1. Amazon Elastic Compute Cloud (EC2) - Introduction
 Arindam Baidya
Arindam Baidya
Background what and why of EC2
Welcome to this introductory lesson on Amazon Elastic Compute Cloud (EC2). In this guide, we’ll explore the evolution of compute, the limitations of traditional data centers, and how EC2 transforms the way you deploy and manage applications in the cloud.
Challenges of Traditional Data Centers
In the 1980s and 1990s, organizations depended on on-premises data centers, facing:
Lengthy Provisioning
Ordering, racking, and configuring hardware could take weeks or months.High Upfront Costs
Capital expenditures for servers, networking, and storage were significant.Maintenance Overhead
Hardware failures, patch management, and firmware upgrades required dedicated teams.Limited Agility
Scaling up or down on demand was virtually impossible without overprovisioning.
To accommodate peak loads, companies often overestimated capacity, tying up capital and reducing operational flexibility.
Emergence of Virtualization
The early 2000s saw the rise of virtualization, which enabled multiple virtual machines (VMs) to run on a single physical server. Key benefits included:
Improved Resource Utilization
Faster Recovery and simplified maintenance
On-Demand Flexibility for deploying new workloads
Virtualization set the stage for cloud computing by decoupling hardware from software.
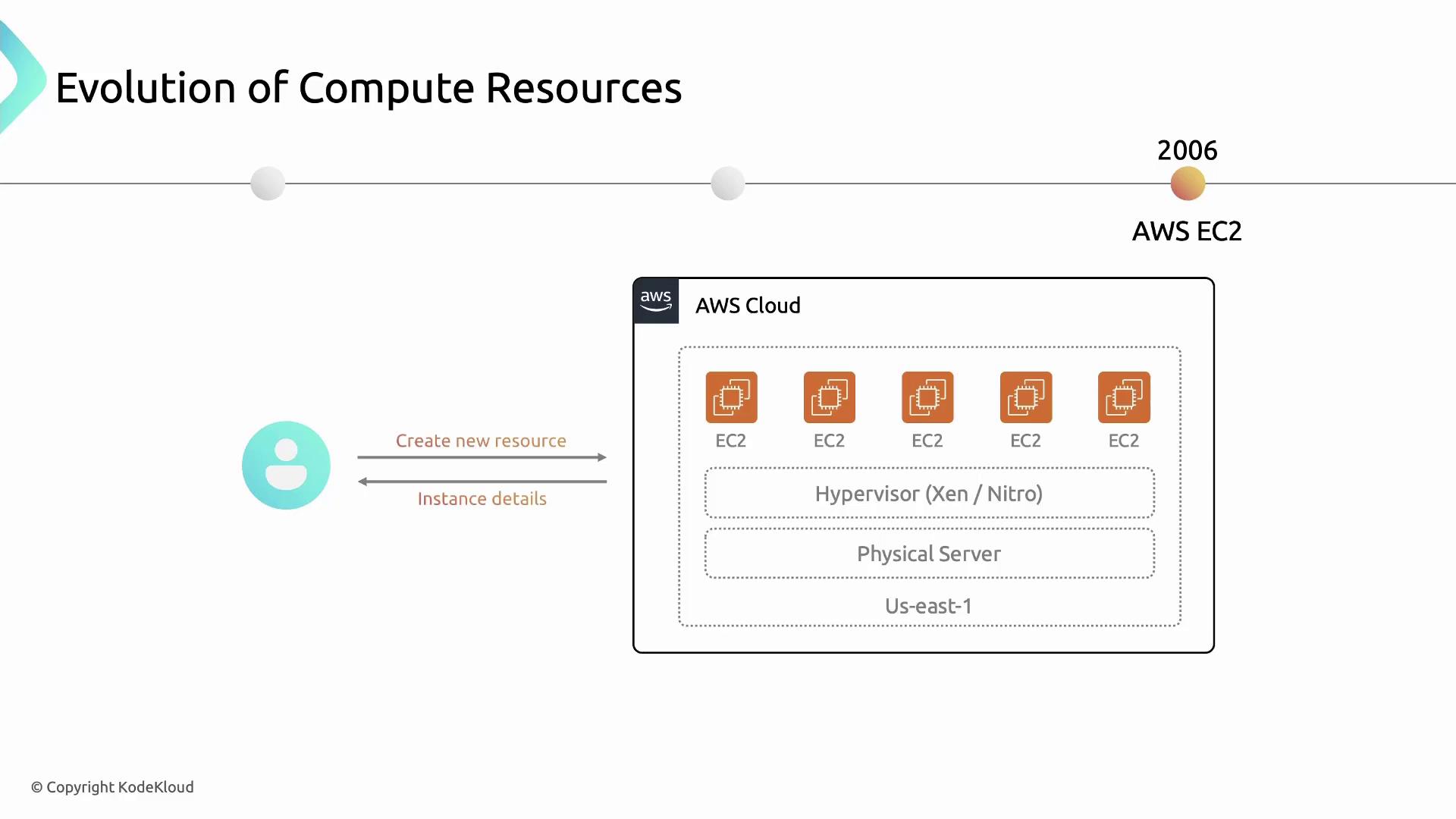
Introducing Amazon EC2
Amazon EC2 (launched in 2006) provides secure, resizable compute capacity in the AWS Cloud. Instead of procuring physical servers, you launch virtual instances with the CPU, memory, storage, and networking capacity you need.
