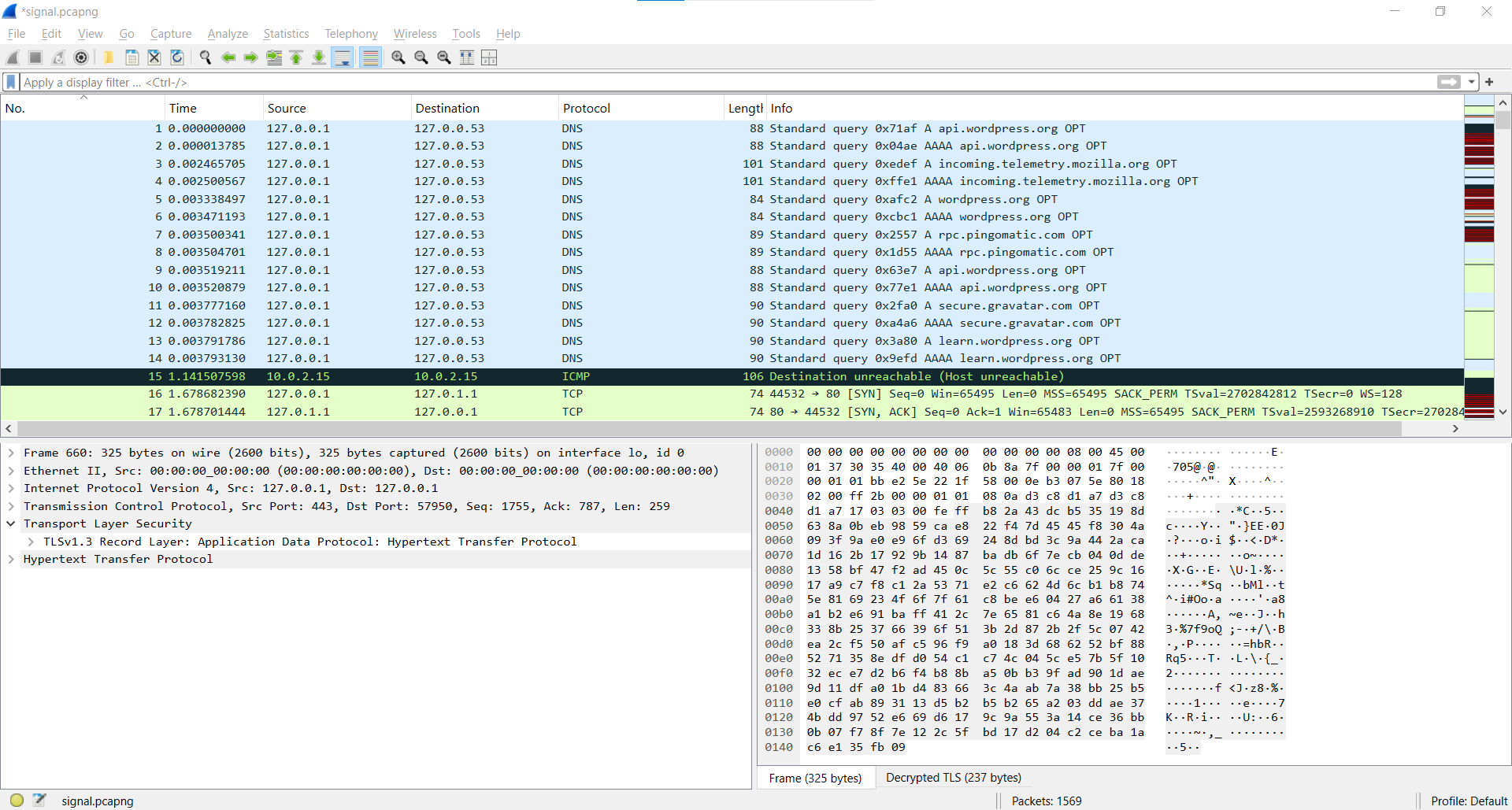
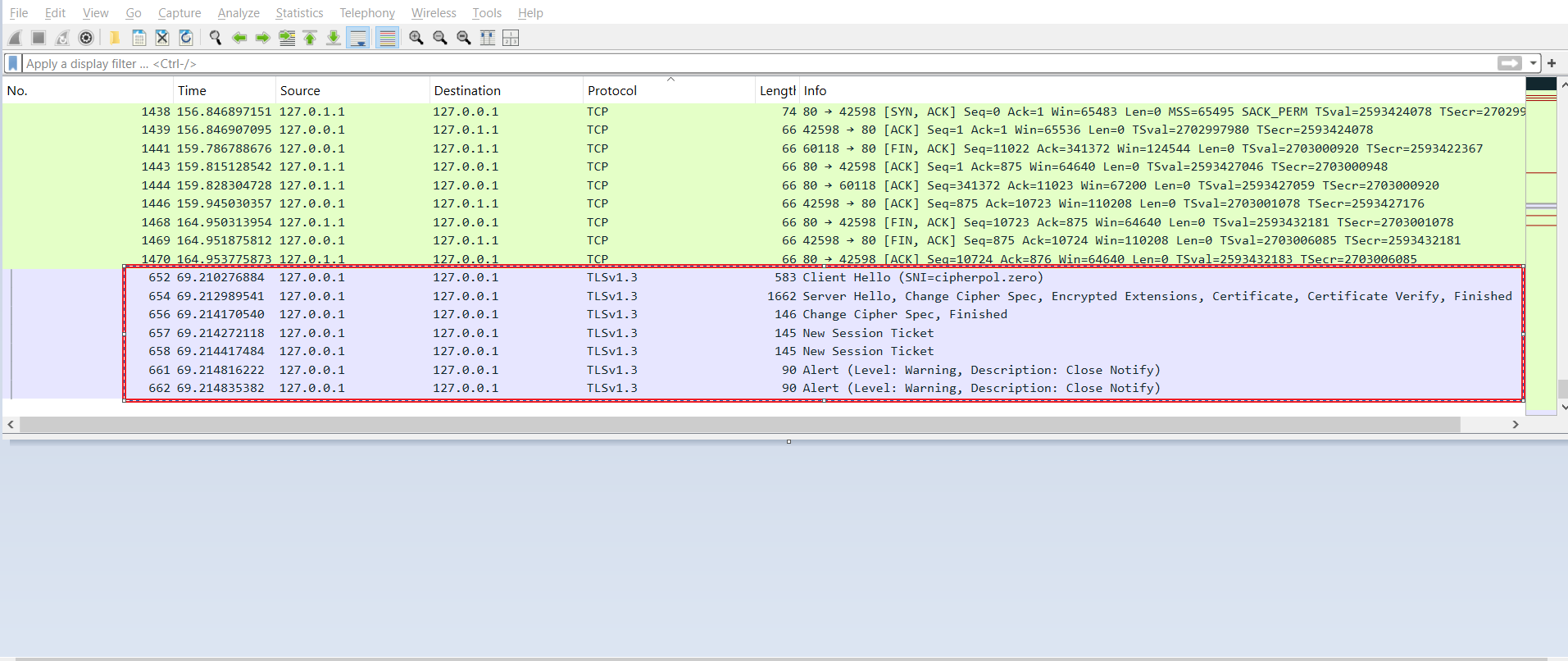
The challenge provided a .pcapng file, which is commonly used for packet capture analysis. My first approach was to inspect the file using Wireshark. Upon opening the file, I noticed various types of packets, including DNS, ICMP, TCP, and HTTP. Given the large number of packets (more than 1500), manually analyzing each packet was not feasible.
