How to Test Twilio Webhooks Locally: A Step-by-Step Guide
 Robbie Cahill
Robbie Cahill
In the world of real-time communication, Twilio stands as a titan, offering powerful APIs for SMS, voice, video, and more. A cornerstone of its event-driven architecture is the webhook, a mechanism that pushes real-time data to your applications as events happen. Whether it's an incoming SMS, a new phone call, or a delivery status update, Twilio webhooks are the bridge between Twilio's cloud and your server.
However, developing and testing applications that consume these webhooks presents a classic development challenge. Twilio's servers live on the public internet, while your development environment typically runs on localhost. How can Twilio send a request to a server it can't reach?
This guide will walk you through the entire process of setting up, handling, and testing Twilio webhooks on your local machine. We'll build a simple Node.js application, and then use Tunnelmole, a powerful open-source tunneling tool, to expose our local server to the internet, creating a seamless development workflow. By the end, you'll be able to confidently build and debug Twilio integrations without ever leaving your local environment.
What Exactly is a Twilio Webhook?
Before we dive into the technical setup, let's clarify what a webhook is in the context of Twilio.
Think of a standard API call: your application initiates a request to a service (like Twilio) to fetch data or perform an action. For example, you call the Twilio API to send an SMS.
A webhook flips this model on its head. It’s a "reverse API." Instead of your application calling Twilio, Twilio calls your application. You provide Twilio with a publicly accessible URL endpoint. When a specific event occurs that you've subscribed to—like a customer sending an SMS to your Twilio phone number—Twilio's servers will immediately send an HTTP request (usually a POST request) to your URL with a payload of data describing that event.
This data payload is typically formatted as application/x-www-form-urlencoded and contains crucial information. For an incoming SMS, it would include:
From: The sender's phone number.To: Your Twilio phone number.Body: The content of the message.MessageSid: A unique identifier for the message.- And many other useful details.
Your application's job is to listen for these incoming requests, parse the data, and then take action. This action could be anything: storing the message in a database, triggering a workflow, or sending an automated reply.
This event-driven approach is incredibly powerful because it eliminates the need for your application to constantly poll Twilio's API to check for new messages or status changes, saving resources and providing true real-time responsiveness.
The Local Development Challenge: localhost vs. The Public Internet
When you run a web server on your development machine, whether it's a Node.js Express app, a Python Flask server, or a Ruby on Rails instance, it typically binds to localhost (or its IP address equivalent, 127.0.0.1). This address is special; it's a loopback interface that tells the operating system, "this traffic is meant for this same machine."
This is great for security and isolation during development. You can access your application by opening a browser and navigating to http://localhost:3000, but no one else on the internet can.
And therein lies the problem for Twilio webhooks.
When you configure a webhook in your Twilio console, you must provide a URL. If you were to enter http://localhost:3000/sms, Twilio's servers would attempt to send a request to that address. From their perspective on the public internet, localhost points to their own machine, not yours. The request would go nowhere, and your local application would never receive the notification.
To solve this, your local server needs a temporary public address. This is where tunneling tools come in.
Introducing Tunnelmole: Your Local Server's Bridge to the World
To receive Twilio's webhook requests, we need a tool that can create a secure tunnel from a public URL on the internet directly to our application running on localhost. For this task, we will use Tunnelmole.
Tunnelmole is a free and open-source command-line tool that instantly gives your local services a public HTTPS URL. It’s lightweight, easy to use, and requires no complicated network configuration.
Key features that make Tunnelmole ideal for this workflow include:
- Open Source: The client and server are fully open source, giving you complete transparency and control. You can inspect the code to see exactly how it works.
- Self-Hostable: While Tunnelmole offers a convenient public service, you can also self-host the server component for ultimate privacy and the ability to use your own domains.
- Simple CLI: Getting a public URL is as simple as running a single command:
tmole <port>. - Secure HTTPS: Tunnelmole provides HTTPS URLs by default, which is a requirement for many modern webhook providers and a best practice for security.
How Tunnelmole Works
The concept behind Tunnelmole is straightforward but powerful.