Note
With EC2, provisioning a new server takes minutes instead of months—accelerating development cycles and innovation.
Key Features of Amazon EC2
Amazon EC2 offers a rich set of features to support diverse workloads:
1. Instance Families
Choose from multiple instance families optimized for different use cases:
| Instance Family | Use Case | Example Types |
| General Purpose | Balanced CPU & memory | t3.micro, m5.large |
| Compute Optimized | Compute-intensive applications | c5.large, c6g.medium |
| Memory Optimized | Memory-bound workloads | r5.xlarge, x1e.2xlarge |
| Storage Optimized | High I/O performance | i3.large, d3en.4xlarge |
| Accelerated Computing | GPU/FPGA-based parallel processing | p3.2xlarge, f1.4xlarge |
2. Flexible Pricing Models
Optimize costs with multiple pricing options:
| Pricing Model | Description | Best For |
| On-Demand | Pay per second for compute resources | Short-term, unpredictable workloads |
| Reserved Instances | Commit to 1–3 year term for discounts | Steady-state, long-running workloads |
| Spot Instances | Bid on spare capacity for up to 90% off On-Demand | Fault-tolerant, flexible applications |
| Savings Plans | Flexible discount model across compute usage | Predictable usage across AWS services |
Warning
Provisioning the wrong instance type or pricing model can lead to unexpected costs. Always analyze your workload patterns first.
3. High Availability & Reliability
Regions & Availability Zones
Distribute instances across multiple AZs for fault tolerance.Automated Hardware Replacement
AWS monitors and remediates failed hardware.
Learn more: AWS Regions and Availability Zones
4. Elastic Scaling
Auto Scaling
Automatically adjust capacity in response to demand.Elastic Load Balancing
Distribute incoming traffic across healthy instances.
Learn more: Amazon EC2 Auto Scaling, Elastic Load Balancing
5. Customization & Control
Amazon Machine Images (AMIs)
Preconfigure OS, application server, and applications.User Data & CloudInit
Automate instance initialization scripts.
Learn more: AMI Overview