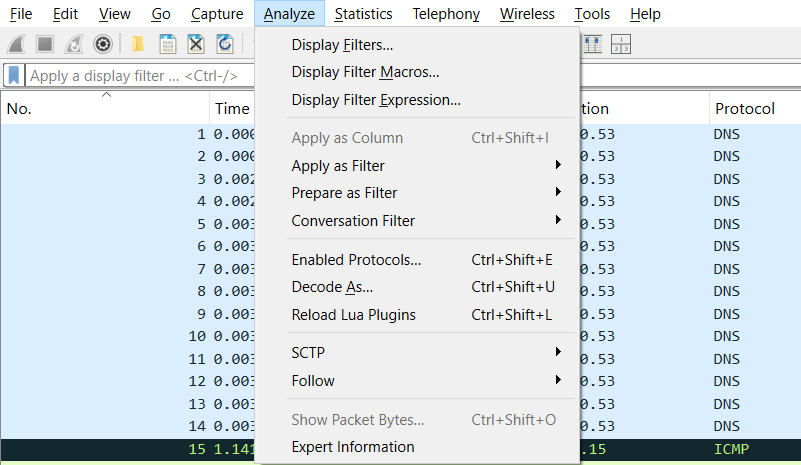
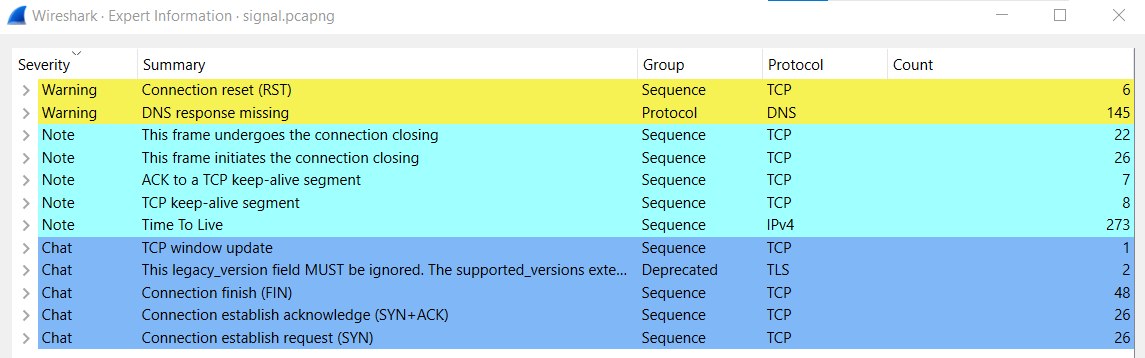
To narrow down the search, I used the Analyze > Expert Information feature in Wireshark to identify any malformed packets, but this did not reveal any useful leads.
Investigation Path
Step 1: Exporting HTTP Objects
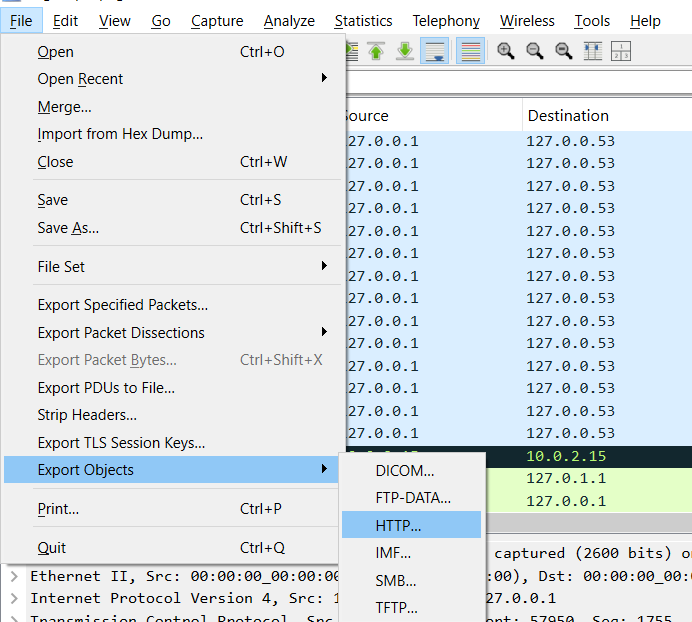
Since there were a significant number of HTTP packets, I decided to export all HTTP objects using File > Export Object > HTTP to analyze them separately.
