Understand the Cyber Kill Chain
 Ashwin Venkatakrishnan
Ashwin Venkatakrishnan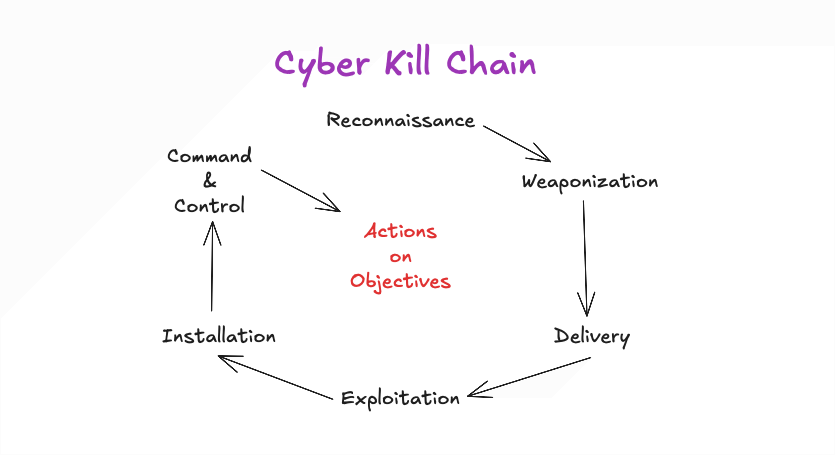
A Kill Chain is a military concept that defines the structure of an attack - target identification, decision and order to attack, and finally, target destruction.
Cyber Kill Chain is a framework established by Lockheed Martin for the cybersecurity industry in 2011 that defines the steps used by adversaries in cyberspace:
Reconnaissance
Weaponization
Delivery
Exploitation
Installation
Command & Control
Actions on Objectives
Reconnaissance
This is the planning phase where the goal is to identify targets. Adversaries discover and collect information on systems and victims through various sources and methods of intelligence gathering.
Here a some of the many sources of Intelligence:
Open-source Intelligence [OSINT] - information that is publicly available.
Closed-source Intelligence [CSINT] - not publicly available; insider information.
(Covert) Human Intelligence [(C)HUMINT] - information from human sources; agents, informants;
Signals Intelligence [SIGINT] - information from analyzing electronic signals; radio, radar, satellite, wire taps;
Geospatial Intelligence [GEOINT] - information from analyzing geographic data; satellite imagery, maps;
Financial Intelligence [FININT] - information from analyzing financial data; transactions, statements, records;
Measurement and Signature Intelligence [MASINT] - information from analyzing intrinsic characteristics of specific targets; type of aircraft or missile based on radar signature, type of computer based on serial number and MAC address;
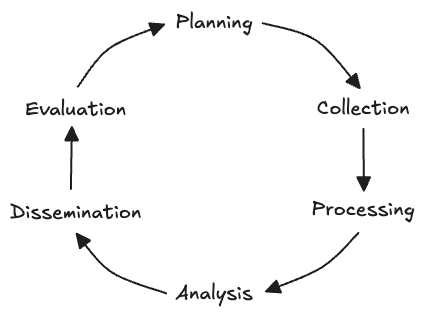
Intelligence Lifecycle:
Weaponization
Prepare the operation. After successful reconnaissance, adversaries develop or procure a deliverable payload - a combination of malware and exploit. Both malware and exploit can be procured from the Dark/Deep Web or developed. Advanced Persistent Threat (APT) groups and sophisticated actors are known to follow the latter approach to evade detection on the target.
With the payload ready, the adversary would identify a backdoor - an entry point to a system that bypasses security mechanisms - to implant the payload.
Delivery
Launch the operation. After the payload is prepared and a backdoor is identified, the adversary would decide on a delivery method for the payload. Some options are:
Phishing email
USB drive distribution / USB drop attack
Watering hole attack: Target a specific group of people by compromising a legitimate website that they frequently visit, implement a redirection mechanism
Exploitation
Gain access to the target. In this stage, the adversary delivers exploits to the target. If the target triggers the exploit, the adversary successfully gains access to the target’s system, allowing them to move laterally or escalate privileges. Lateral movement is a technique that attackers use to move deeper into the target’s network after gaining initial access. A zero-day - a vulnerability unknown to the developers/maintainers of software that an adversary can exploit - may instead be used by adversaries in this stage.
Installation
Establish beachhead at the target. Once the adversary gains access to the target system through a backdoor, their objective would be to maintain that access. This requires a persistent backdoorto be setup, which can be achieved through:
Web shell: A malicious script written in a web development language like ASP, JSP, or PHP. Given that scripts are used widely by websites, web shells tend to go under the radar due to their simplicity and file format (.php, .asp, .aspx, etc.).Meterpreter: A Metasploit Framework payload that installs a backdoor and gives a remote shell to execute malicious code on a target system.Windows Services: Use tools likescorRegto install and/or modify Windows services with malicious payloads to maintain access. Adversaries may alsomasqueradethe malicious payload using a service name related to the OS or legitimate software.Run keys: In the Windows Registry,Runkey can be defined to execute a program whenever a user login occurs. User-specific or system-wideRunkeys can be defined. UnlikeRunOncekeys, which get deleted after execution is triggered,Runkeys persist unless they are deleted explicitly. Cobalt Strike used this method.
To hide their actions, adversaries can also employ timestomping to modify file timestamps such as modify, access, and create times.
Command and Control (C2)
Remote control of the implanted payload. After persisting access to the target system, adversaries setup C2 to remote control the malware and manipulate the target system. The C2 infrastructure may be owned by the adversary or it may be another compromised host. In many cases, the malware tends to be simple/minimal and consistently contacts the adversary’s C2 server over a communication channel to perform malicious actions. This is called C2 Beaconing. Some of the communication channels used are:
IRC: While most security solutions can easily detect this channel today,IRCwas widely used as the communication method by malware to theC2server.HTTP/HTTPS: BlendsC2 beaconingtraffic with legitimate web traffic to evade firewalls.DNS Tunneling: Makes constantDNSrequests to an adversary-controlledDNSserver.
Actions on Objectives
Achieve the mission’s goal. With control over the target system established, adversaries can focus on the objectives of their mission, for example:
Credential collection
Privilege escalation
Internal reconnaissance
Lateral movement
Data exfiltration
Delete backups and shadow copies
Overwrite or corrupt data
Resources
Subscribe to my newsletter
Read articles from Ashwin Venkatakrishnan directly inside your inbox. Subscribe to the newsletter, and don't miss out.
Written by