6. Integration with AWS Services
EC2 works seamlessly with the broader AWS ecosystem:
| Service | Purpose |
| Amazon S3 | Object storage |
| Amazon RDS | Managed relational databases |
| AWS VPC | Virtual networking |
| AWS IAM | Secure access control |
| AWS CloudWatch | Monitoring and observability |
Introduction to VPC subnet route table internet gateway and nat gateway
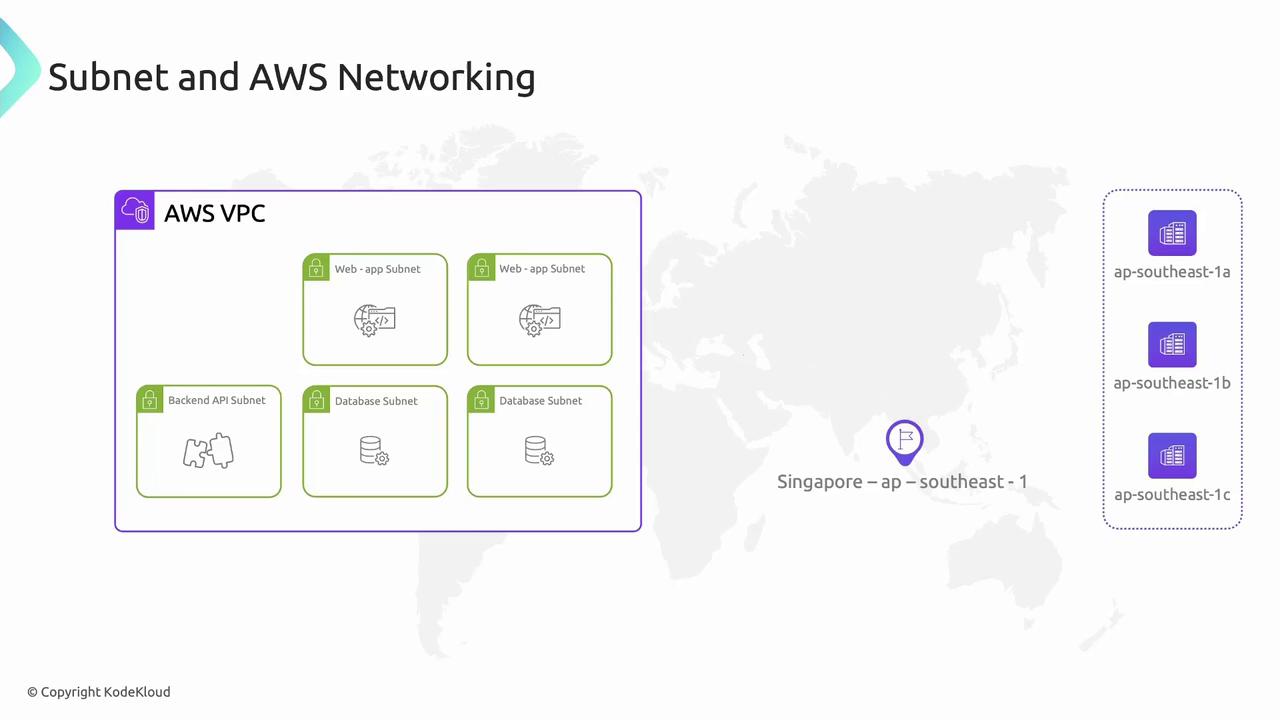
Amazon Web Services (AWS) provides a global, highly reliable backbone to deploy secure and scalable network architectures. In this guide, you’ll learn how VPCs, subnets, route tables, Internet Gateways, and NAT Gateways work together to isolate and manage traffic for your EC2 instances.
First, let’s explore AWS’s global footprint:

AWS Regions are fully isolated geographic areas. Each Region contains multiple Availability Zones (AZs)—separate data centers that ensure fault tolerance and high availability. Behind the scenes, the AWS Backbone Network securely interconnects Regions and edge locations for low-latency, high-throughput performance.
Virtual Private Cloud (VPC): Your Private Network
A Virtual Private Cloud (VPC) is your own private, logically isolated section of the AWS Cloud. It acts like a gated community, where you control who enters, leaves, and communicates internally.
Key VPC capabilities:
| Feature | Description |
| Isolation | Logical separation from other AWS accounts |
| Customizable IP Range | Define your own CIDR block and segment with subnets |
| Hybrid Connectivity | Connect on-premises via VPN, Direct Connect, and VPC Peering |
| AWS Service Integration | Seamlessly integrates with EC2, RDS, ELB, Lambda, and more |

Note
Remember: VPCs do not span Regions. Resources in one Region (and its AZs) cannot communicate with resources in another without a peer connection or VPN.
Subnets: Segmenting Your VPC
Subnets subdivide a VPC into smaller IP ranges within a single AZ—like dividing a housing lane into individual plots. Use subnets to isolate workloads (web servers, APIs, databases) based on security and routing needs.