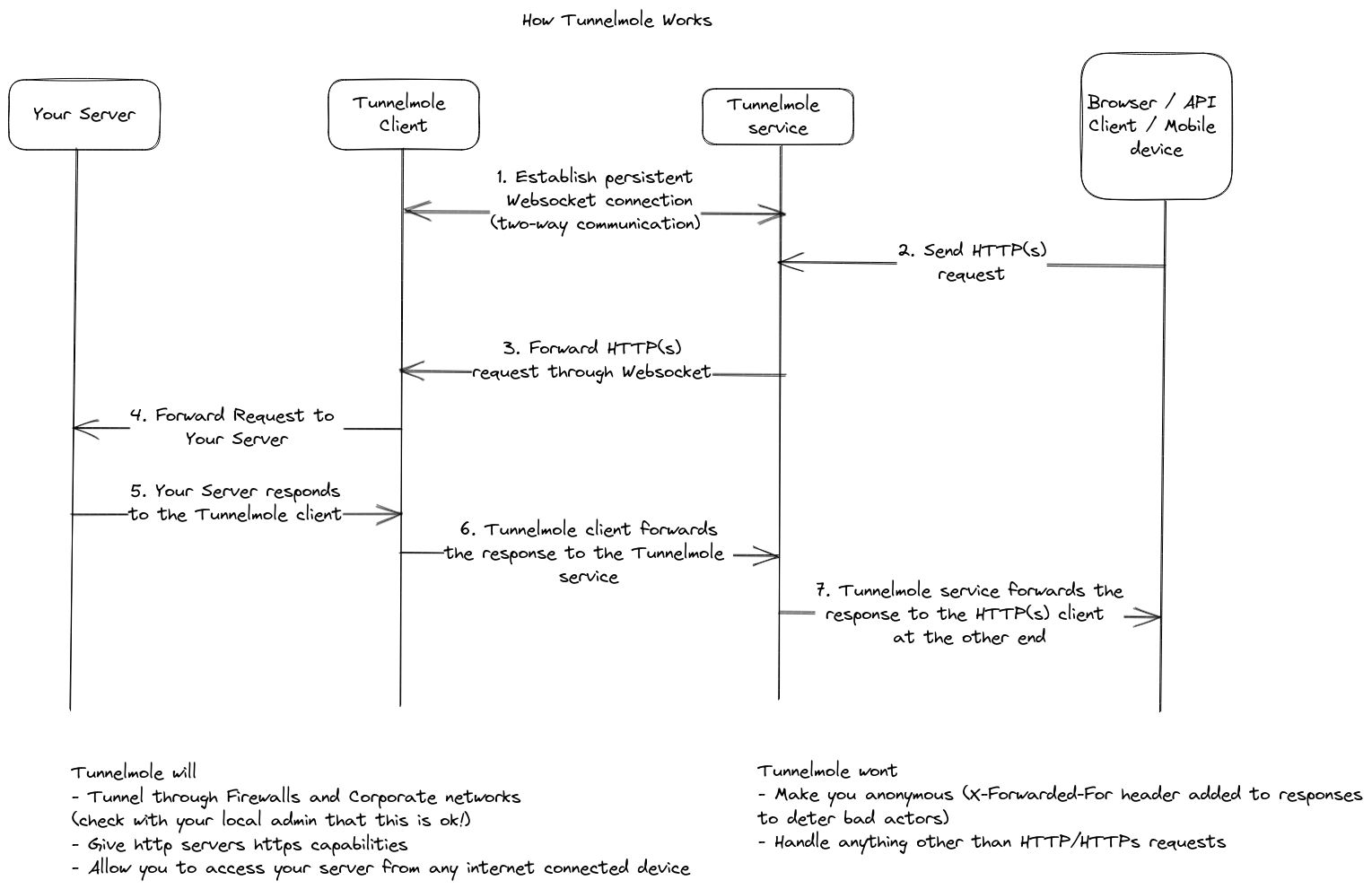
- Client Connection: You run the Tunnelmole client (
tmole) on your machine. It establishes a persistent, secure connection to the Tunnelmole service running on the public internet. - Public URL Generation: The Tunnelmole service generates a unique public URL (e.g.,
https://random-id.tunnelmole.net) and assigns it to your connection. - Request Forwarding: When Twilio (or any other service) sends an HTTP request to your public Tunnelmole URL, the Tunnelmole service receives it.