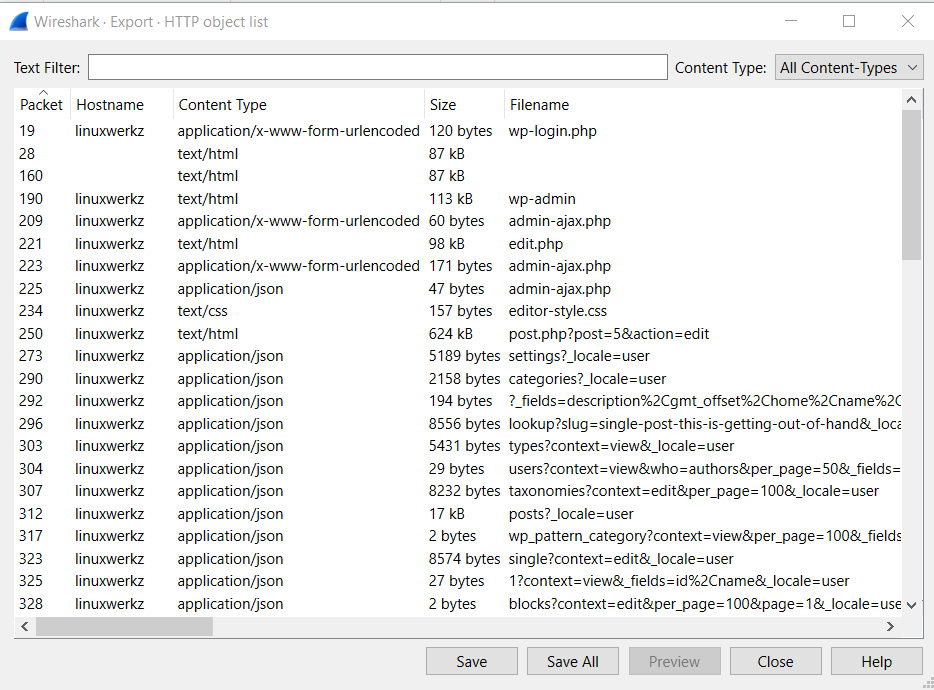
The export yielded around 20-30 files, including several PHP files (users.php, admin-ajax.php, index.php, edit.php). However, inspecting the source code of these files did not provide any useful information.
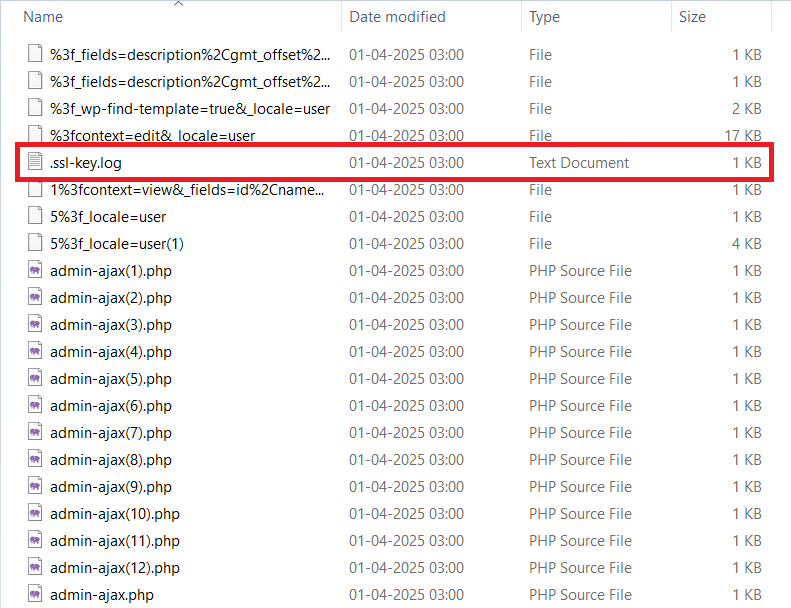
Among the exported files, I found a file named .ssl-key.log, which contained a TLS Secret Key. This key is used to decrypt encrypted network traffic in Wireshark.