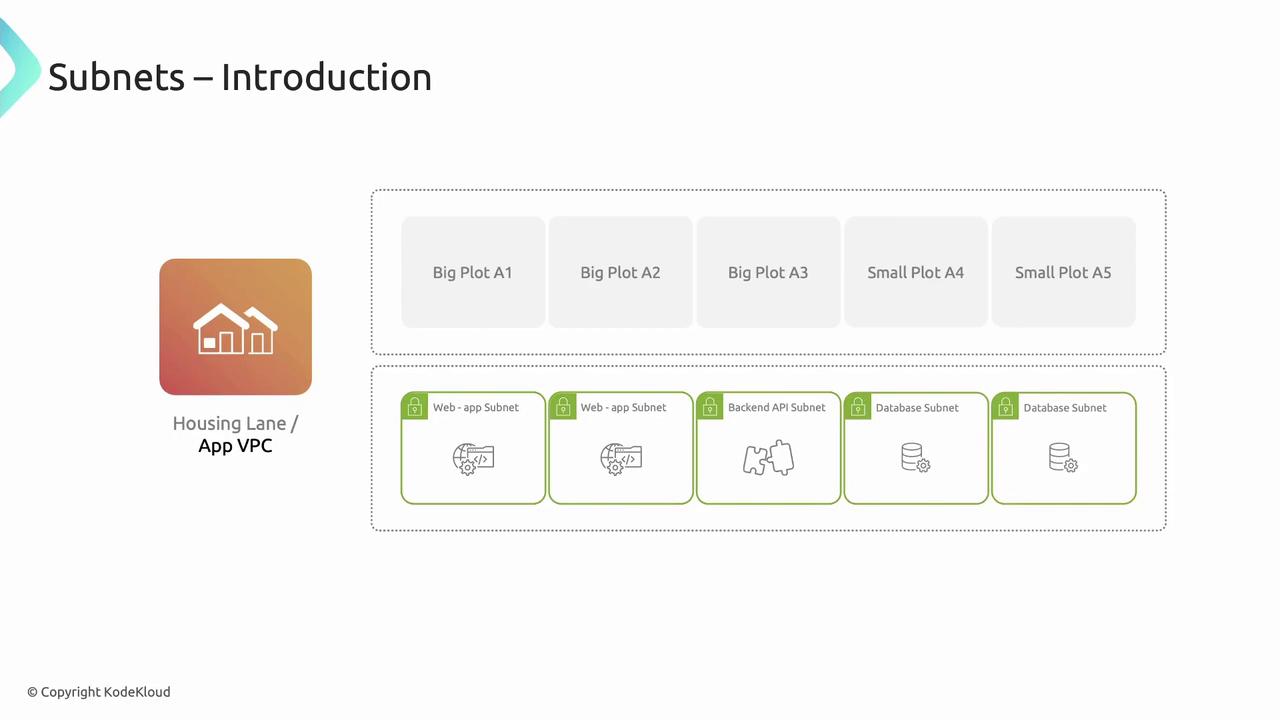
By placing subnets in multiple AZs, you build high-availability architectures:
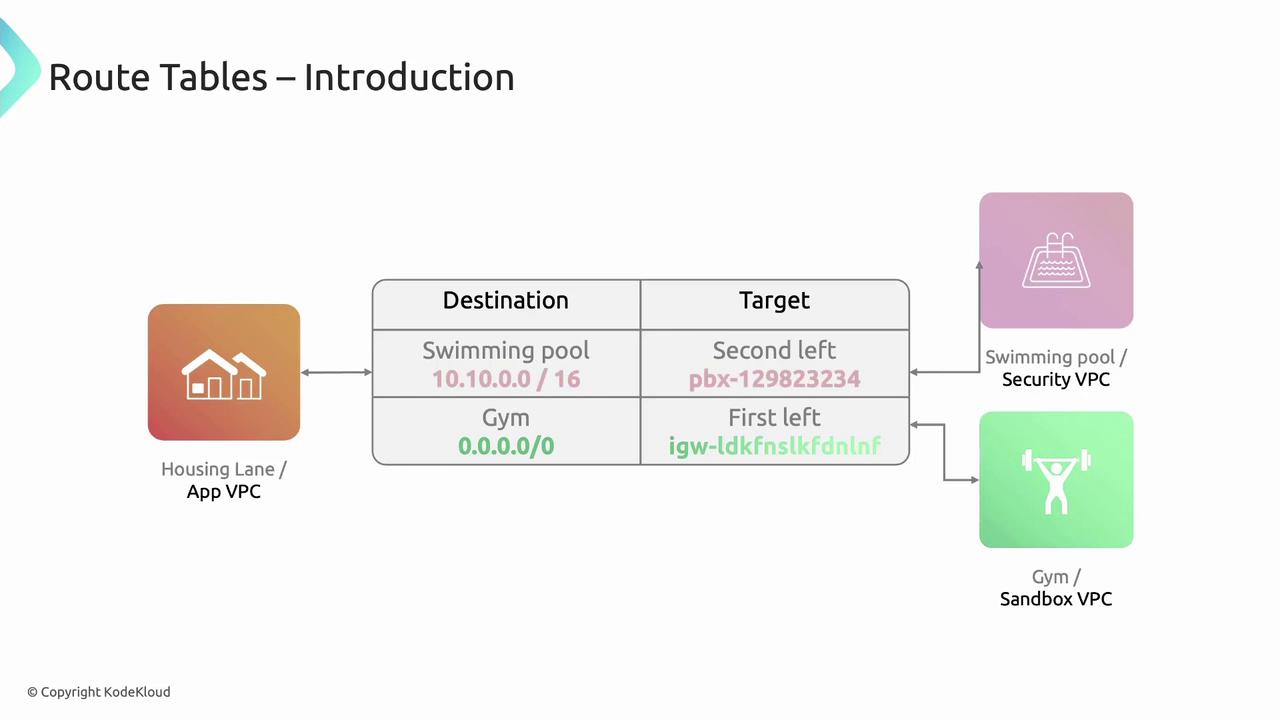
Route Tables: Traffic Signposts
Route tables control how packets flow between subnets, VPC peering connections, Internet Gateways, and NAT Gateways. Each entry maps a destination CIDR to a target.