- Tunneling: The service then forwards that exact request down the secure tunnel to the Tunnelmole client on your machine.
- Local Delivery: The client delivers the request to your local web server running on the specified port (e.g.,
localhost:3000). - Response Handling: The response from your local server travels back through the same tunnel to the Tunnelmole service, which then delivers it back to Twilio.
This entire process happens very quickly, creating a seamless link that makes your local application behave as if it were deployed on a public server.
Step-by-Step Guide: Handling Twilio SMS Webhooks Locally
Let's get our hands dirty and build a complete end-to-end solution. We will create a Node.js application that listens for incoming SMS messages from Twilio, logs them, and sends a reply.
Prerequisites
Before you begin, make sure you have the following:
- A Twilio Account: If you don't have one, you can sign up for a free trial account. The trial provides you with a phone number and free credits.
- Node.js and npm: This guide uses Node.js. Download it from the official Node.js website. Npm is included with the installation.
- A Twilio Phone Number: From your Twilio console, acquire a phone number that is capable of sending and receiving SMS messages.
Step 1: Create a Basic Node.js Express Server
First, let's set up a simple web server using the popular Express framework. This server will have a single endpoint, /twilio-webhook, to handle incoming requests from Twilio.
Create a new project directory, navigate into it, and initialize a new Node.js project.
mkdir twilio-webhook-app
cd twilio-webhook-app
npm init -y
Next, install Express and body-parser, a middleware to help us parse the incoming request data.
npm install express body-parser
Now, create a file named index.js and add the following code:
const express = require('express');
const bodyParser = require('body-parser');
const app = express();
const port = 3000;
// Twilio sends its requests as 'application/x-www-form-urlencoded',
// so we need to use the 'urlencoded' middleware to parse it.
app.use(bodyParser.urlencoded({ extended: false }));
// Define our webhook endpoint
app.post('/twilio-webhook', (req, res) => {
console.log('🎉 Webhook Received!');
const from = req.body.From;
const to = req.body.To;
const body = req.body.Body;
console.log(`From: ${from}`);
console.log(`To: ${to}`);
console.log(`Message: "${body}"`);
// We'll add a response later. For now, just send a 200 OK.
res.status(200).send('Webhook received');
});
app.listen(port, () => {
console.log(`🚀 Server listening at http://localhost:${port}`);
});
Let's break down this code:
- We initialize an Express application.
- We use
bodyParser.urlencoded()to correctly parse the data format that Twilio uses for its webhooks. This middleware populates thereq.bodyobject with the webhook data. - We define a
POSTroute at/twilio-webhook. This is where Twilio will send its requests. - Inside the route handler, we log a confirmation message and then print the core details of the SMS: the sender (
From), the recipient (To), and the message content (Body). - Finally, we start the server on port
3000.
Start your server by running:
node index.js
You should see the message: 🚀 Server listening at http://localhost:3000. Your local endpoint is now live.
Step 2: Install and Run Tunnelmole
Now it's time to make our local server accessible to Twilio. Let's install and run Tunnelmole.
The quickest way to install Tunnelmole on Linux or macOS is with the following command:
curl -O https://install.tunnelmole.com/xD345/install && sudo bash install
For Windows or other installation methods, including NPM, check out the official Tunnelmole installation docs.
With Tunnelmole installed, open a new terminal window (leave your Node.js server running in the first one) and run the following command to expose your server on port 3000:
tmole 3000
Tunnelmole will start up and display output similar to this:
Your Tunnelmole Public URLs are below and are accessible internet wide. Always use HTTPs for the best security
https://cqcu2t-ip-49-185-26-79.tunnelmole.net ⟶ http://localhost:3000
http://cqcu2t-ip-49-185-26-79.tunnelmole.net ⟶ http://localhost:3000
This is the magic moment. The URL starting with https:// is your new public address. Copy this HTTPS URL. Any request sent to it will be instantly forwarded to your local server running on http://localhost:3000.