Step 2: Injecting TLS Secret Key in Wireshark
To decrypt the encrypted TLS packets, I followed these steps:
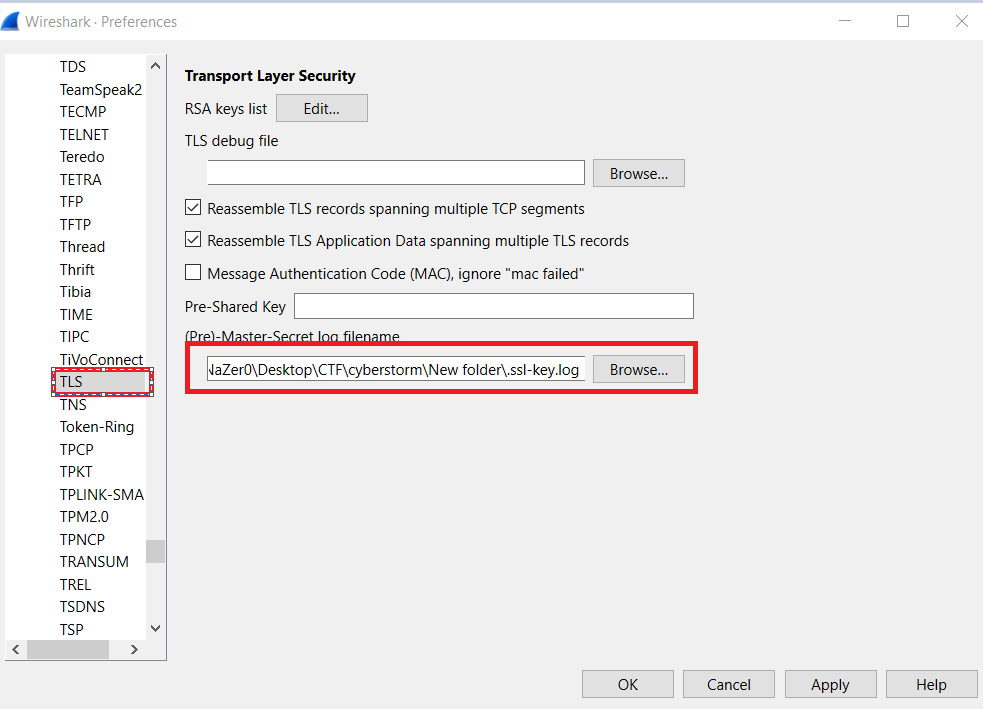
Open Wireshark and navigate to Edit > Preferences (Shortcut Ctrl+Shift+P).
Under the Protocols dropdown, select TLS.
In the (Pre) - Master-Secret log filename field, select the
.ssl-key.logfile and apply the changes.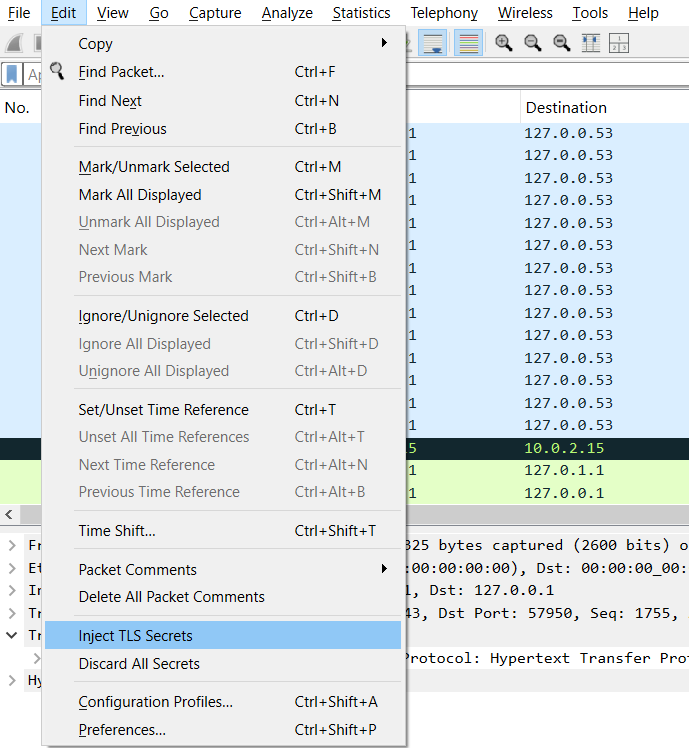
Then, I injected the SSL secret key by selecting Edit > Inject SSL Secret.