Example “App VPC” route table:
| Destination | Target |
| 10.10.0.0/16 | VPC Peering Connection |
| 0.0.0.0/0 | Internet Gateway (igw-xxxx) |
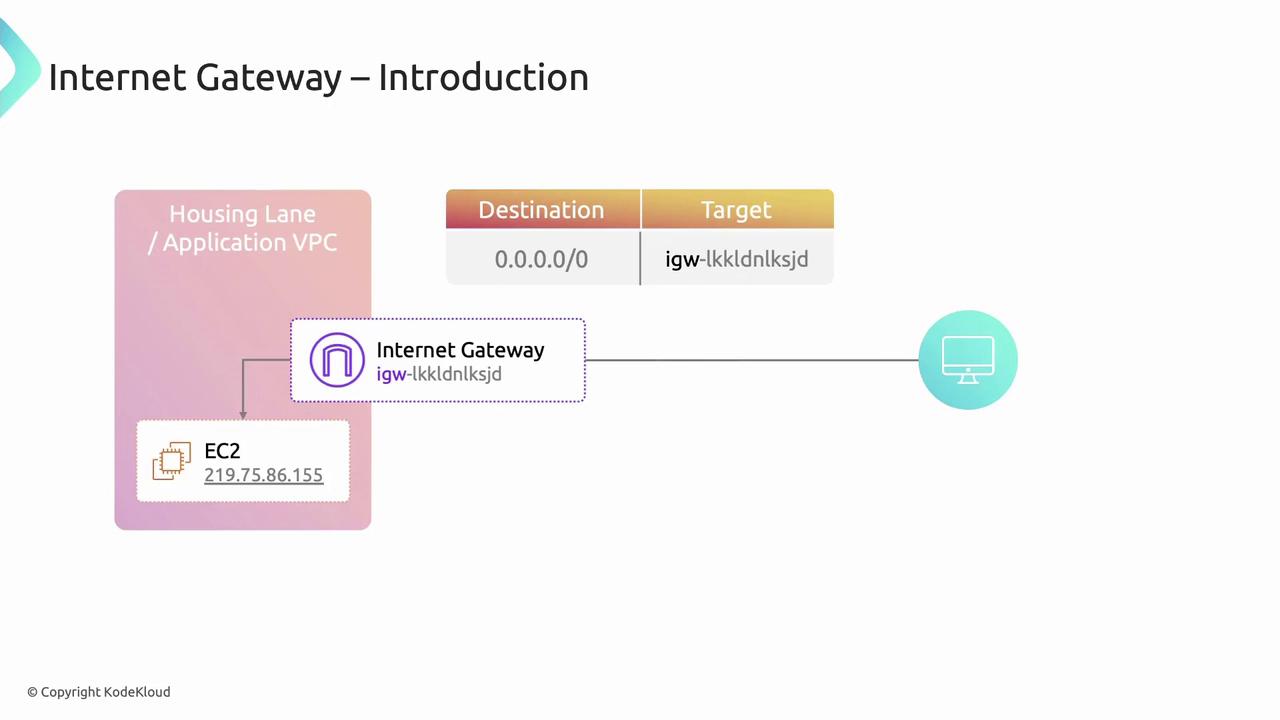
Internet Gateway: Public Access Point
An Internet Gateway (IGW) is a horizontally scaled, redundant VPC component that allows communication between your VPC and the Internet.
To enable Internet access for a subnet:
Create and attach an IGW to your VPC.