Step 3: Configure the Webhook in Your Twilio Console
With our public URL in hand, we need to tell Twilio where to send the webhook.
- Log in to your Twilio Console.
- Navigate to the Phone Numbers section in the left-hand menu, then go to Manage > Active numbers.
- Click on the Twilio phone number you want to use for testing.
- Scroll down to the Messaging configuration section.
- Find the line that says "A MESSAGE COMES IN". Next to it, there is a dropdown set to "Webhook".
- In the text box, paste your public HTTPS URL from Tunnelmole, and be sure to append your endpoint path
/twilio-webhook. The final URL should look like this:https://cqcu2t-ip-49-185-26-79.tunnelmole.net/twilio-webhook. - Ensure the method is set to
HTTP POST. - Click the Save button at the bottom of the page.
Twilio is now configured. Whenever this phone number receives an SMS, Twilio will send a POST request to your Tunnelmole URL.
Step 4: Test Your First Webhook!
This is the moment of truth.
Using your personal mobile phone, send an SMS message to your Twilio phone number.
Now, look at the terminal where your Node.js server is running. After a few seconds, you should see the following output:
🎉 Webhook Received!
From: +14155552671 // Your mobile number
To: +15017122661 // Your Twilio number
Message: "Hello from my phone!"
Success! Twilio successfully sent the webhook, Tunnelmole tunneled it to your local machine, and your Express app processed it. You have now mastered the fundamental workflow for local Twilio webhook development.
Taking it Further: Responding with TwiML
Simply receiving a webhook is useful, but the real power of Twilio comes from the ability to respond and create interactive experiences. You can do this using TwiML (Twilio Markup Language).
TwiML is a set of XML tags that instruct Twilio on what to do next. You can use it to send a reply SMS, make an outbound call, play audio, and much more. When Twilio sends you a webhook, it expects a TwiML document in your HTTP response.
Let's modify our application to automatically reply to every incoming SMS.
First, we need to install the official Twilio Node.js helper library, which makes generating TwiML a breeze.
npm install twilio
Now, update your index.js file with the following code:
const express = require('express');
const bodyParser = require('body-parser');
const twilio = require('twilio');
const MessagingResponse = twilio.twiml.MessagingResponse;
const app = express();
const port = 3000;
app.use(bodyParser.urlencoded({ extended: false }));
app.post('/twilio-webhook', (req, res) => {
console.log('🎉 Webhook Received!');
const from = req.body.From;
const body = req.body.Body;
console.log(`From: ${from}, Message: "${body}"`);
// Create a new TwiML response
const twiml = new MessagingResponse();
// Add a <Message> verb to the TwiML
twiml.message(`Thanks for your message! You said: "${body}"`);
// Set the response content type to XML and send the TwiML
res.writeHead(200, { 'Content-Type': 'text/xml' });
res.end(twiml.toString());
});
app.listen(port, () => {
console.log(`🚀 Server listening at http://localhost:${port}`);
});
What did we change?
- We imported the
MessagingResponseobject from thetwiliolibrary. - Inside our webhook handler, after logging the incoming message, we create a new
MessagingResponseinstance. - We use the
twiml.message()method to add a<Message>instruction to our response. This tells Twilio to send a reply SMS. - Critically, we set the
Content-Typeheader of our HTTP response totext/xml. - Finally, we send the generated TwiML string as the response body. The resulting XML will look something like this:
<?xml version="1.0" encoding="UTF-8"?> <Response> <Message>Thanks for your message! You said: "Hello again!"</Message> </Response>
Stop and restart your Node.js server to apply the changes (Ctrl+C, then node index.js). Your Tunnelmole tunnel will remain active and does not need to be restarted.
Now, send another SMS to your Twilio number. You'll see the message logged in your console as before, but this time, you will receive an automated reply on your phone!
Essential Practice: Securing Your Webhook
Your webhook endpoint is currently open to the public internet. Anyone who knows your Tunnelmole URL could send fake requests to it, potentially triggering unwanted actions or abusing your service. This is a serious security risk.