This resulted in decrypted TLSv1.3 packets appearing in the capture.
Step 3: Following the TLS Stream
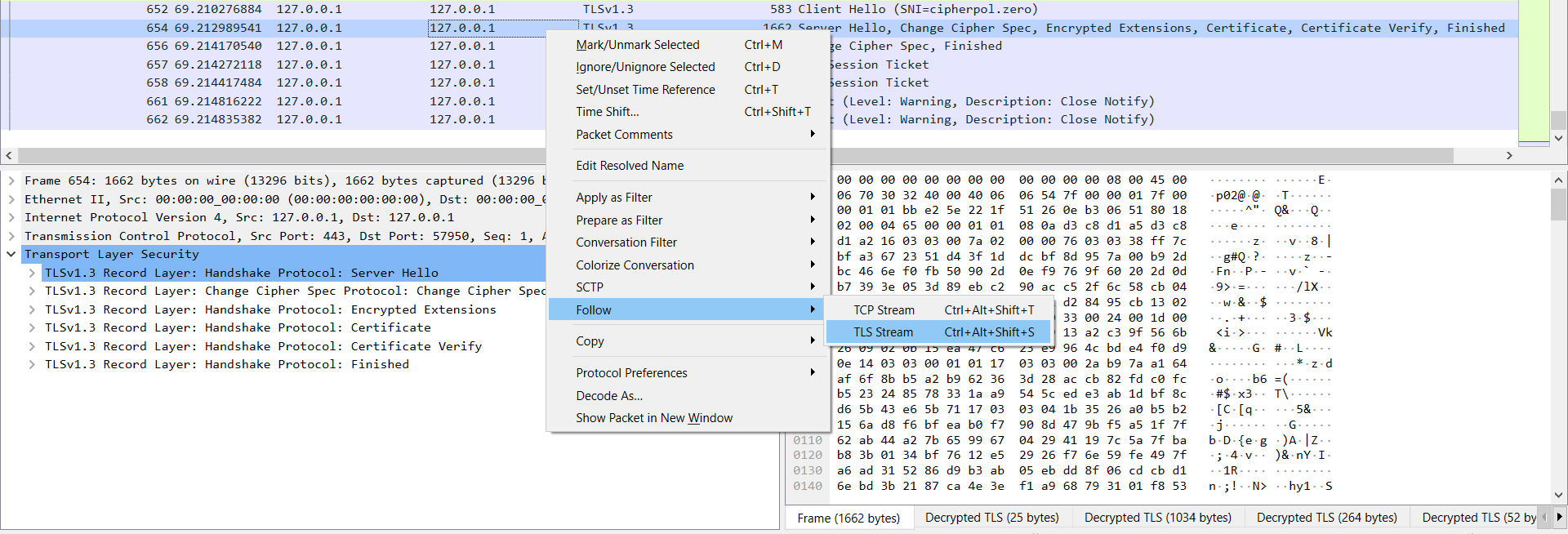
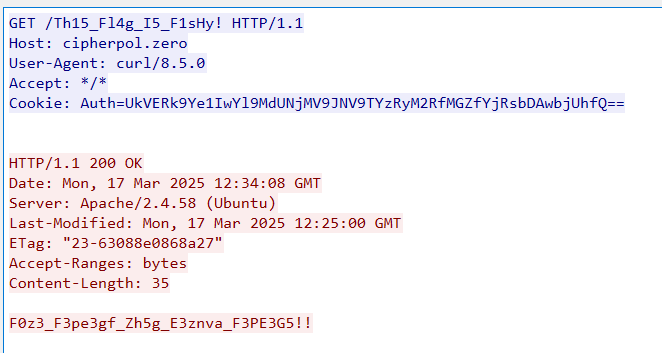
After decrypting the TLS packets, I right-clicked on one of them and selected Follow > TLS Stream. This revealed two pieces of interesting data:
Th15_Fl4g_I5_F1sHy!F0z3_F3pe3gf_Zh5g_E3znva_F3PE3G5!!