Add a route to your route table:
Destination:
0.0.0.0/0Target:
igw-<gateway-id>
Assign public or Elastic IPs to your EC2 instances.
NAT Gateway: Secure Outbound Connectivity
A NAT Gateway allows instances in private subnets to initiate outbound Internet traffic while preventing inbound connections.
Setup steps:
Launch a NAT Gateway in a public subnet.
Update the private subnet’s route table:
Destination:
0.0.0.0/0Target:
nat-<gateway-id>
Instances in the private subnet will use the NAT Gateway for OS updates, API calls, and package downloads without exposing their private IPs.
Warning
Each NAT Gateway incurs an hourly charge and data processing fees. Consider using a NAT instance for low-throughput scenarios.
Introduction to Security Group
AWS Security Groups act as virtual firewalls, controlling both inbound and outbound traffic for your EC2 instances and other resources. In this guide, you’ll learn how to configure security group rules to secure your applications while maintaining the necessary connectivity.
Security Group Analogy
Think of a gated community:
A guard at the entrance logs visitors’ details on arrival and exit.
Only pre-approved guests or those matching specific criteria can enter or leave.
Similarly, a Security Group inspects network packets, allowing only traffic that matches its defined rules.
Scenario Overview
You have an EC2 instance inside a VPC with an attached security group named application-security-group. This group evaluates:
Inbound traffic (requests coming to your instance)
Outbound traffic (requests leaving your instance)
Security Group Rule Components
Every security group rule—whether inbound or outbound—includes:
| Component | Description | Example |
| Protocol | Network protocol (TCP, UDP, ICMP, or all) | TCP |
| Port range | Single or range of ports | 22, 80 or 1024–65535 |
| Source/Dest. | Source CIDR for inbound; destination CIDR for outbound | 203.0.113.0/24 |
Configuring Inbound Rules
Inbound rules control which external systems can reach your instance.
Allow HTTP (port 80) from a specific IP:
aws ec2 authorize-security-group-ingress \ --group-name application-security-group \ --protocol tcp \ --port 80 \ --cidr 121.10.13.141/32Test a connection from
130.67.87.13on port 80 → Rejected (IP not allowed).Open HTTP to the world:
aws ec2 authorize-security-group-ingress \ --group-name application-security-group \ --protocol tcp \ --port 80 \ --cidr 0.0.0.0/0
Warning
Allowing 0.0.0.0/0 exposes your port to the entire Internet. Ensure you only open ports that are strictly necessary.
Configuring Outbound Rules
By default, outbound traffic is fully open:
| Protocol | Port Range | Destination |
| All | All | 0.0.0.0/0 |
To tighten outbound access, specify the protocol, port range, and destination:
aws ec2 revoke-security-group-egress \
--group-name application-security-group \
--protocol all \
--cidr 0.0.0.0/0
aws ec2 authorize-security-group-egress \
--group-name application-security-group \
--protocol tcp \
--port 443 \
--cidr 203.0.113.0/24
Note
Always review both inbound and outbound rules to maintain the principle of least privilege.
Best Practices
Use descriptive security group names (e.g.,
web-sg,db-sg).Limit CIDR ranges to the smallest possible scope.
Regularly audit rules for unused or overly permissive entries.
Combine Security Groups with Network ACLs for layered defense.