Twilio provides a robust mechanism to prevent this: request validation.
When Twilio sends a request to your webhook URL, it includes a special HTTP header called X-Twilio-Signature. This signature is a hash of the request URL and its parameters, created using your unique Twilio Auth Token as the key.
Your application can recalculate this signature using the same information and compare it to the one Twilio sent. If they match, you can be certain the request is authentic and came from Twilio.
The Twilio helper library makes this validation simple. Let's add it to our app.
First, you need your Twilio Auth Token. Treat this like a password and never commit it to public source control. Find it on your Twilio Console dashboard. The best practice is to store it in an environment variable.
For this example, we'll temporarily place it in our code, but remember to use environment variables for real projects.
Update index.js one last time:
const express = require('express');
const bodyParser = require('body-parser');
const twilio = require('twilio');
// IMPORTANT: Replace with your Auth Token. Use environment variables in production!
const TWILIO_AUTH_TOKEN = 'your_auth_token_here';
const MessagingResponse = twilio.twiml.MessagingResponse;
const app = express();
const port = 3000;
// Body parser must run before the validation middleware
app.use(bodyParser.urlencoded({ extended: false }));
// Twilio Validation Middleware
app.post('/twilio-webhook', (req, res, next) => {
// The 'x-forwarded-proto' header is important when using a tunnel like Tunnelmole
const protocol = req.headers['x-forwarded-proto'] || req.protocol;
const fullUrl = protocol + '://' + req.get('host') + req.originalUrl;
const twilioSignature = req.headers['x-twilio-signature'];
// The 'twilio.validateRequest' function will return 'true' if the request is valid
const requestIsValid = twilio.validateRequest(
TWILIO_AUTH_TOKEN,
twilioSignature,
fullUrl,
req.body
);
if (requestIsValid) {
next(); // Request is valid, proceed to the next handler
} else {
console.error('🚫 Invalid Twilio Signature. Request blocked.');
res.status(403).send('Forbidden: Invalid Twilio Signature');
}
});
// Webhook Handler (now runs only if validation passes)
app.post('/twilio-webhook', (req, res) => {
console.log('🎉 Webhook Received and Validated!');
const body = req.body.Body;
const twiml = new MessagingResponse();
twiml.message(`Your signature was valid! You said: "${body}"`);
res.writeHead(200, { 'Content-Type': 'text/xml' });
res.end(twiml.toString());
});
app.listen(port, () => {
console.log(`🚀 Server listening at http://localhost:${port}`);
});
Key changes in the security update:
- We've added a middleware function that runs before our main webhook handler for the
/twilio-webhookroute. - We construct the
fullUrlthat Twilio used to sign the request. Note: When using a proxy or tunnel like Tunnelmole, the original protocol (https) is often stored in thex-forwarded-protoheader. This is a crucial detail for validation to work correctly behind a tunnel. - We call
twilio.validateRequest()with our Auth Token, the signature from the header, the URL, and the raw request body. - If validation passes, we call
next()to proceed to our main logic. If it fails, we send a403 Forbiddenresponse and block the request.
Restart your server, send another SMS, and everything should work as before, but now your endpoint is secure.
Conclusion
Twilio webhooks are a fundamental part of building powerful, real-time communication applications. While local development presents the initial hurdle of bridging the gap between the public internet and your localhost environment, tools like Tunnelmole make solving this problem trivial.
In this guide, we've walked through the entire lifecycle:
- We understood the role of webhooks in Twilio's architecture.
- We built a Node.js server to handle incoming webhook requests.
- We used the open-source tool Tunnelmole to instantly get a public HTTPS URL for our local server.
- We configured and tested an SMS webhook from the Twilio console.
- We learned how to create interactive replies using TwiML.
- We secured our endpoint by implementing Twilio's request validation.
With this workflow, you can now rapidly iterate, debug, and test your Twilio applications with the speed and convenience of a local development setup. Happy building!
Subscribe to my newsletter
Read articles from Robbie Cahill directly inside your inbox. Subscribe to the newsletter, and don't miss out.
Written by