The first string appeared to be a complete flag, while the second one seemed incomplete.
Step 4: Decoding Base64 Encoded String
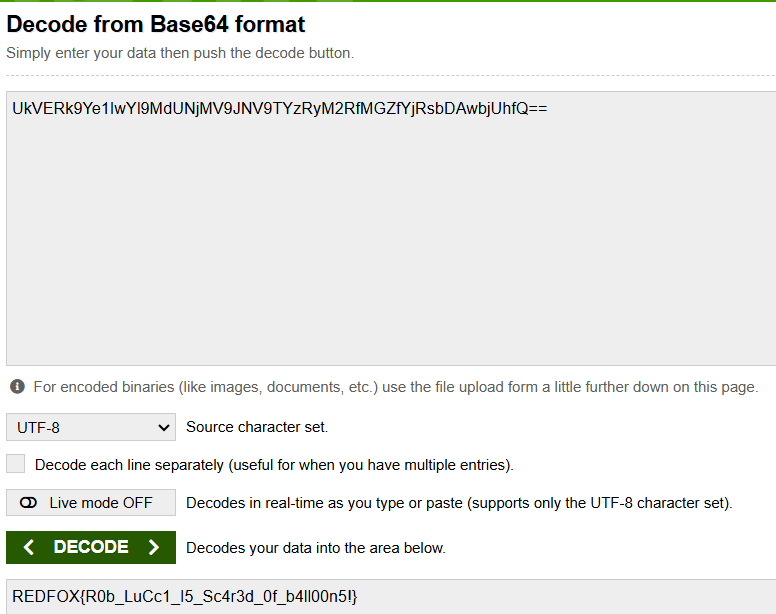
Within the data, I also found a Base64-encoded string. Base64-encoded data often ends with ==, which helped me identify it. Using an online Base64 decoder, I decoded the string and retrieved the final flag.
Finding the Flag
After decoding the Base64 string, I successfully retrieved the flag:
Flag: REDFOX{R0b_LuCc1_I5_Sc4r3d_0f_b4ll00n5!}
Tools & Resources Used
Wireshark: For analyzing network traffic and decrypting TLS packets.
Base64 Decoder: To decode the Base64-encoded string.
TLS Secret Key Injection: To decrypt HTTPS traffic in Wireshark.
Lessons Learned / Takeaways
Exporting Objects in Wireshark: Exporting HTTP objects is an efficient way to reduce the number of packets for analysis.
Decryption Techniques: Injecting a TLS secret key can reveal encrypted traffic, which is useful in forensic investigations.
Pattern Recognition: Identifying Base64-encoded strings using
==at the end helped in quickly recognizing and decoding it.Systematic Approach: Following a structured approach (checking malformed packets, exporting objects, decrypting traffic) helped in solving the challenge efficiently.
Rabbit Holes / Dead Ends
Initially, I spent time inspecting the PHP files extracted from the HTTP objects, but they contained no useful information. This reinforced the need to focus on network-level decryption instead of file content analysis.
More About
Wireshark
Wireshark is an open-source network protocol analyzer used for capturing and inspecting network traffic in real-time. It allows users to examine data packets at a granular level, helping with network troubleshooting, performance analysis, and cybersecurity investigations. Wireshark supports multiple protocols and provides detailed insights into packet structures. It is widely used by network administrators, security analysts, and developers. With features like filtering, live capture, and deep inspection, Wireshark is a valuable tool for understanding network behavior and identifying issues.
TLS Secret Key
A TLS Secret Key is a cryptographic key used in Transport Layer Security (TLS) to encrypt and decrypt communication between a client and a server. It ensures secure data transmission by preventing eavesdropping and tampering. The secret key is typically part of a key pair (public and private keys in asymmetric encryption) or a session key in symmetric encryption.
In Wireshark, you can use TLS secret keys (from SSLKEYLOGFILE) to decrypt encrypted HTTPS traffic for analysis, provided you have access to the necessary private keys.
Subscribe to my newsletter
Read articles from Nayanesh directly inside your inbox. Subscribe to the newsletter, and don't miss out.
Written by