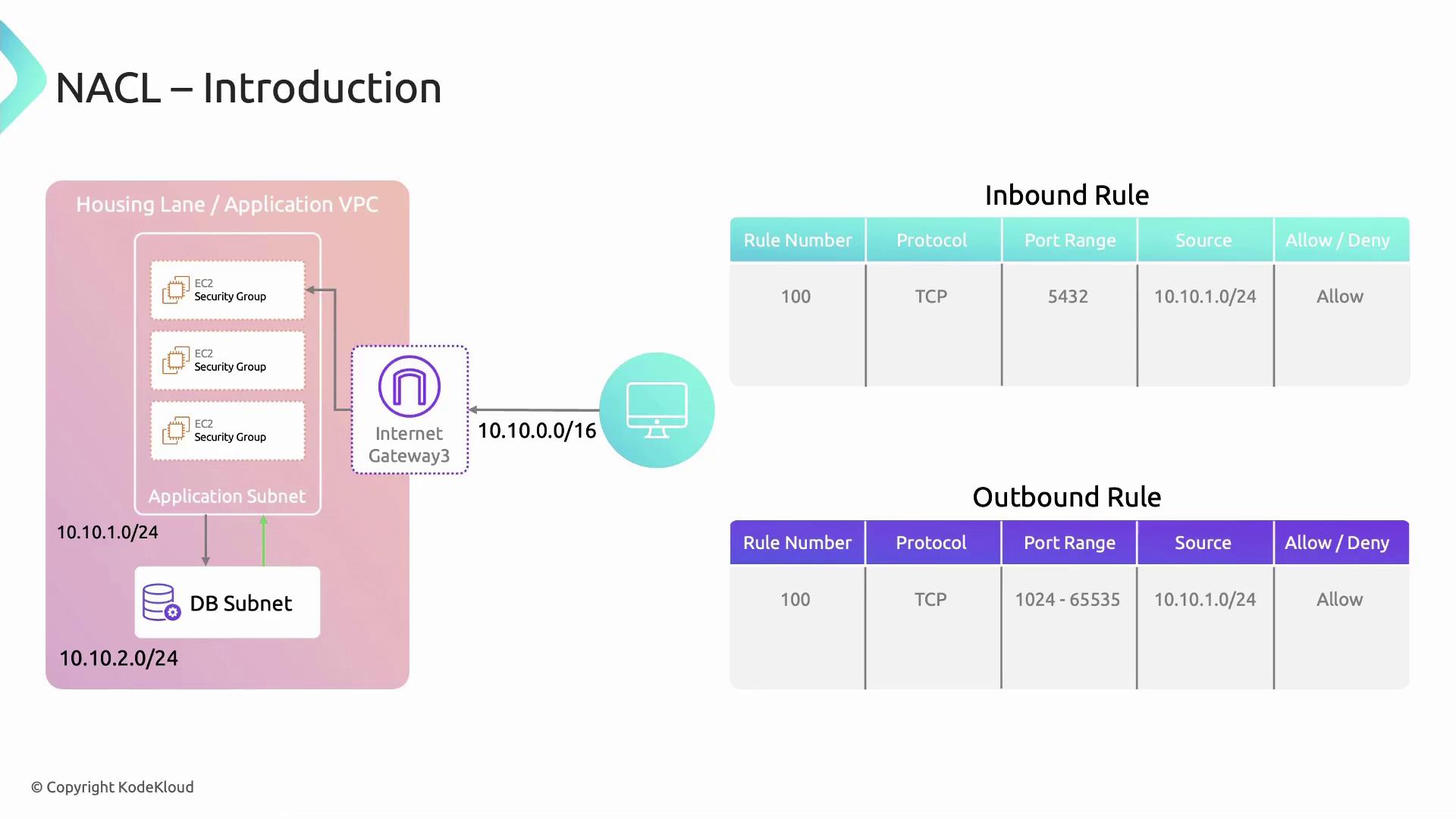
Introduction to NACL
Network Access Control Lists (Network ACLs or NACLs) are an essential network-layer security feature in Amazon VPCs. While Security Groups enforce host-level traffic rules, NACLs apply stateless, subnet-level filters. This makes them ideal for isolating resources—such as placing databases in a separate subnet and only allowing traffic from your application subnet.
Note
Network ACLs are stateless: you must explicitly configure both inbound and outbound rules to allow return traffic. In contrast, Security Groups are stateful and automatically permit responses.
Network ACLs consist of ordered rule entries that either allow or deny specific traffic. Rules are evaluated by ascending rule number, and processing stops when a match is found.
| Field | Description |
| Rule Number | Integer from 1–32,766, determining evaluation order |
| Protocol | TCP, UDP, ICMP or ALL |
| Port Range | Single port or range (e.g., 80 or 1024–65535) |
| CIDR Block | IPv4/IPv6 network (source for inbound, destination for outbound) |
| Action | ALLOW or DENY |
Inbound vs. Outbound Rules
Inbound rules filter traffic entering the subnet.
Outbound rules filter traffic leaving the subnet.
Example: Allowing Ephemeral Port Traffic
In this scenario, an application subnet (10.10.1.0/24) must communicate with a database subnet. We allow TCP traffic on ephemeral ports (1024–65535) and deny all other traffic.
Inbound Rules
Rule # Protocol Port Range Source CIDR Action
100 TCP 1024–65535 10.10.1.0/24 ALLOW
* ALL ALL 0.0.0.0/0 DENY
Outbound Rules
Rule # Protocol Port Range Destination CIDR Action
100 TCP 1024–65535 10.10.1.0/24 ALLOW
* ALL ALL 0.0.0.0/0 DENY
Warning
Always include a catch-all DENY rule (*) to block unwanted traffic. Omitting it can leave your subnet exposed.
Combine Security Groups (stateful) and Network ACLs (stateless) for layered defense.
Use specific rule numbers to group similar rules.
Regularly audit NACL logs via VPC Flow Logs.
Section Summary
Lesson Summary
In this lesson, we explored Amazon Elastic Compute Cloud (EC2), AWS’s core IaaS offering for provisioning and managing virtual servers in the cloud. You learned key EC2 features, pricing models, scalability options, and the fundamental networking components that make up an AWS deployment.
What Is Amazon EC2?
Amazon EC2 (Elastic Compute Cloud) is a web service launched by AWS in 2006 that lets you rent virtual machines—called instances—to run applications without investing in physical hardware or managing your own data center infrastructure. EC2 instances can be resized, scaled, and configured to meet workloads ranging from development environments to high-performance computing.
Key EC2 Features
1. Instance Families
Choose from multiple instance families optimized for different workloads:
| Instance Family | Use Case |
| General-purpose | Balanced CPU, memory, and networking |
| Compute-optimized | High-performance processors for compute-heavy |
| Memory-optimized | Large in-memory databases and caches |
| Storage-optimized | High, local I/O performance |
| Accelerated computing | GPU, FPGA, and machine learning workloads |
Note
Selecting the right instance family ensures optimal performance and cost efficiency for your application.
2. Pricing Models
| Pricing Model | Description |
| On-Demand | Pay per second with no upfront commitment |
| Reserved Instances | Commit to 1–3 years for significant discounts |
| Spot Instances | Bid on spare capacity for up to 90% off—and risk interruptions |
| Savings Plans | Flexible pricing model across compute usage |
3. Scalability & Reliability
On-demand scaling: Launch or terminate instances programmatically.
Auto Scaling: Automatically adjust capacity based on policies and health checks.
Elastic Load Balancing (ELB): Distribute incoming traffic across multiple instances for fault tolerance.
4. High Availability
Spread instances across multiple Availability Zones (AZs) within a Region.
Built-in redundancy and rapid failover.
5. Flexible Configurations
Choose from dozens of operating systems (Linux, Windows) and preconfigured AMIs.
Customize CPU, memory, storage (EBS or instance store), and networking (ENI, IP).
6. AWS Service Integrations
EC2 seamlessly integrates with AWS services, including Amazon S3, AWS Lambda, Amazon RDS, AWS Identity and Access Management (IAM), and Amazon CloudWatch, enabling robust, scalable architectures.
Core Networking Concepts
AWS Account
Your root container for AWS resources, billing, and identity controls.
AWS Region & Availability Zones
Region: A geographical area (e.g., us-east-1) with multiple isolated data centers.
Availability Zone (AZ): An individual data center with its own power and networking setup.
Amazon VPC
A Virtual Private Cloud where you define your own IP address range, subnets, route tables, and gateways.
Subnets
Public Subnet: Instances have direct internet access via an Internet Gateway.
Private Subnet: Instances cannot be reached from the internet without a NAT Gateway or proxy.
Internet Gateway
Attaches to your VPC to enable outbound and inbound internet traffic for public subnets.
NAT Gateway
Provides outbound-only internet access for instances in private subnets, blocking inbound connections.
Route Table
Determines how traffic flows within your VPC and to external networks (Internet Gateway, NAT Gateway, peering connections).
Security Group
Stateful virtual firewall at the instance level that controls inbound and outbound traffic based on rules.
Subscribe to my newsletter
Read articles from Arindam Baidya directly inside your inbox. Subscribe to the newsletter, and don't miss out.
Written by
Arindam Baidya
Arindam Baidya
🚀 Aspiring DevOps & Cloud Engineer | Passionate about Automation, CI/CD, Containers, and Cloud Infrastructure ☁️ I work with Docker, Kubernetes, Jenkins, Terraform, AWS (IAM & S3), Linux, Shell Scripting, and Git to build efficient, scalable, and secure systems. Currently contributing to DevOps-driven projects at Assurex e-Consultant while continuously expanding my skills through hands-on cloud and automation projects. Sharing my learning journey, projects, and tutorials on DevOps, AWS, and cloud technologies to help others grow in their tech careers. 💡 Let’s learn, build, and innovate together!